If the coronavirus has you working from home for the next few weeks, don’t forget about cybersecurity best practices that can help defend against a cyberattack.
Along with the coronavirus upsurge, new “opportunities” have blossomed for cybercriminals in at least two ways. First, the term “coronavirus” is reaching unprecedented levels of search volumes, meaning that malicious developers are updating their toolkits with coronavirus-themed scams, malicious links and sites. A lot of the dangers that employees need to watch out for are detailed in ESET Security Evangelist Tony Anscombe’s blog, Beware scams exploiting coronavirus fears.
Therefore, I will focus here on a second “opportunity” for cybercriminals – the increased number of employees who are working from home and outside of the usual protections of corporate networks. This second vector greatly widens the attack surface on the digital assets of a company and demands a higher responsibility on the part of employees and management alike.
Certainly, for some companies, the infrastructure and security measures to support employees working from home are already in place, but for others, especially smaller businesses, this may not be the case. By taking just a few extra steps, the employees of any company can greatly strengthen their digital security stance against a possible attack while working from home.
Read on for 5 best practice tips:
1. Check your home router’s settings and change the defaults.
Working from home means all your internet traffic passes through your home router. Cybercriminals can attempt to hack your router, intercept your Wi-Fi traffic and ultimately gain access to your network. So, if you haven’t reviewed the configuration options for your home router yet, now is the time – before your home network and connected devices become compromised.
Typically, you can get to your router’s control panel by typing something like 192.168.1.1 in your browser while connected to your home network. From there you can change a lot of settings that have a direct bearing on your security. Make sure to change the default usernames and passwords that come with your router – these can be easily searched online by a hacker.
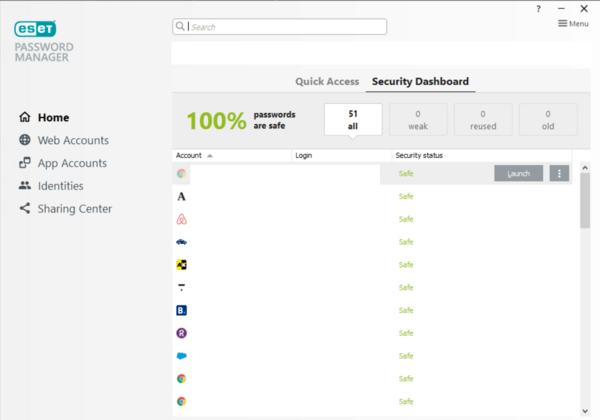
For creating strong and unique passwords, I use ESET Password Manager (part of my ESET Smart Security Premium subscription). Using a password manager is great because I only need to remember one long passphrase – my private keys to the kingdom – and all my other account passwords are easily managed with a few clicks via the Password Manager:
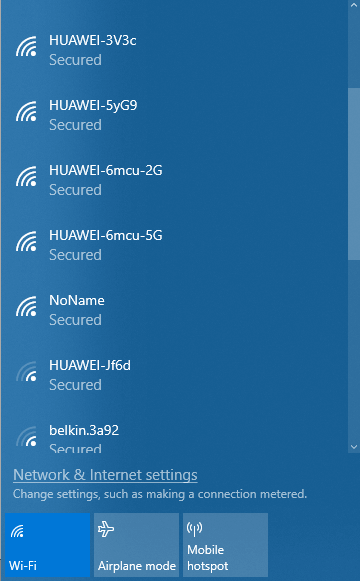
You should also change your SSID – that’s the name of your home network. Looking at the SSIDs of Wi-Fi networks detected from my apartment, a lot of neighbors are apparently using Huawei routers – that’s free information for an attacker:
2. Scan your home network for unwanted devices.
You can also use scanning tools to find unwanted devices on your home network. ESET Smart Security Premium, for example, comes with a Connected Home Monitor scanning tool that can find pesky neighbors who have perhaps been secretly using your Wi-Fi connection without you knowing. Change your password and kick unrecognized devices off your network:

3. Update your home router’s firmware – or stop using a legacy router.
With ESET researchers having recently discovered the KrØØk vulnerability in billions of Wi-Fi chips used in routers, among other devices, it is paramount to ensure the firmware of your home router is updated to the latest version provided by the manufacturer. In fact, if you discover you are using a legacy router, it’s time for a new home router.
If you end up shopping for a new router, look for options that can provide greater security for your home network. In fact, some routers, like those made by Gryphon, incorporate threat intelligence provided by ESET to detect and block malware, phishing sites and other threats at the network level for every router-connected device in your home.
For more information about configuration options for your home router, start with the blog post How to secure your router to prevent IoT threats.
4. Use a virtual private network (VPN) to encrypt your communication.
Employees who need access to a company’s intranet while working remotely will be communicating over insecure public networks. You can better protect that communication by using a VPN that establishes a safe tunnel for the communication to happen.
With a VPN, the small data packets that make up the communication can be kept away from prying eyes, even while travelling across the wider Internet, by only allowing decryption at the ends of the tunnel, i.e., your employees’ devices and your corporate network.
If you don’t have an IT department, you might have to set up your own VPN connections. Don’t worry, it’s not as daunting as you might think – check out this guide on WeLiveSecurity.
5. If you have the option, use two-factor authentication (2FA) to protect your remote access.
Employees who use remote access technologies, like the Remote Desktop Protocol (RDP), are quite open to attack without the proper security and mitigation options in place. Threat actors attack RDP either by social engineering passwords out of employees or by brute-forcing their way in. In other words, the success of attacks against RDP can stem from poor management of the authentication process or from social engineering tricks, among other factors.
Therefore, to better address authentication needs, businesses have the option of using ESET Secure Authentication, ESET’s two-factor authentication (2FA) solution, designed to help doubly secure remote access technologies like VPN and RDP, as well as employee credentials.
The double layer of protection comes from the fact that 2FA requires an employee to enter a one-time code usually delivered via an authentication app (the more secure option) or an SMS, in addition to the usual corporate username and password. Even if an attacker compromises a password, having 2FA in place will prevent unauthorized access.
Looking for a comprehensive set of remote workforce resources for your IT admins and employees?
