The global scale of the recent Exchange server attacks deserves the designation “saga.” The fallout, resulting in data theft and further malware deployment, has likely led to intensive changes in security protocols at thousands of institutions, and will surely be felt for a long time.
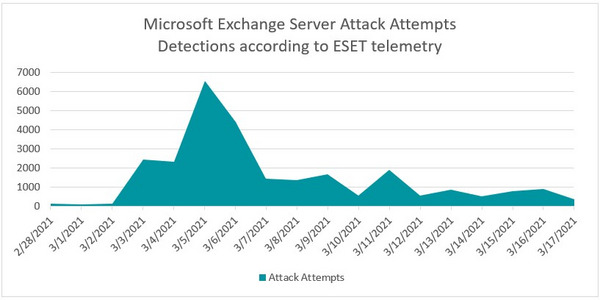
In an update to ESET’s original research piece detailing the global impact of the attacks, ESET’s telemetry picked up almost 27,000 attack attempts via web shells against around 5,500 unique servers:
Along with our well-received research into advanced persistent threat groups leveraging the Exchange vulnerabilities, ESET has set out to provide proactive advice via its Knowledgebase and a Customer Advisory. As the saga moves forward and we continue to compile and analyze data from the networks we protect, we would like to share how our cloud sandbox technology, ESET Dynamic Threat Defense (EDTD), and our endpoint detection and response solution, ESET Enterprise Inspector (EEI), offer protection to our clients.
With respect to malicious files, EDTD not only handles executables (as is the case with ESET LiveGrid®) but also documents, scripts, installers and other file types commonly used to deliver threats. As such, the technology gives greater visibility into, and protection against, various threat types. Leveraging EDTD in combination with endpoint security—both of which are backed by our core detection technologies—brings a multilayered approach to the table that significantly increases the likelihood an attack is automatically detected.
Looking closely at the samples related to the exploitation of Exchange servers, ESET has seen that some of the post-compromise attack components, for example, the loaders for the PlugX RAT (also known as Korplug), are being detected by EDTD when the most sensitive detection threshold – Suspicious – is applied. The same applies to the CobaltStrike-related components.
These kinds of detections also trigger alerts in the ESET Lab, where our researchers are actively monitoring EDTD detection data. The knowledge gained from malware analysis of these samples can then be applied further as we investigate possible intrusion vectors and remediation.
With respect to post-compromise investigation and monitoring of servers, security operations center teams can use ESET Enterprise Inspector to address what amounts to a global challenge.
From the point of view of EEI’s rule set, the current modus operandi of the attackers can be fairly generic, meaning that creating a rule that detects such generic activity—even though possibly malicious—might cause a high number of false positives. For example, it is quite normal for w3wp.exe, the IIS worker process, to execute cmd.exe and powershell.exe, meaning that a rule monitoring this event would flood EEI’s dashboard with false positives.
However, ESET security teams have investigated how EEI faces up against malicious activity following the exploitation of Exchange. Our findings suggest that EEI deployed on exploited servers can cut investigation time by at least 80%.
EEI can not only shorten the time for investigation, but also show the path of attack. Critically, the security admin at EEI’s dashboard would have data at hand to see what was happening, when and where, which is a significant help in identifying and cleaning up malware, as well as providing for the overall security of compromised email servers.
Please follow our blog where ESET will share additional information to help customers return to normal operations following the extensive global exploitation of Exchange.