ESET products stopped WannaCry / WannaCryptor in its tracks: here’s how
When “WannaCry” or “WannaCryptor” hit the world on May 12, people began to panic. Especially those people on the frontlines—IT managers, CISOs, etc.—who are directly responsible for ensuring systems are patched and devices are protected.
However, ESET customers were protected by our our multilayered technology, which had the ability to block the WannaCry malware and prevent it from spreading—something not all the other security vendors were able to do. How was ESET able to do this?
ESET security solutions use multiple protective technologies:
ESET Network Attack Protection constitutes an important layer of protection against WannaCryptor. The technology blocked the NSA-originated exploit (known as EternalBlue) used to spread WannaCryptor.D at the network level.

ESET DNA Detections can identify specific known malware samples and their variants or even previously unseen or unknown malware which contains genes that indicate malicious behavior. In this case, the DNA Detection technology identified and blocked WannaCryptor.D files.
ESET Advanced Memory Scanner stepped in to detect and block activity of WannaCryptor.D at the memory level.
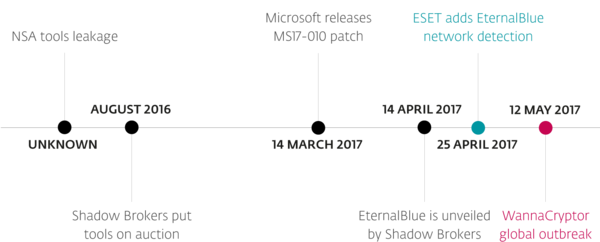
Attempts to exploit the leaked vulnerability had been detected, reported on, and stopped well before the outbreak of WannaCry—because ESET’s network detection of the EternalBlue exploit was added on April 25. On Friday, May 12, ESET increased the protection level for the WannaCry threat via updates to the detection engine. (For more information on ESET products that prevent a WannaCry infection, view our Customer Advisory.)
How does the attack work?
When WannaCry infiltrates a user’s computer, it encrypts its files and instructs the victim to pay in Bitcoin in order to retrieve those files. The ransom demanded for decryption of the files appears to be about $300. It then uses the EternalBlue exploit to access other unpatched machines in the network as well as online. (For a real-time check of the amounts that the malicious actors have received in Bitcoin funds, go here.)
Reports of WannaCry started in Spain’s telecom sector and quickly spread from that point to healthcare organizations in the U.K., various commercial websites, entire enterprise sites, and just about every type of network in between. People from around the world posted screenshots of the malware from computers in offices, to hospitals and schools.
What should you do to stay protected?
Attacks using the EternalBlue exploit had been appearing even before the surge of WannaCry, spreading an off-the-shelf cryptocurrency mining software , and we believe these threats are still very real. Please follow these steps to help keep your business protected in the wake of WannaCry.
- Ensure your Windows machines are up to date: Patches can be difficult to deploy across the entire network. However, you’ll want to install this one. It has been available since mid-April and actually stops the exploit from gaining a foothold in your environment. The patch listing for the entire listing of the Equation Group files can be located here.
- Use anti-malware software: This is a basic but critical component. Just because it’s a server, and it has a firewall, does not mean it does not need anti-malware: it does. Always install a reputable anti-malware program. (And one that protects against the EternalBlue exploit.)
- Back up files: For companies hit by ransomware that do have current backups, the attack is not nearly as damaging. Make sure you always back up data, and regularly check to make sure your backup systems are working properly.
- Don’t pay up: We recommend that users don’t pay the ransom – be it in the case of WannaCry or any other ransomware. The much-repeated advice is now even more convincing seeing as there appears to be no reliable way for the attackers to match victims to payments and decrypt their files.
ESET, a leader in proactive endpoint security for 30 years, protects more than 100 million users worldwide. Unlike some of our competitors, ESET includes ransomware protection in all our products at no extra charge.