1bn+
users worldwide
400k+
business customers
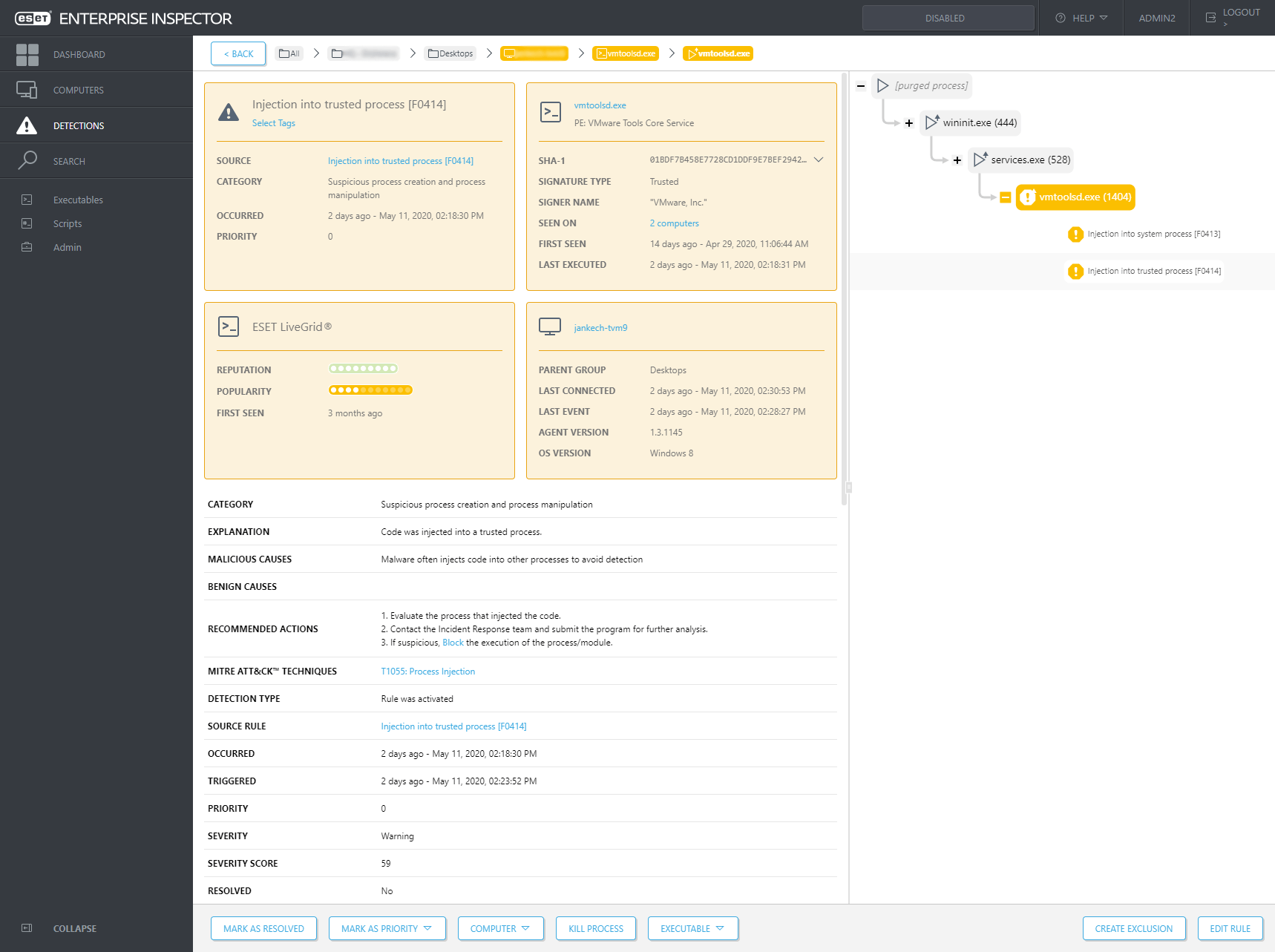
ESET Enterprise Inspector
Endpoint Detection and Response tool from ESET that enables continuous comprehensive monitoring of real-time endpoint activity, in-depth analysis of suspicious processes and immediate response to incidents and breeches. Paired with ESET Endpoint Protection Platform, ESET Enterprise Inspector is a complete prevention, detection and remediation solution to:

Detect advanced persistent threats

Stop file less attacks

Block zero-day threats

Protect against ransomware

Prevent company policy violation
Open architecture & integrations
ESET Enterprise Inspector provides a unique behavior and reputation based detection that is fully transparent to security teams. All rules are easily editable via XML to allow fine-tuning or easily created to match the needs of specific enterprise environments, including SIEM integrations.
Public API
ESET Enterprise Inspector features an API that enables accessing and exporting of detections, and their remediation to allow effective integration with tools such as SIEM, SOAR, ticketing tools and many others.
MITRE ATT&CK™
ESET Enterprise Inspector references its detections to the MITRE Adversarial Tactics, Techniques, and Common Knowledge (ATT&CK™) framework, which in one click provides you with comprehensive information even about the most complex threats.
Remote access
ESET Enterprise Inspector features remote PowerShell capabilities that allow Security Engineers to remotely inspect and configure their organization’s computers, so a sophisticated response can be achieved without breaking the user’s workflow.
Multiplatform
ESET Enterprise Inspector supports Windows and MacOS, which makes it a perfect choice for multiplatform environments.
Use cases
PROBLEM
Threat Hunting & Blocking
Your early warning system or Security Operation Center (SOC) delivers a new threat warning. What are your next steps?
SOLUTION
- Leverage early warning system to retrieve data on upcoming or new threats.
- Search all computers for existence of new threat.
- Search all computers for indicators of compromise that threat existed prior to warning.
- Block threat from being able to infiltrate network or execute within organization.

protected by ESET since 2017
more than 9,000 endpoints
protected by ESET since 2016
more than 32,000 endpoints
The ESET difference
Threat Hunting
Apply data filters to sort it based on file popularity, reputation, digital signature, behavior or contextual information. Setting up multiple filters allows automated easy threat hunting, including APTs and targeted attacks which is customizable to each company’s environment. By adjusting behavior rules, ESET Enterprise Inspector can be customized also for Historic Threat Hunting and “rescan” the entire events database.
Investigation and Remediation
Use a built-in set of rules or create your own rules to respond to detected incidents. Each triggered alarm features a proposed next step to be performed for remediation. This quick response functionality helps to ensure that any single incident will not fall through the cracks.
Anomaly and behavior detection
Check actions that were carried out by an executable and utilize ESET’s LiveGrid® Reputation system to quickly assess if executed processes are safe or suspicious. Monitoring anomalous user-related incidents are possible due to specific rules written to be triggered by behavior, not simple malware or signature detections. Grouping of computers by user or department allows security teams to identify if the user is entitled to perform a specific action or not.
Company Policy Violation
Block malicious modules from being executed on any computer in your organization’s network. ESET Enterprise Inspector’s open architecture offers the flexibility to detect violations of policies about using specific software like torrent applications, cloud storages, tor browsing or other unwanted software.
One-click isolation
Define network access policies to quickly stop malware’s lateral movements. Isolate a compromised device from the network by just one click in the EEI interface. Also, easily remove the devices from the containment state.
Scoring
Prioritize the severity of alarms with scoring functionality that attributes a severity value to incidents and allows the admin to easily identify computers with a higher probability of a potential incident.
Tagging
Assign and unassign tags for fast filtering to EEI objects such as computers, alarms, exclusions, tasks, executables, processes and scripts. Tags are shared among users, and once created, they can be assigned within seconds.

ESET is compliant with ISO/IEC 27001:2013 - an internationally recognized and applicable security standard in implementing and managing information security. See the certificate.

ESET demonstrates ability to consistently provide products and services that meet customer and regulatory requirements for a quality management system (QMS) in compliance with ISO 9001:2015. See the certificate.
The certification is granted by the third-party accredited certification body SGS and demonstrates ESET full compliance with industry leading best practices.
Explore our customized solutions
Please leave us your contact details so we can design a personalized offer to fit your requirements.
No commitment.
Discover additional services complementing ESET Enterprise Inspector
ESET Deployment & Upgrade
ESET professionals install and configure ESET products in your environment and train your organization to ensure a successful deployment/upgrade.
ESET Threat Monitoring
ESET experts constantly monitor your network and endpoint security, alerting you in real time when something suspicious needs your attention.
ESET Threat Hunting
ESET experts help customers investigate data, events and alarms generated by ESET Enterprise Inspector including root cause analyses, forensic investigation and actionable mitigation advice.
Looking for the complete security of your network?
Related enterprise-grade solutions
ESET Targeted Attack Protection
- Security Management Center
- Endpoint Protection Platform
- Cloud Sandbox Analysis
- Endpoint Detection & Response

ESET Dynamic Mail Protection
- Security Management Center
- Mail Security
- Cloud Sandbox Analysis
Related products and services
- ESET Endpoint Security
Award-winning multilayered technology combining machine learning, big data and human expertise. - ESET Dynamic Threat Defense
Cloud-based sandboxing technology that detects never before seen or zero-day threats. - ESET Deployment & Upgrade
Fast, seamless customer support for all new deployments or upgrades.