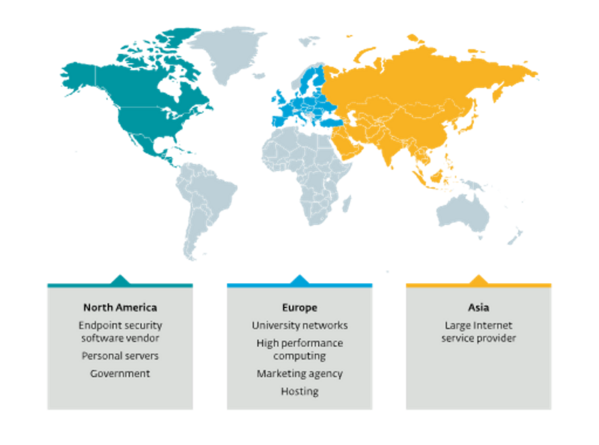
BRATISLAVA, MONTREAL – ESET researchers discovered Kobalos, a malware that has been attacking supercomputers – high performance computer (HPC) clusters. ESET has worked with the CERN Computer Security Team and other organizations involved in mitigating attacks on these scientific research networks. Among other targets was a large Asian ISP, a North American endpoint security vendor as well as several privately held servers.
ESET researchers have reverse engineered this small, yet complex malware that is portable to many operating systems including Linux, BSD, Solaris, and possibly AIX and Windows. “We have named this malware Kobalos for its tiny code size and many tricks; in Greek mythology, a kobalos is a small, mischievous creature,” explains Marc-Etienne Léveillé, who investigated Kobalos. “It has to be said that this level of sophistication is only rarely seen in Linux malware,” adds Léveillé.
Kobalos is a backdoor containing broad commands that don’t reveal the intent of the attackers. “In short, Kobalos grants remote access to the file system, provides the ability to spawn terminal sessions, and allows proxying connections to other Kobalos-infected servers,” says Léveillé.
Any server compromised by Kobalos can be turned into a Command & Control (C&C) server by the operators sending a single command. As the C&C server IP addresses and ports are hardcoded into the executable, the operators can then generate new Kobalos samples that use this new C&C server. In addition, in most systems compromised by Kobalos, the client for secure communication (SSH) is compromised to steal credentials.
“Anyone using the SSH client of a compromised machine will have their credentials captured. Those credentials can then be used by the attackers to install Kobalos on the newly discovered server later,”
adds Léveillé. Setting up two-factor authentication for connecting to SSH servers will mitigate the threat, since the use of stolen credentials seems to be one of the ways it is able to propagate to different systems.
For more technical details about Kobalos, read the blogpost “Kobalos – A complex Linux threat to high performance computing infrastructure” on WeLiveSecurity. Make sure to follow ESET Research on Twitter for the latest news from ESET Research.
Industry and region of compromised organizations
For 30 years, has been developing industry-leading IT security software and services for businesses and consumers worldwide. With solutions ranging from endpoint and mobile security, to encryption and two-factor authentication, ESET’s high-performing, easy-to-use products give consumers and businesses the peace of mind to enjoy the full potential of their technology. ESET unobtrusively protects and monitors 24/7, updating defenses in real-time to keep users safe and businesses running without interruption. Evolving threats require an evolving IT security company. Backed by R&D centers worldwide, ESET becomes the first IT security company to earn awards, identifying every single “in-the-wild” malware without interruption since 2003. For more information visit or follow us on , and.
