Why do customers appreciate our identity and data protection?
Data breaches prevention
Minimize risks of business continuity disruptions and ensure the organization and its data are protected anywhere and anytime.
Fast seamless deployment
Whether encryption or authentication, both solutions are tailored to keep setup time to the absolute minimum.
Regulatory compliance
Meet legal requirements and regulations such as GDPR, CCPA, LGPD, or POPI.
Common use cases
Worried about
Data breaches?
Businesses appear in the news every single day to alert their customers that a data breach has occurred.
Worried about
Managing remote employees?
Companies need the ability to protect sensitive data in the case of employee termination or when devices are lost or stolen.
Worried about
Data leakage?
Every company uses removable media devices to move data from one computer to another, but most companies do not have a way to verify that the data is staying only on company devices.
Worried about
Verifying user login?
Businesses use shared computers in shared workspaces and require verification of all parties logging in throughout the workday
Worried about
Weak passwords?
Users tend to employ the same passwords across multiple applications and web services, thus putting businesses at risk
Worried about
Insider threats?
Insider threats are on the rise, and they may take months to discover. They are driven by digital workspaces, remote work, and the agile behavior of companies without strict policies.
What makes our solutions a perfect fit for your needs?
Encryption
Identity and data protection
ESET Full Disk Encryption
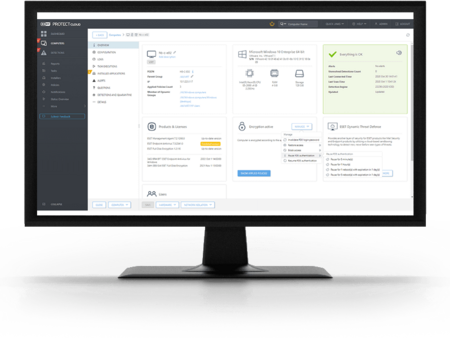
A powerful encryption managed natively by ESET remote management console. It increases your organization's data security that meets compliance regulations.
- Encrypt system disks, partitions or entire drives
- Manage from ESET PROTECT Console
- Deploy, activate and encrypt devices in a single action
See interactive demo or start a free trial
Explore ESET Full Disk Encryption features
All products managed from one console
ESET Full Disk Encryption works within the ESET PROTECT console, helping administrators to save time thanks to familiarity with the existing management environment and concepts.
Fully validated
Patented technology to protect data for businesses of all sizes. ESET Full Disk Encryption is FIPS 140-2 validated with 256 bit AES encryption.
Powerful encryption
ESET Full Disk Encryption encrypts system disks, partitions and entire drives to ensure that everything stored on each PC or laptop is locked down and secure, protecting you against loss or theft.
Cross-platform coverage
Manage encryption on Windows machines and native macOS encryption (FileVault) from a single dashboard.
Single-click deployment
Manage full disk encryption across your entire network from a cloud‑based console. ESET PROTECT single pane of glass allows admins to deploy, activate and manage encryption on their connected endpoints with a single click.
Add additional devices at any time
You can increase the number of devices covered by your license at any time.
System requirements
Supported operating systems:
- Microsoft Windows 7, 8, 8.1, 10
- macOS 10.14 (Mojave) and higher
Requirements
- deployed ESET PROTECT console in cloud or on-premises
Encryption
Identity and data protection
ESET Endpoint Encryption
A simple to use standalone encryption solution providing full remote control of endpoint encryption keys and security policy for files on hard drives, portable devices and emails. Ensures:
- Zero data breaches
- Meet compliance requirements
- Seamless encryption
Explore ESET Endpoint Encryption features
Fully validated
Patented technology to protect data for businesses of all sizes. ESET Endpoint Encryption is FIPS 140-2 validated with 256 bit AES encryption.
No server required
ESET Endpoint Encryption requires no server for deployment and can seamlessly support remote users.
Cross-platform coverage
Manage encryption on Windows machines and native macOS encryption (FileVault) from a single dashboard.
Granular data protection
ESET Endpoint Encryption gives companies enhanced ability to protect specific files, folders, virtual disks or archives.
Protect data in transit
By encrypting emails and attachments, and restricting access to removable media for specific users, you can protect data in transit and prevent their leakage outside the company.
Centralized management
Full control of licensing and software features, security policy and encryption keys from a dedicated ESET Endpoint Encryption console.
System requirements
Supported operating system
Client OS: Windows 11, 10, 8.1, 8, 7, macOS 10.14 (Mojave) and higher
Server OS: Windows Server 2022, 2019, 2016, 2012 R2, 2012, 2008 R2
Authentication
Identity and data protection
ESET Secure Authentication
An easy-to-use and effective mobile-based multi-factor authentication (MFA) solution that protects organizations from weak passwords and unauthorized access.
- Prevent data breaches
- Meet compliance requirements
- Manage centrally from your browser
- Use your phone, or HW tokens
Explore ESET Secure Authentication features
MFA made easy
Authentication is easy: just answer a prompt sent to your phone. Works on iOS and Android devices, and for all platforms and services.
Multiple ways to authenticate
ESET Secure Authentication supports mobile applications, push notifications, hardware tokens, FIDO security keys, as well as custom methods.
Cloud support
In addition to on-premises applications, ESET Secure Authentication also supports web/cloud services such as Office 365, Google Apps, Dropbox and many others, via ADFS 3.0 or SAML protocol integration.
Remote management
ESET Secure Authentication uses its own streamlined management console accessible via a web browser.
10-minute setup
The aim was to create an application that a small business with no IT staff at all could set up and configure.
No dedicated hardware required
All the costs of ESET Secure Authentication are built in so no dedicated hardware is necessary. Simply install the solution on a server and start provisioning.
System requirements
- Server side:
32 and 64-bit versions of Microsoft Windows Server 2008, 2008 R2, 2012, 2012 R2, 2016, 2012 Essentials, 2012 R2 Essentials, 2016, 2016 Essentials, 2019, 2019 Essentials, Small Business Server 2008 & 2011 - Client side:
iOS (iPhone), Android, Windows 10 Mobile - Hardware token support: While the solution doesn't require HW tokens to work, it supports all event-based HOTP tokens that are OATH-compliant, TOTP tokens, as well as FIDO2 and FIDO U2F hardware keys
Киберзащита на световно ниво

Печелим уважението на специалисти и анализатори

Награждават ни в независими тестове
Заслужаваме доверието на клиенти от България и света
Purchase your identity and data protection today
ESET's identity and data protection is available in the following solutions
Best-in-class endpoint protection against ransomware & zero-day threats, backed by powerful data security.
Encryption
All included components:
- Management Console
- Endpoint Protection
- File Server Security
- Full Disk Encryption
- Advanced Threat Defense
- Mail Security
- Cloud App Protection
- Extended Detection & Response
Complete, multilayered protection for endpoints, cloud applications & email, the #1 threat vector.
Encryption
All included components:
- Management Console
- Endpoint Protection
- File Server Security
- Full Disk Encryption
- Advanced Threat Defense
- Mail Security
- Cloud App Protection
- Extended Detection & Response
Powerful two-factor authentication for safe access to networks and data.
Multi-factor authentication
- Prevent data breaches
- Meet compliance requirements
- Manage centrally from your browser
- Use your phone or HW tokens
Extended detection and response (XDR) that delivers enterprise-grade visibility, threat hunting and response options.
Encryption
All included components:
- Management Console
- Endpoint Protection
- File Server Security
- Full Disk Encryption
- Advanced Threat Defense
- Mail Security
- Cloud App Protection
- Extended Detection & Response
Simple and powerful encryption for organizations of all sizes.
Encryption
- Full disk encryption
- Removable media encryption
- File and folder encryption
- Virtual disks and encrypted archives
- Centralized management compatible
ESET Technology Alliance solutions
Data Loss Prevention & Insider Threat Protection
Identity and data protection
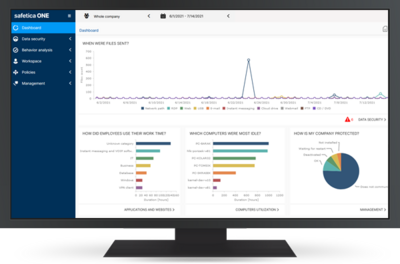
Safetica
Protect your company valuable assets against data loss,
theft or malicious attacks.
- Tough on insider threats and data loss
- Easy on users and infrastructure
- Protects data in hybrid work era
- Supports regulatory compliance
Explore Safetica solutions
Safetica ONE
Enterprise-grade on-prem DLP covering a full range of security scenarios with a focus on data protection, workspace audit, and business productivity.
Safetica NXT
Next-gen SaaS DLP focused on core data security scenarios, maximum simplicity and automation based on best practices.
System requirements
Supported operating systems
- Microsoft Windows 7, 8.1, 10, 11 (32-bit [x86] or 64-bit [x64]), MSI installation package, .NET 4.7.2 and higher
- macOS 10.10 and higher (for full DLP feature set recommend 10.15 and higher)
- Android 6+ and Google Play Services
- iOS 10+
- Windows Server 2012 and higher
Hardware requirements
- Endpoints: 2.4 GHz dual-core processor, 2 GB RAM and more, 10 GB of available disk space
- Server: 2.4 GHz quad-core processor, 8 GB RAM and more, 100 GB of available disk space, a shared or dedicated server, support of virtual machines and cloud hosting.
- Requires connection to server with MS SQL 2012 and higher or Azure SQL
Backup and recovery
Xopero
Total protection, backup and recovery of your business data onsite or in the cloud. Advanced cloud backup for computers, servers and virtual environment, Xopero offers comprehensive data. Benefit from:
- Complete protection for critical files
- Control over all backups
- Easy to use and cost savings
- Remote management