With ransomware booming on the threat landscape, the rising number of lock‑and‑extort attacks highlights another dangerous trend – the increasing prevalence of EDR (Endpoint Detection and Response) killers, malware designed to shut down cybersecurity defenses.
The way these enhanced ransomware attacks unfold poses a challenge for businesses, no matter how sophisticated their cybersecurity solutions may be. Organizations cannot rely solely on automated malware hunting or aggressive blacklisting of vulnerable drivers, which EDR killers frequently abuse. Even a skilled Security Operation Center (SOC) team may struggle to stop an advanced ransomware breach, as they must act appropriately, quickly, and with enough authority – leaving no room for error.
ESET’s recent research, grounded in telemetry and incident investigations, underscores a simple truth: if your defense strategy only focuses on blocking vulnerable drivers at load time, you’re reacting too late. A cyber threat intelligence‑led approach is how you stay ahead – by anticipating the tools, playbooks, and pivot points affiliates will use against you.
Key points of this article:
- Ransomware actors increasingly rely on EDR‑killing tools – especially those abusing vulnerable drivers – to disable endpoint protection right before launching malicious encryption.
- These tools are cheap, accessible, and require little technical skill from attackers.
- Businesses cannot rely on automated defenses, since they are dealing with a human attacker on the other end who reacts to obstacles, and simply blocking vulnerable drivers is not an easy task, as it might break legitimate software.
- Effective protection requires layered strategies beyond detection. When combined with cyber threat intelligence, these strategies can reveal active campaigns and help defenders predict and prepare for attacks.
Why ransomware groups use EDR killers
Ransomware is not new, but after reaching a certain level of sophistication, it has become a widely purchased as a service on the black market. ESET researchers regularly track and defend against an increasing number of “customers” of various ransomware as service offerings.
The numbers are alarming – ESET analysis of data leak sites indicates a steep 50% year-on-year increase in ransomware attacks. Verizon’s 2025 Data Breach Investigations Report confirms the trend with a year-over-year increase in ransomware attacks from 32% to 44%, noting that 88% of breached SMBs found ransomware in their systems.
However, ransomware does have one major weakness: it’s noisy by design. Encryptors touch thousands of files quickly, triggering hooks and attracting the attention of any reliable security solution or service.
Cybercriminals can overcome this problem using various obfuscation techniques, but those are not 100% reliable, and constant development/updating consumes a lot of time and resources.
Sadly, ransomware crews have found an effective workaround: they discovered that they don’t need stealthy, hard-to-develop encryptors to win; they just need business defenses to blink. That’s why EDR killers have become an almost standard midpoint indicator of modern ransomware intrusions: an affiliate gains high privileges, runs a tool to disrupt endpoint protection, and only then unleashes the encryptor.
Usually, attackers use the technique known as Bring Your Own Vulnerable Driver (BYOVD), abusing legitimate but vulnerable (usually older) drivers to access the kernel of a targeted operating system. Once a vulnerable driver is installed, malware iterates over a list of process names and issues a command to the vulnerable driver to kill the process, abusing the driver’s access to the kernel.
What makes the situation even worse is that EDR killers are accessible, cheap, and increasingly “plug-and-play” because they often rely on legitimate yet vulnerable drivers, and there are large collections of publicly available proofs of concept (PoCs).
In short: cybercriminals enjoy a comfortable environment, where everything they need is available as a service, which significantly lowers the skill level required for deploying ransomware campaigns. They simply buy ransomware on the black market and deploy it silently using affordable yet powerful tools with kernel‑level impact – effectively avoiding traditional defenses.
How do EDR killers work?
Before we dive into prevention, let’s briefly see how different kinds of EDR killers operate.
Script-based EDR killers
The simplest EDR killers rely on built in administrative tools such as “taskkill” to tamper with security processes and services. These basic methods still appear but are mostly associated with lower skill threat actors.
Safe Mode content currently inside Scripts block
A slightly more advanced variant uses Windows Safe Mode, where only minimal system components load and security products are usually absent. While this increases the chance of disabling protection, it requires a reboot, creates noise, and is unreliable in unfamiliar environments, making it rare in real world attacks.
Misused anti-rootkit tools
Before kernel mode driver signing was enforced, rootkits were common, therefore specialized anti rootkit tools were created to detect and remove them. Because these tools operate with high privileges, attackers can misuse legitimate anti-rootkits to terminate protected processes or disable security components.
Rootkit-based EDR killers
Rootkits are far less common today, but still appear when developed by mature cybercriminals via custom Windows drivers – a complex task especially without breaking the system altogether. For example, Rootkit-based EDR killers can abuse stolen legitimate certificates to run a malicious driver in the kernel where they can disable endpoint protection.
BYOVD-based EDR killers
The BYOVD technique is now the dominant approach for EDR killers. Attackers install a legitimate driver that contains a known vulnerability, then exploit that flaw to terminate protected processes or disable key security callbacks.
ESET researchers detect a total of almost 90 EDR killers actively used in the wild, 54 of them are BYOVD-based (abusing a total of 35 vulnerable drivers).
Driverless EDR killers
A newer class of EDR killers achieves similar aims without touching the kernel. Instead of terminating processes, these tools disrupt essential EDR functionality – for example, by blocking communication between an endpoint and its security backend or causing EDR components to become unresponsive. Their unconventional approach makes detection more challenging and encourages quick adoption by ransomware attackers – a trend already seen by ESET researchers.
How to detect EDR killer activity before ransomware launches
While BYOVD remains dominant, it’s clear that focusing solely on drivers breeds false confidence and faulty attribution. Here is why:
- Blocking a driver happens only at the very last possible moment, when affiliates typically already have high privileges and are seconds away from launching the encryptor. If the EDR killer fails, they will simply try another tool.
- BYOVD attacks use legitimate drivers, and overly aggressive blocking may lead to business disruption of legacy or enterprise software.
- argeted driver blocking is problematic on its own, as different approaches have different weaknesses, and threat actors are known to find ways to circumvent these policies.
How to defend against EDR killers
Careful driver load blocking – Blocking drivers is crucial and, indeed, an effective way to stop EDR killers, but keep in mind that there are serious challenges. To avoid system disruption, consider starting with a “Detect but don’t clean” mode, then adding exclusions as needed, and finally switching to a “Detect and clean” mode.
Enforce HVCI and driver-signing controls – These include Microsoft’s blocklist, enforced driver signing, and HVCI.
Use WDAC or equivalent application control – Tools like Windows Defender Application Control (WDAC) allow policies that approve only selected drivers. Other platforms use technologies like ESET’s Host‑based Intrusion Prevention System (HIPS), which blocks applications via rules.
Protect your EDR – EDR self‑protection and anti‑tamper features prevent unauthorized users from meddling with your security solution.
Patch or remove vulnerable drivers already present – There is no need to use BYOVD technique if your systems already use a vulnerable driver. Thorough patch management should prevent that.
Deploy a skilled SOC team or XDR – When automated defense is not enough, fast and right response is necessary.
Monitoring EDR‑specific attack behaviors
An important part of defense is detection of the patterns EDR killers typically generate.
Here are alerts you need to watch for:
- Unexpected attempts to modify services
- Loading of drivers from temporary or user directories
- Changes to Safe Mode boot settings
- PowerShell running with high privileges
- Sudden EDR process instability or silence
- Sysmon or Windows logs related to driver installation
Why threat intelligence matters for EDR-killer defense
As you can see, the nature of EDR killers makes traditional automated signatured-based protection insufficient. EDR killers are simply too unpredictable for automated protection, and a catch-all strategy will likely disable legitimate drivers, possibly crippling your business’s operations.
The answer to this situation is high-quality MDR that can quickly respond to incidents, complemented by curated, information-rich threat intelligence, both of which allow defenders to see the EDR killers that are currently actively deployed and anticipate possible attacks.
Here is how threat intelligence can help you:
- It gives you an overview of recent ransomware campaigns.
- It provides strategic insights into targeting patterns, attack progression, lessons learned, and IoCs .
- echnical analysis describes the full attack chain – from initial access to data encryption and extortion.
- It offers actionable guidance on how to defend against current ransomware threats in the wild.
- A threat intelligence feed provides a continuously updated stream of curated data that helps security teams identify threats.
- Advanced threat intelligence services come with AI chatbots, helping security analysts and decision-makers to correctly interpret incidents and act quickly.
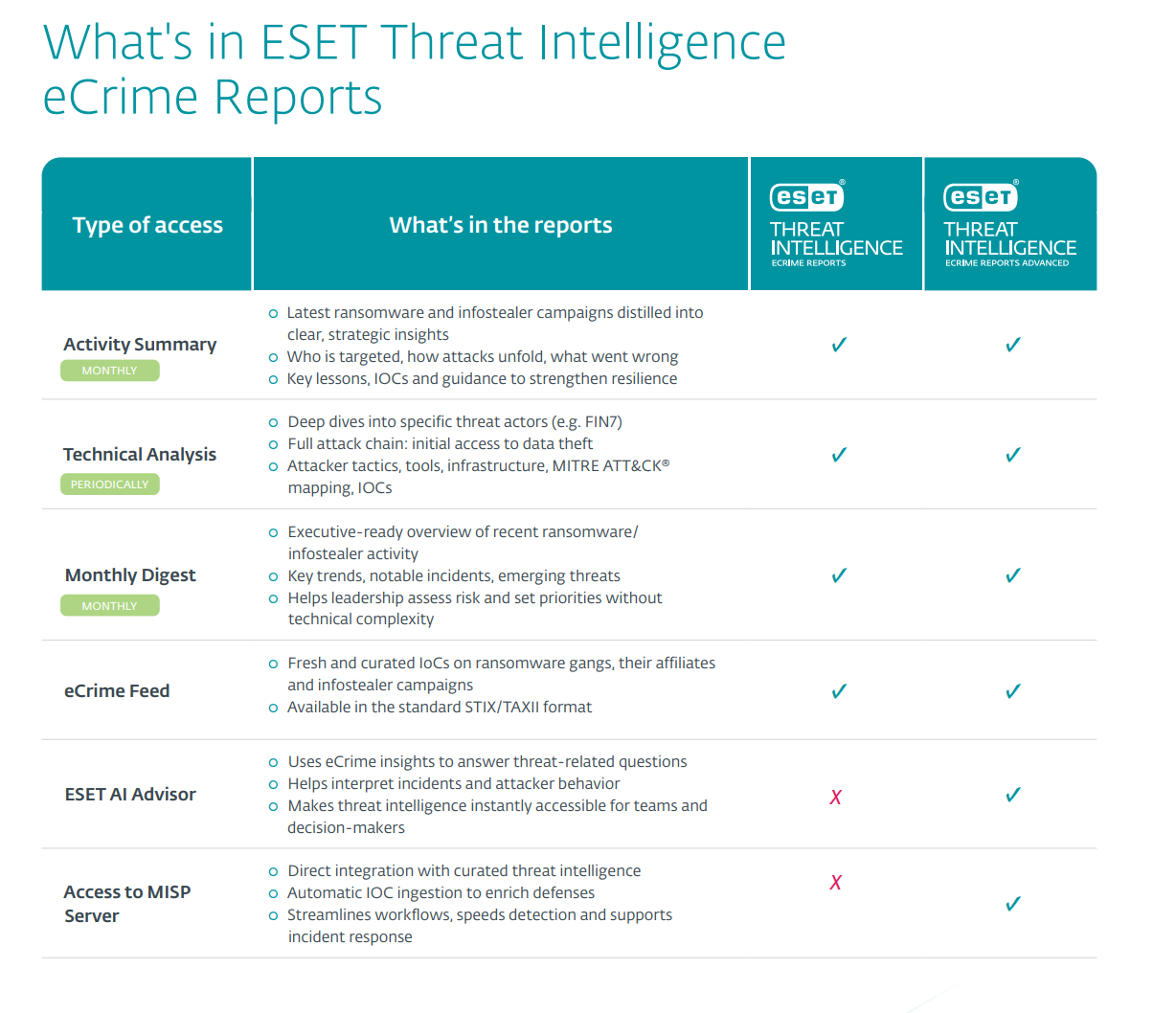
To give security teams a strategic edge against modern cybercriminal groups, ESET has recently extended its threat intelligence portfolio with ESET eCrime Reports that provide security teams with curated, high‑quality insights into incidents, including key lessons, IoCs, hunting rules, and guidance, to predict attacks, close gaps, and strengthen defenses proactively.
Facing ransomware in the AI era
The days when businesses just installed cybersecurity products and put any thoughts of threats behind them are gone. Cybercrime is booming, with an increasing amount of malware delivered as a service. This means that lower skills are required to operate malicious campaigns, and AI tools are making everything even easier and faster for bad actors.
In this threat landscape, EDR killers shine because they’re cheap and let attackers focus on speed, as they already possess a reliable pre-encryption knockout punch. If you only sound the alarm at load time, you’re only meeting the adversary at the final gate — when they already hold admin privileges and momentum.
A mature threat intelligence service changes that. It reframes the problem from “block a driver” to “break the process,” tying intelligence about affiliates, commercialization trends, and user-mode evasion into concrete detections, faster authority to act, and precise response. That’s how you convert research into resilience — and ensure that your EDR is online when it matters most.
Frequently Asked Questions (FAQs)
What are EDR killers, and why are they important in modern ransomware attacks?
EDR killers are tools or malware designed to disable or disrupt endpoint detection and response (EDR) solutions. They help ransomware operators avoid detection before launching encryptors, making attacks far more effective and difficult to stop.
Why have EDR killers become the default step in ransomware intrusions?
Ransomware encryptors are noisy and easy to detect. Instead of trying to make stealthy encryptors, attackers use EDR killers to blind defenses first. These tools are cheap, accessible, and often built around vulnerable but legitimate drivers, making them a fast, reliable way to evade security products.
How do EDR killers typically work?
EDR killers use different approaches, such as:
- Simple scripts that terminate security services
- Abusing Safe Mode to disable protection
- Misusing anti-rootkits or rootkits
- Bring Your Own Vulnerable Driver (BYOVD) techniques
- Emerging driverless methods that disrupt EDRs without kernel-level access
Why is blocking vulnerable drivers alone not enough to stop EDR killers?
Blocking driver loads happens too late in the attack chain, when attackers already have high privileges. Overly aggressive blocking can also break legitimate software, and attackers can easily generate thousands of variants using the same vulnerable driver or certificate.
What are effective strategies for defending against EDR killers?
Key defense measures include careful driver-blocking policies, hardened application control (e.g., WDAC, HIPS rules), strong EDR self‑protection and anti-tamper features, proper vulnerability and patch management, SOC or XDR support, and monitoring for EDR‑killer behavior patterns.
Why is cyber threat intelligence essential against EDR killers and ransomware?
EDR killers evolve quickly, making ransomware attacks unpredictable. High‑quality threat intelligence helps organizations anticipate which tools, techniques, and ransomware families are active, understand full attack chains, and apply meaningful defensive measures before attackers strike.
What is BYOVD?
Bring Your Own Vulnerable Driver (BYOVD) is an attack technique in which an attacker intentionally loads a legitimately signed but flawed kernel-mode driver to a victim’s system to gain high-privilege code execution. Once in the kernel, attackers can tamper with operating system internals and security products, which is why BYOVD is frequently used by EDR killers. However, EDR killers cannot reliably disable all security software in every environment: success depends on the specific vulnerable driver used, existing mitigations, and the architecture of security tools .
Is Microsoft’s vulnerable driver blocklist enough to stop BYOVD?
The blocklist is inherently reactive, cannot instantly cover newly discovered or privately traded vulnerabilities, and can be bypassed in environments where it is disabled, outdated, or misconfigured.
What should defenders monitor for if they suspect an EDR killer?
If defenders suspect the presence of an EDR killer, they should monitor for abnormal driver load events, especially newly introduced or rarely seen kernel drivers. Further, they should check for unexpected attempts to modify services, attempts to disable or manipulate kernel callbacks, and sudden loss of telemetry or agent crashes without corresponding system failures. Kernel integrity violations, repeated service restarts, or unexpected changes to security product state are also strong signals.
What is the difference between EDR evasion and an EDR killer?
EDR evasion focuses on avoiding detection, for example by obscuring malicious behavior. An EDR killer aims to actively neutralize the EDR itself, often through privileged actions like BYOVD to blind or suppress defenses rather than sneak past them.







