Sensitive information is gold. Its value can be counted in the millions, considering how costly cyberattacks can turn out to be. First, though, bad actors need to position themselves to procure said data.
Thus, social engineering attacks are poised to exploit human error, with spearphishing representing one of their craftier variants, catching victims with bespoke scams designed to reel in specific people. How specific? Read on...
Key points of this article:
- Spearphishing is a tactic used to gain initial access in attacks against business systems.
- ESET Research has observed spearphishing numerous times, as it’s commonly used by advanced persistent threat (APT) groups in their operations.
- The end results of spearphishing can be anything from credential theft through data exfiltration to extortion and ransomware.
- Protection is a question of awareness, attack surface minimization, and extended prevention.
The anatomy of spearphishing
Spearphishing is an attack tactic deployed by malicious actors as an entry point into organizational networks. These attacks are designed to be deeply targeted, so they’re often used against high-value targets, such as governmental or financial entities, where a later breach could net a hefty return.
Specifically, spearphishing targets individuals or small groups of people with messages that appear to come from a trusted source or be on a subject of interest to the intended victim. In fact, this is where spearphishing differs from regular phishing the most. The authors of the attack collect data on their target by various social engineering methods, as well as scraping of public data sources like social media and press releases, to craft believable messages.
Message in a bottle
A form of spearphishing is business email compromise (BEC), a costly scam with the goal of procuring money or confidential data from a business by way of pretense. For example, a company’s financial department could be targeted by someone pretending to be the CEO or CFO requiring a prompt monetary transfer to make a business deal. This is how, in one case, a manufacturing firm lost $60 million.
ESET Research on the money
ESET Research has detected and observed multiple spearphishing campaigns, which are a global phenomenon.
In May 2025, ESET Research reported on Operation RoundPress, for which the compromise vector was a spearphishing email leveraging an XSS vulnerability to inject malicious JavaScript code into a victim’s webmail page. Most victims were governmental entities and defense companies in Eastern Europe, though some targets were detected in other parts of Europe, Africa, and South America.
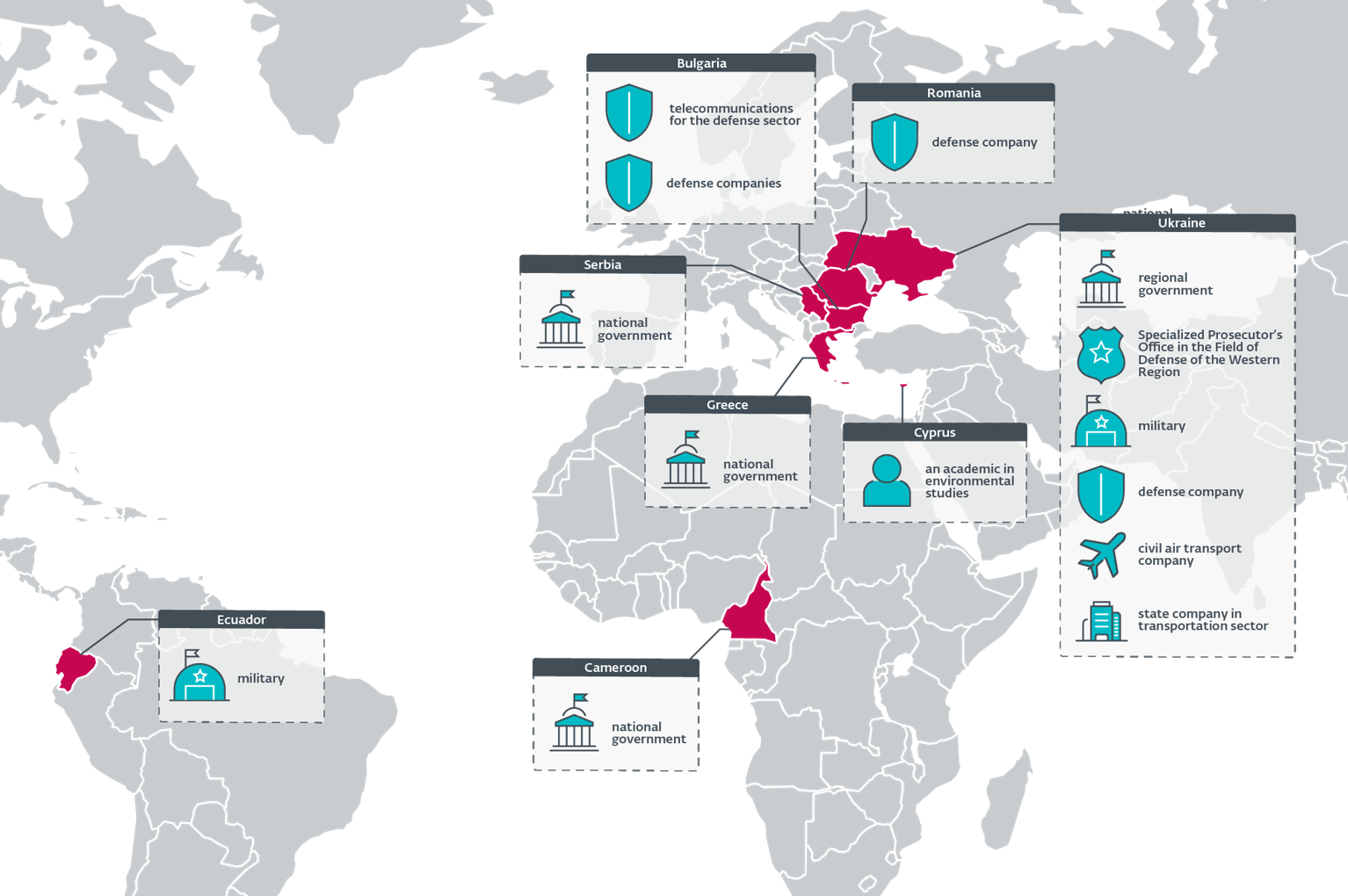
A map of Operation RoundPress victims as assessed by ESET. (Source: ESET Research)
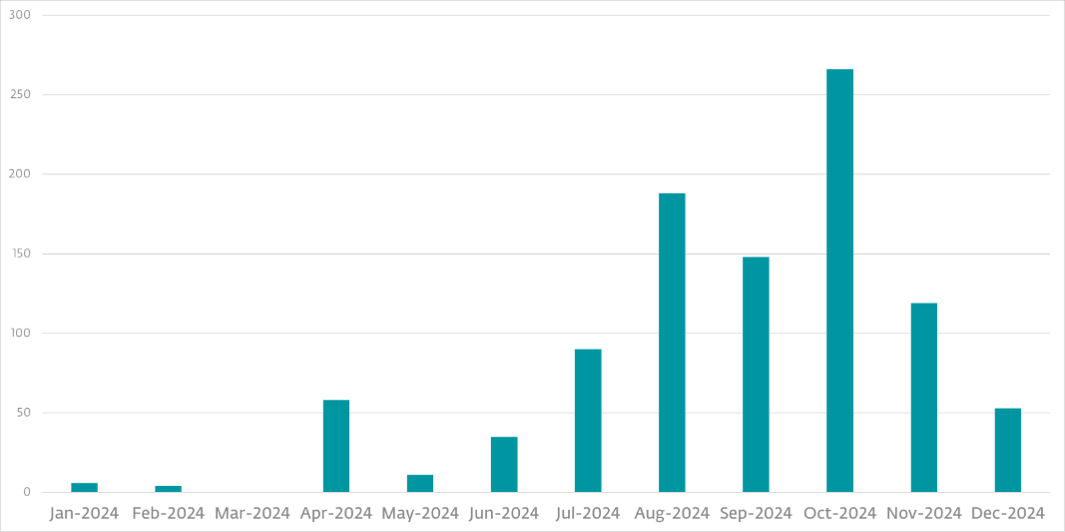
In truth, spearphishing is a major tool for nation-state attackers such as Gamaredon, a Russia-aligned APT group, which kept deploying large spearphishing campaigns against Ukrainian entities through 2022 and 2023, with major updates to their tools in 2024.
In Asia, MirrorFace, a China-aligned APT group that focuses on Japanese entities and their partners, has been targeting local companies and diplomatic organizations (such as one from the EU), with one particular spearphishing campaign (named Operation LiberalFace by ESET Research) that targeted Japanese political entities in 2022.
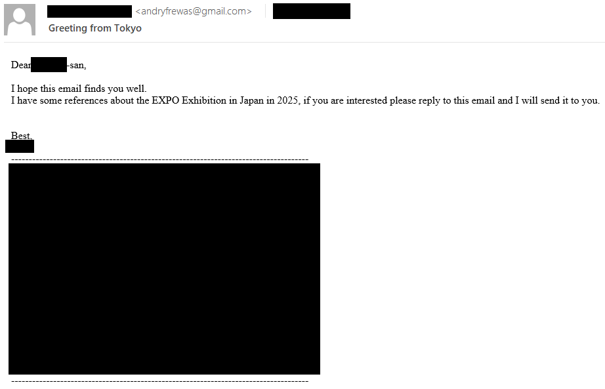
Examples of two spearphishing emails by MirrorFace. (Source: Dominik Breitenbacher/ESET Research)
Similarly, in late 2023, ESET Research revealed how enterprise-sized actors in particular, including those in governmental sectors in Latin America, were being targeted by spearphishing emails, with the attackers masquerading as recognized organizations from particular countries, such as government or tax entities. The precision of these attacks pointed to high-grade targeting, indicating that the threat actors had detailed knowledge about their intended victims.
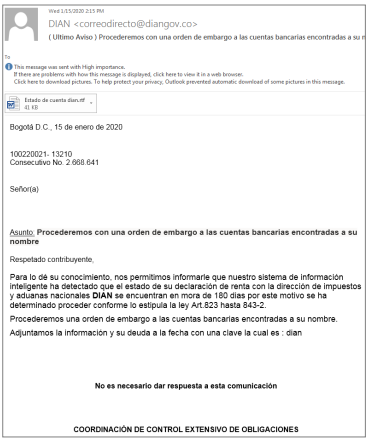
Example of a spearphishing email from LATAM. (Source: Camilo Gutiérrez Amaya and Fernando Tavella, Operation King Tut, ESET Research)
In many cases, spearphishing emails contain malicious content, such as malicious URLs, downloads, or attachments. In the case of a BEC, it could just be a phone number, email address, calendar, or meeting invite. Interacting with said malicious content could then trigger the next stage of the attack and/or compromise, even leading to malware installation. What can follow is even worse, though.
For more information about a slice of the latest global APT group activity and how spearphishing fits into the scheme of things, please read the ESET APT Activity Report Q4 2024-Q1 2025.
All are fish that come to the net
Spearphishing actors have many goals. Getting a business to fork over millions following a phony call is just as likely as the attackers having put their foot in a business network’s door following a single short email exchange.
Human error, which spearphishing exploits, is a leading cause of data breaches, with the 2025 Verizon Data Breach Investigations Report naming it as a major factor in 60% of all breaches.
For example, DeceptiveDevelopment, a North Korea-aligned group, focuses mostly on financial gain. It targets software developers on Windows, Linux, and macOS to steal cryptocurrency, sprinkled with a bit of potential cyberespionage. The group’s fake job listings appear to be advertised by legitimate companies and industry leaders based in the cryptocurrency or financial sector, such as investment firms. As part of one of its campaigns, DeceptiveDevelopment spread the WeaselStore infostealer, developed to exfiltrate data saved in Chrome, the MetaMask wallet extension, and the local keychain.
The outcome is obvious: monetary loss for individuals as well as a potential compromise of their online accounts. But what about a business example?
In 2014, a large US health insurance company suffered a large-scale data breach, potentially exposing the personal information of around 80 million people. Apparently, the hackers gained initial access by tricking an employee with a spearphishing email whose malicious content deployed malware, gained persistence, and then enabled the threat actor to move laterally through the organization’s network. Ultimately, the attackers gained access to the firm’s data storage system that held sensitive personal records.
The result? Multiple lawsuits at a cost of $115 million. Such attacks are just one of many critical issues the healthcare sector is facing.
How to protect against spearphishing
How can you prevent spearphishing from catching you off guard?
First off, focus on keeping your guard up. Human error is tough to account for, but it’s not impossible to lower the chances of it being an escalating factor for a cyberattack. For this purpose, cybersecurity awareness training is the gold standard, especially if addressed in a gamified, more interactive format followed by continuous simulations.
Second, establish a secure environment. Certain endpoint security solutions, or added cloud app and email server protection products, come with anti-phishing functionalities and advanced filters to block spearphishing messages before they end up in an employee’s hands (figuratively).
Third, advanced threat defense is also a very viable way to deal with malicious attachments that arrive in email. Behavioral detection has come a long way thanks to machine learning, and when coupled with endpoint security that is capable of stripping malware code down to its DNA, the multiple layers of preventive protection greatly lower the chance of anything slipping through.
It’s a good idea to establish essential but also extended prevention capabilities like vulnerability management and secure authentication, since the less room there is for a malicious actor to potentially abuse, the stronger a business’s digital fortress.
Spare me the details
The factors that contribute to the success of a spearphishing attack are many. Should that make one nervous? Undoubtedly. However, for every attack and vector, there’s a defensive strategy that works to mitigate it.
So, rather than falling for obvious bait, address your weaknesses and focus on a prevention-first mindset to face tomorrow’s threats in the present.
For more thorough insights into the latest ESET telemetry and threat landscape, make sure to follow ESET Research on Twitter (today known as X), BlueSky, and Mastodon.











