This blog documents 18 Android malware campaigns discovered by ESET researchers between 2023 and 2026. The threats range from trojanized messaging apps and banking phishing tools to near-field communication (NFC) payment fraud and, most recently, the first Android malware known to abuse generative AI. Each entry is based on original ESET research, with several campaigns having no prior public documentation at the time of discovery.
The landscape has changed dramatically: According to ESET telemetry, NFC-based threats grew 87% in the second half (H2) of 2025, and AI is now being used by both attackers (deepfakes, adaptive malware) and defenders. Use this list to understand what current Android threats look like in practice.
If you want to protect your mobile device against such attacks, try ESET Mobile Security.

StrongPity espionage campaign
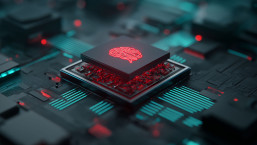
In early 2023, ESET researchers published a blog about the StrongPity a malware campaign, which spread a trojanized version of the hugely popular Android Telegram app. It was repackaged and presented as “the” app for the video-chat service Shagle, despite the fact that Shagle doesn’t have an official app. The fake app was then distributed from a copycat Shagle website.
image 1. Comparison of the legitimate website on the left and the copycat on the right
Ultimately, criminals used Shagle’s popularity — the app has 2.5 million active users — to spread this malware and its diverse spyware features, including 11 functions that are responsible for recording phone calls and collecting SMS messages, call logs, contact lists, and much more. If a victim grants the malicious StrongPity app access to their phone’s accessibility services, it will also be able to monitor incoming notifications and steal communications from 17 apps, including Viber, Skype, Gmail, Messenger, and Tinder.
Transparent Tribe Campaign
In March 2023, ESET researchers published a blog about a cyberespionage campaign that distributed CapraRAT backdoors through trojanized and supposedly secure Android messaging apps. The apps also accessed and removed sensitive information. Victims were likely targeted through a honey-trap romance scam in which they were initially contacted on one platform and then convinced to use supposedly more secure apps, which they were then lured into installing.
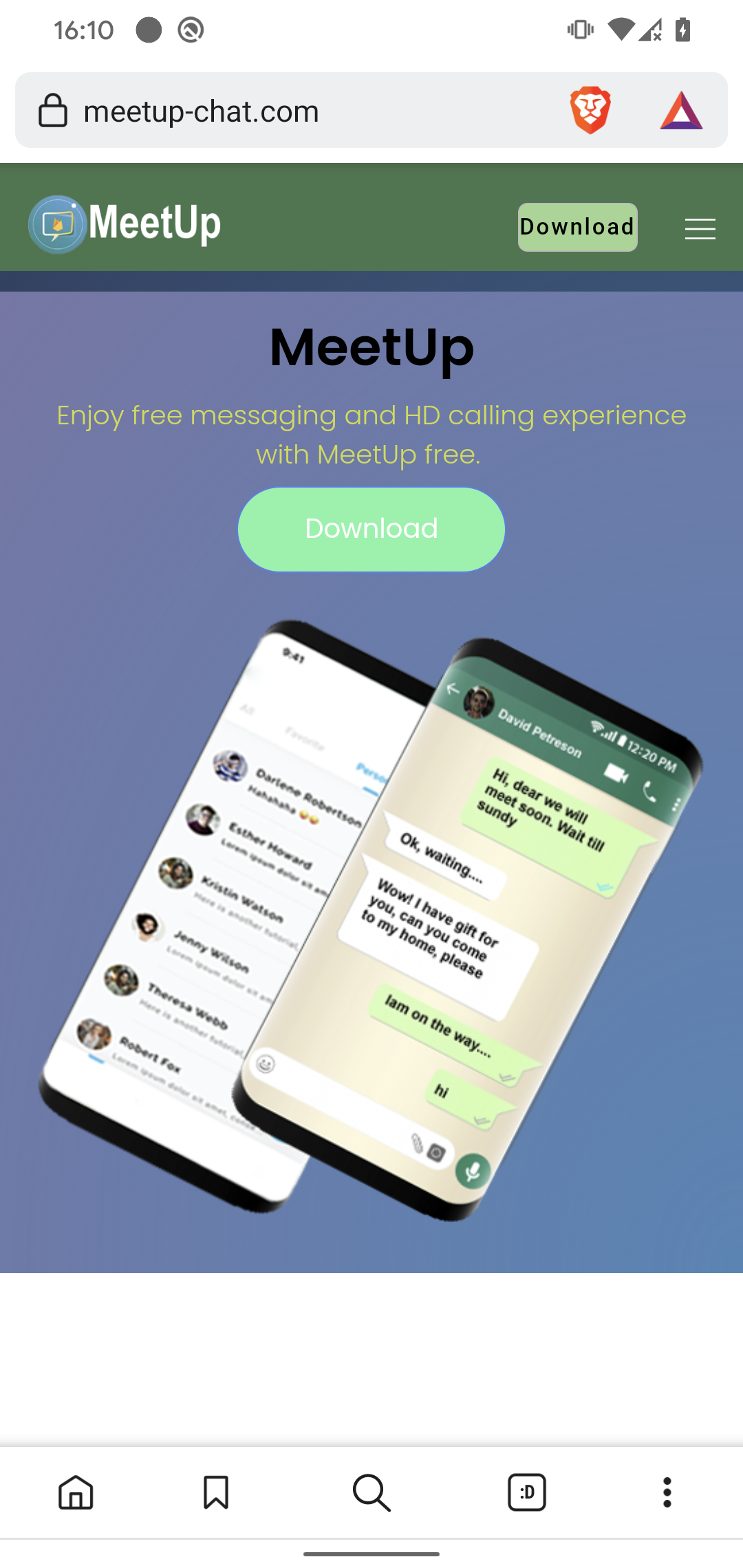
image 2. Distribution website of CapraRAT posing as MeetUp
After the victim signs into the app, CapraRAT then starts to interact with the server operated by the cybercriminal by sending basic device info while it waits to receive commands to execute. Based on these commands, CapraRAT is capable of stealing call logs, contact lists, SMS messages, recorded phone calls, recorded surrounding audio, CapraRAT-taken screenshots, CapraRAT-taken photos, and much more.
It can also receive commands to download files, launch any installed app, kill any running app, make calls, send SMS messages, intercept received SMS messages, and download updates and ask the victim to install them.
Trojanized WhatsApp and Telegram apps: Clipboard hijackers stealing cryptocurrency
At the beginning of 2023, ESET researchers discovered dozens of copycat Telegram and WhatsApp websites mainly targeting Android and Windows users with trojanized versions of these instant messaging apps.
image 3. Distribution diagram of trojanized messenger apps
Most of the malicious apps identified by ESET researchers are clippers, a type of malware that steals or modifies the contents of a user’s clipboard (short-term storage). Some of these apps use optical character recognition (OCR) to recognize text from screenshots stored on the compromised devices. All of them were chasing after victims’ cryptocurrency funds, with several targeting cryptocurrency wallets.
Android Gravity RAT
In June 2023, ESET researchers published research on Android GravityRAT spyware. This malware was distributed within the malicious but functional messaging apps BingeChat and Chatico, both based on the OMEMO Instant Messenger app.
image 4. Distribution website of the malicious BingeChat messaging app
This spyware can steal call logs, contacts, SMS messages, device location, basic device information, and files with specific extensions, such as jpg, png, txt, pdf, etc. GravityRAT can also access and steal WhatsApp backups and receive commands to delete files.
SpinOk
In the second half of 2023, ESET telemetry detected an 89% increase in Android malware, primarily due to a mobile marketing software development kit (SDK), a digital toolbox that ESET identified as SpinOk Spyware. This toolbox was offered as a gaming platform and was incorporated into numerous legitimate Android apps, including many available on official app marketplaces.
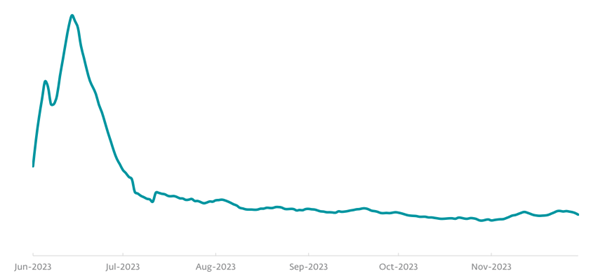
image 5. Android/SpinOK detection trend in H2 2023, seven-day moving average
Once an app with the aforementioned SpinOk toolkit is installed, it operates like spyware, connecting to the criminal’s command-and-control server and stealing a range of data from the device, including potentially sensitive clipboard contents.
Telekopye
In 2023, ESET researchers found the source code of a toolkit toolkit that helps well-organized groups of scammers to conduct online-shopping scams without being particularly well versed in IT. The toolkit, which ESET researchers have named Telekopye, creates phishing web pages from predefined templates, generates phishing emails and SMS messages, and sends them to targeted users.
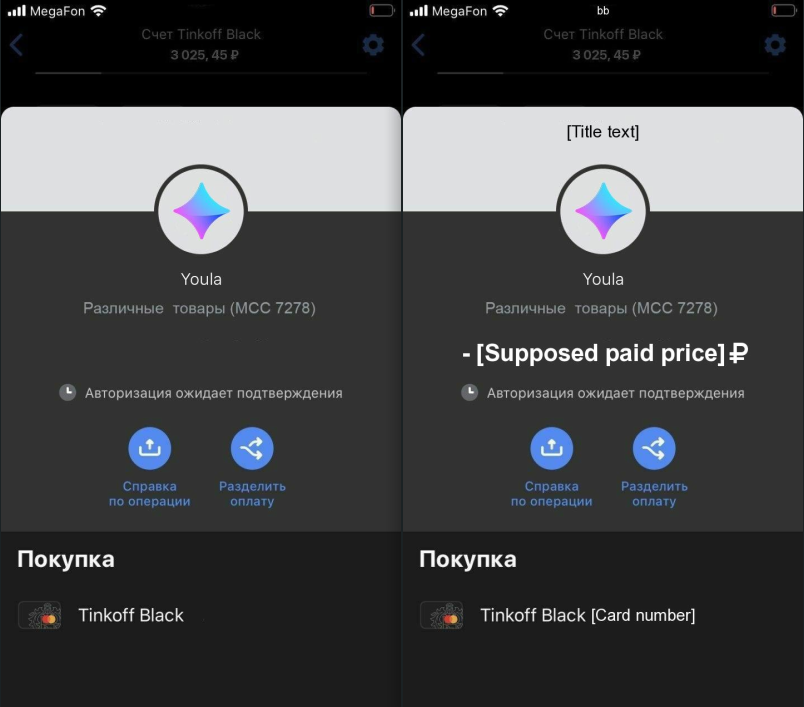
image 6. Generated fake screenshot (template on the left, template filled with sample text on the right)
First, attackers find their victims, then they try to earn their trust so they fall for either a buyer scam, a seller scam, or a refund scam. When attackers think that a victim sufficiently trusts them, they use Telekopye to create a phishing web page from a premade template and then send the URL to the victim. For example, attackers trick a victim into buying a nonexistent item and then send them a link to a phishing web page resembling the payment page of the legitimate online marketplace listing the reputed item.
After the victim submits card details via this page, the attackers use these card details to steal the victim’s money.
Kamran
In late 2023, ESET researchers identified a possible watering-hole attack on on a regional news website that delivers news about Gilgit-Baltistan, a disputed region administered by Pakistan. When opened on a mobile device, the Urdu version of the Hunza News website offered readers the option to download the Hunza News Android app directly from the website; however, the app had malicious capabilities, specifically espionage.
The Kamran spyware in question displayed the content of the Hunza News website and contains custom malicious code. Upon launching, Kamran prompts the user to grant permissions to access various data stored on the victim’s device. If permissions are granted, Kamran spyware automatically gathers sensitive user data, including SMS messages, contacts list, call logs, calendar events, device location, list of installed apps, received SMS messages, device info, and images.
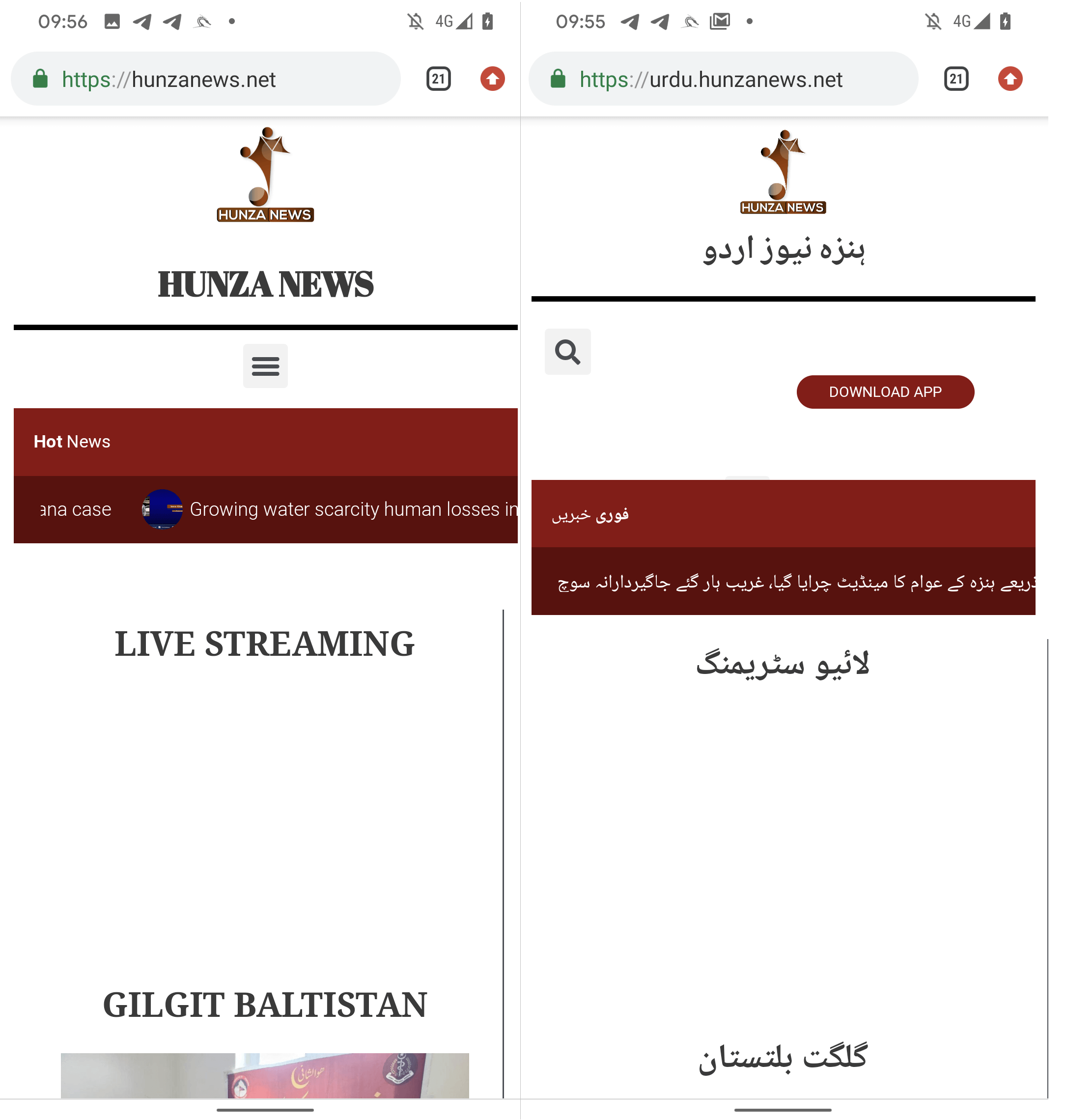 image 7. English (left) and Urdu (right) versions of Hunza News shown on a mobile device
image 7. English (left) and Urdu (right) versions of Hunza News shown on a mobile device
2024: Zero-day exploits, NFC payment fraud, and banking phishing
EvilVideo
ESET researchers discovered a zero-day exploit that targets Telegram for Android, and appeared for sale for an unspecified price in an underground forum post on June 6, 2024. Using the exploit to abuse a software vulnerability that researchers named EvilVideo, attackers could share malicious Android content via Telegram channels, groups, and chat, and make them appear as multimedia files. The exploit works only on Android Telegram versions 10.14.4 and older. After ESET researchers approached Telegram, they fixed the issue.
The exploit seems to rely on the threat actor being able to create a malicious payload (content) that displays an Android app as a multimedia preview. Once shared in a chat, the payload appears as a 30-second video. Since media files received via Telegram are set to download automatically by default, it means that users with the option enabled will automatically download the malicious payload once they open the conversation in which it was shared. The option can be disabled manually; in that case, the payload can still be downloaded by tapping the download button in the top left corner of the shared apparent video.
Hamster Kombat malware: Ratel spyware and fake app stores targeting players
In mid-2024, ESET researchers discovered and analyzed two threats abusing the success of Hamster Kombat, an in-app Telegram clicker game where players earn fictional currency by completing simple tasks and incentives to log into the game daily.
The first threat is a fake, non-functional, malicious app resembling the Hamster Kombat app that contains Ratel Android spyware capable of stealing notifications and sending SMS messages. The malware operators use this functionality to pay for subscriptions and services with the victim’s funds without the victim noticing.
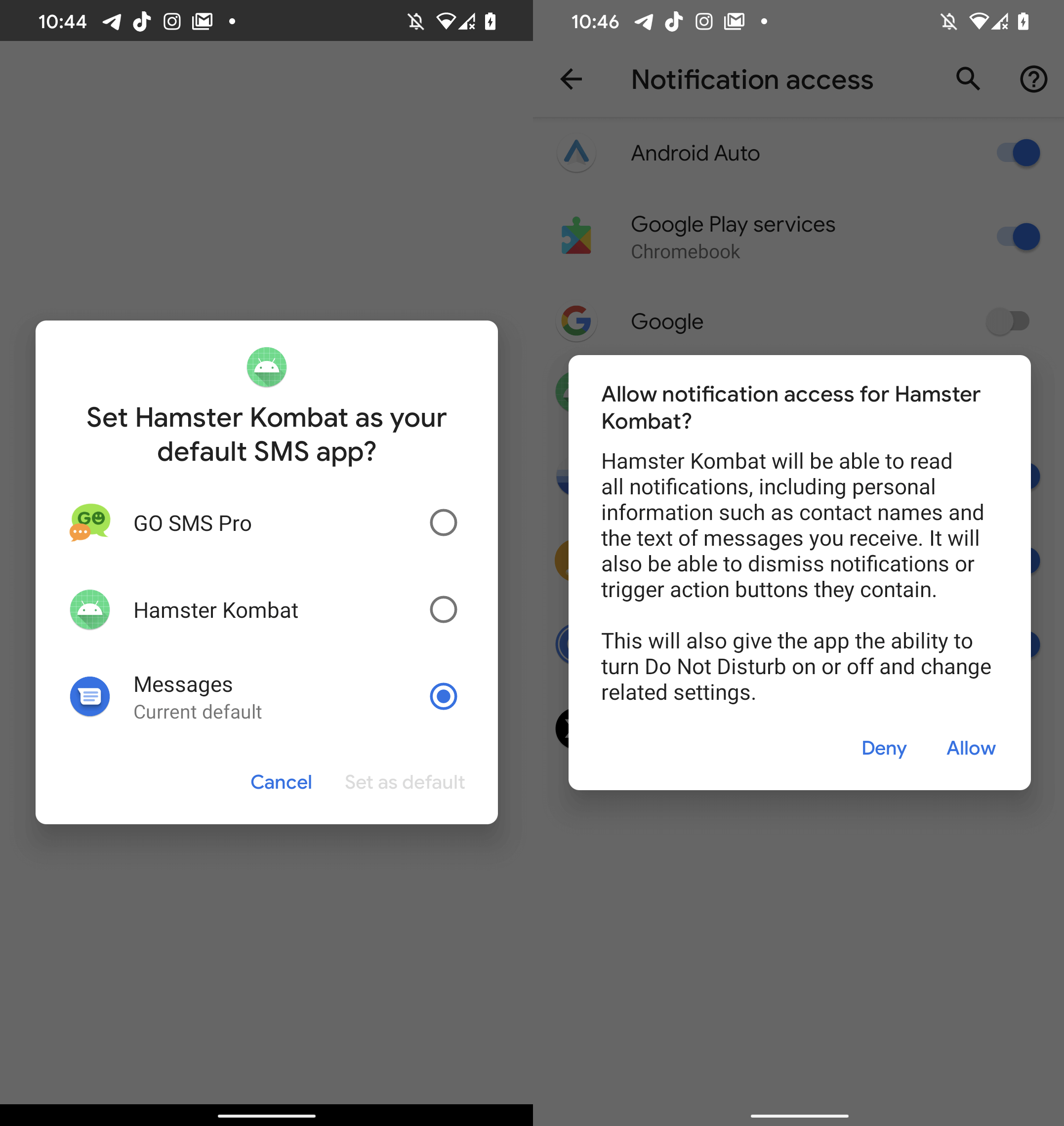
image 8. Malicious Hamster Kombat access requests
The second threat is a collection of fake websites that mimic app stores claiming to have Hamster Kombat available for download. However, tapping the “Install” or “Open” buttons only leads the user to unwanted advertisements.
PWA banking phishing: How attackers install fake banking apps without Google Play
In mid-2024, ESET Research published a blog about an uncommon type of phishing campaign targeting mobile users who are clients of a prominent Czech bank. This technique is noteworthy because it abuses a progressive web application (PWA), allowing the installation of a phishing app from a third-party website without the user having to allow third-party app installation.
The initial sources of this campaign included automated voice calls, SMS messages, and social media malvertising that ultimately encouraged victims to open a phishing URL redirecting them to a fake Google Play Store page for the targeted banking application or a copycat website for the application.
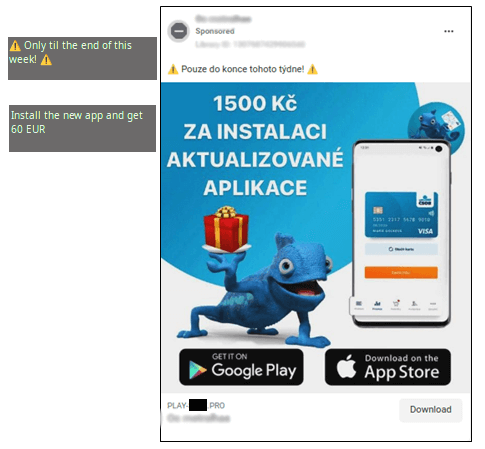
image 9. Example of a malicious advertisement used in these campaigns
After visiting these fake websites, Android users saw a pop-up ad enticing them to install the malicious application resembling the legitimate banking application. The application was, in fact, created with WebAPK technology that enables the creation of web applications that can be installed on Android devices as if they were native, or legitimate. This allows users to install PWAs to their home screen on Android devices without having to use the Google Play Store.
NFCGate
While monitoring a malicious campaign that abuses PWA to steal banking credentials from targets in the Czech Republic, ESET researchers uncovered a truly novel attack related to the previous campaign. In August 2024, ESET published a blog about the same criminal group improving their techniques to enable unauthorized ATM withdrawals from the bank accounts of clients at three Czech banks.
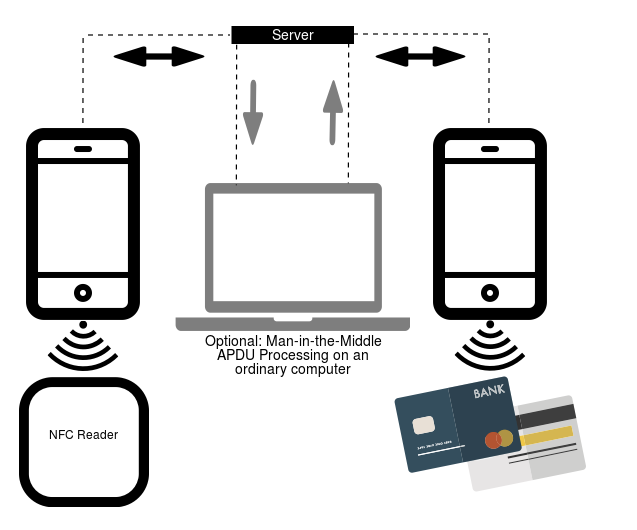
image 10. NFCGate architecture (source: https://github.com/nfcgate/nfcgate/wiki)
First, cyber criminals deceived victims into believing that they were communicating with their bank, and then they tricked them into downloading and installing a fake banking app with a unique malware that ESET has named NGate. The malware clones near-field communication data (NFC) from victims’ payment cards using NFCGate and sends this data to an attacker’s device. That device is then able to imitate the original card and withdraw money from an ATM.
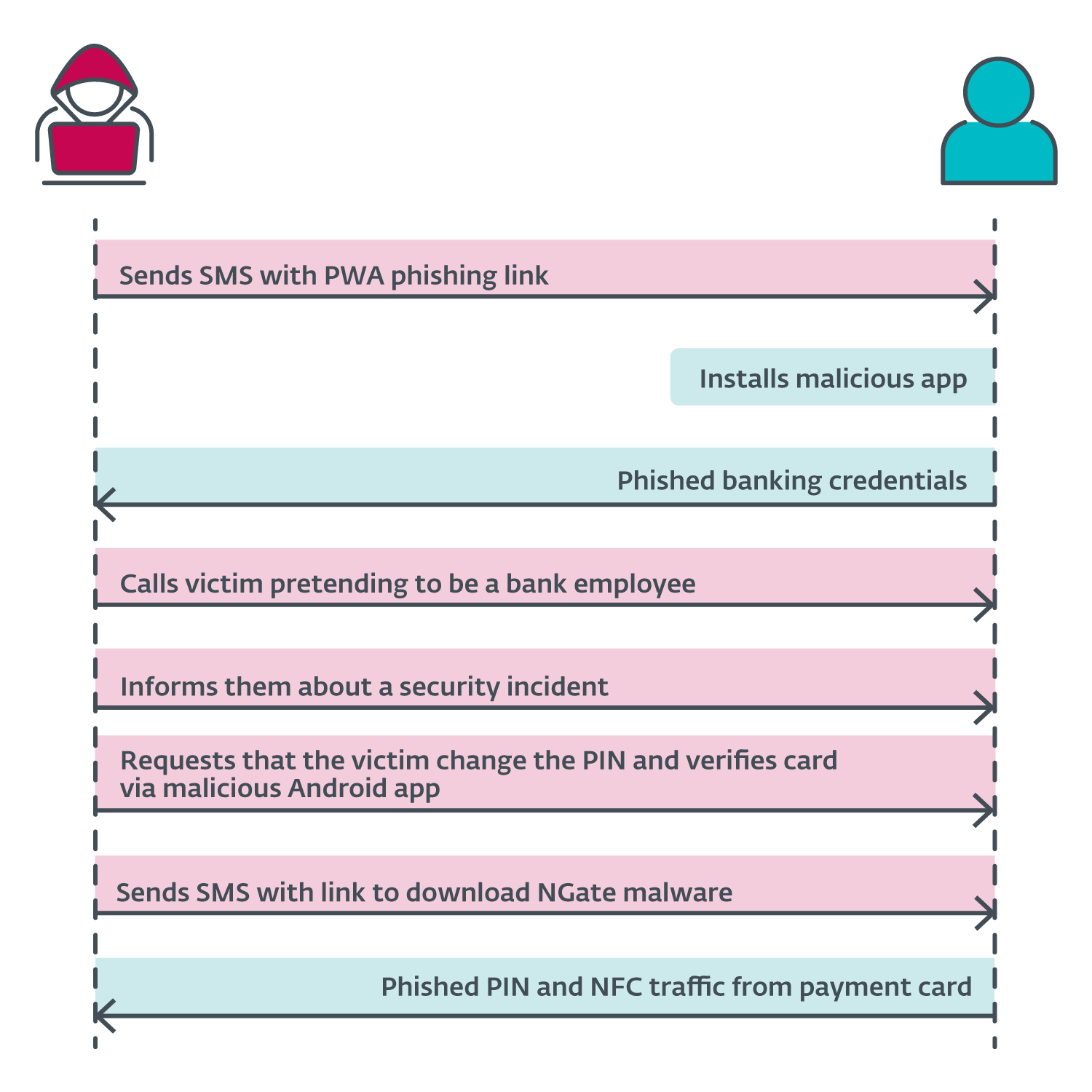
image 11. The specific attack scenario for the 2024 NFCGate malicious campaign
Since then, cybercriminals have been constantly improving both scam tactics and malware. ESET telemetry recorded an 87% increase in NFC-related threats in H2 2025. For example, in an improved attack scenario, attackers now take a further step, persuading victims to reveal a one-time passcode to confirm their card details for a digital wallet so that they can in fact register the stolen card to the criminal’s own digital wallet.
In late 2025, ESET researchers discovered a new version of NFCGate malware capable of harvesting saved contacts, likely to increase the success rate of the fake support calls. Other variants of this malware include remote control, accessibility service abuse, and automated transfer system capabilities.
Nomani
In 2024, social media saw a flood of new scam ads propagating “secret” investment opportunities, miraculous dietary supplements, and legal or law enforcement assistance.
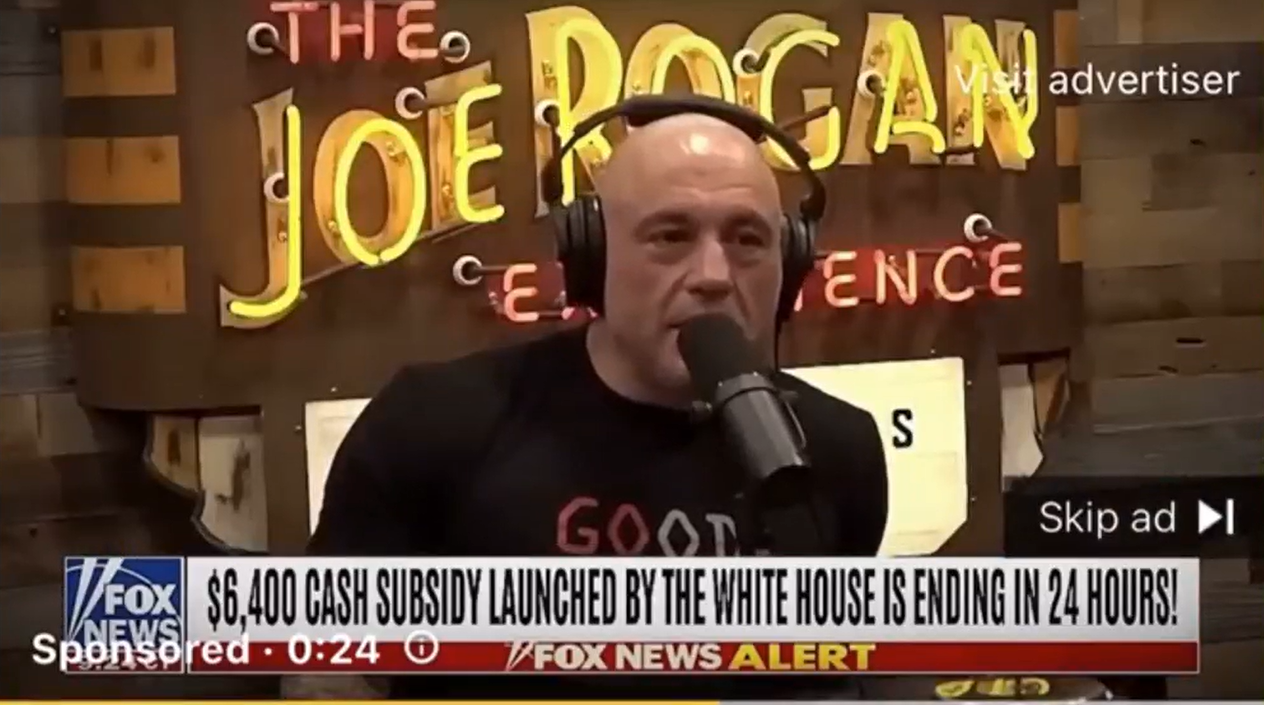
image 12. AI-generated deepfake video featuring Joe Rogan
To make these offers appear credible, criminals misuse the brands of local and global businesses or use AI-generated deepfake videos featuring famous personalities apparently guaranteeing the legitimacy of the advertised products. The main goal of the fraudsters is to lead victims to phishing websites and forms that harvest their personal information.
In 2025, Nomani scams saw several notable upgrades, including higher-quality news-related deepfakes, improved phishing websites showing signs of AI-generated elements, and shorter fake ad campaigns that can evade automated protection on social media more efficiently.
2025–2026: PromptSpy, GhostChat, ClickFix, and GhostPairing
Spyware campaigns target privacy-conscious Android users
In mid-2025, ESET researchers discovered two spyware campaigns targeting, paradoxically, privacy-conscious Android users. Both campaigns were distributed through deceptive websites designed to impersonate communication platforms Signal and ToTok. These sites offer malicious applications posing as improvements that are disguised as a “Signal Encryption Plugin” and “ToTok Pro.” Neither app containing the spyware was available in official app stores. Once installed, both spyware families exfiltrate sensitive data and files from compromised Android devices.
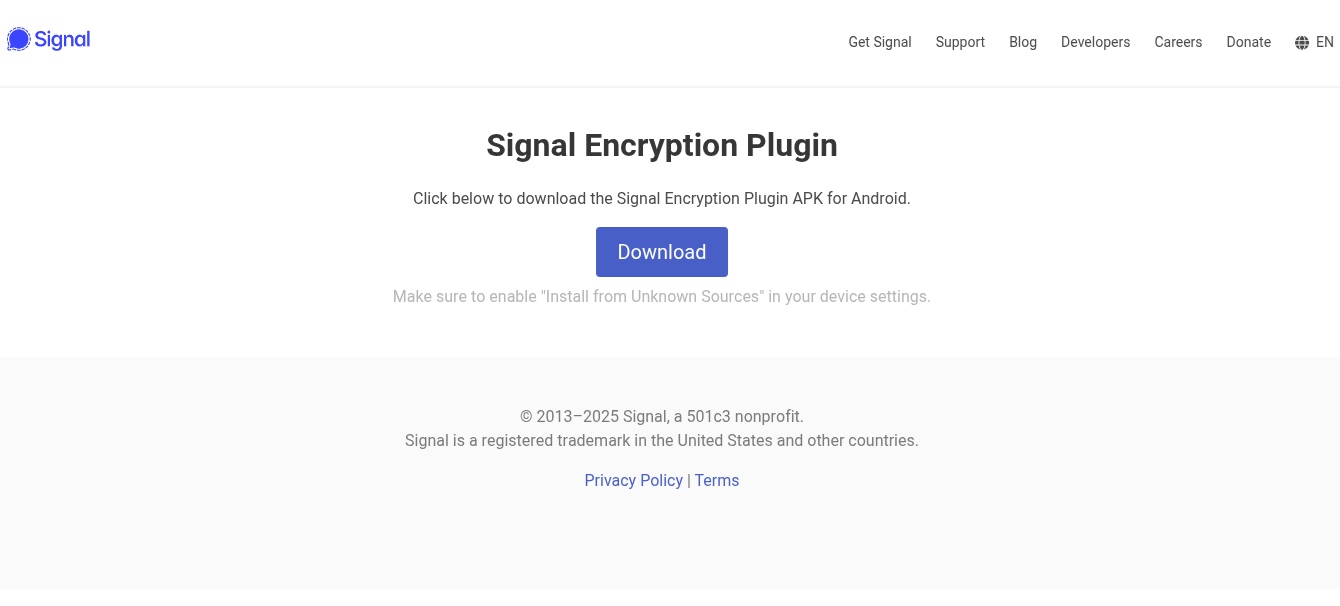
image 13. Website distributing fake Signal Encryption Plugin app
GhostChat
In H2 2025, ESET researchers uncovered an Android spyware campaign that uses romance scam tactics and a malicious app disguised as a legitimate chat platform. The malicious app, which the researchers named GhostChat, has never been available on Google Play, and users have to enable permissions for installing apps from unknown sources to get it.
Presumably, attackers offered victims a link for the malicious app together with a passcode to unlock profiles of women available in the app. However, once the app is installed, its operators can immediately monitor and exfiltrate sensitive data from the victim’s device. The passcode requirement is there only to create a sense of security and exclusivity.
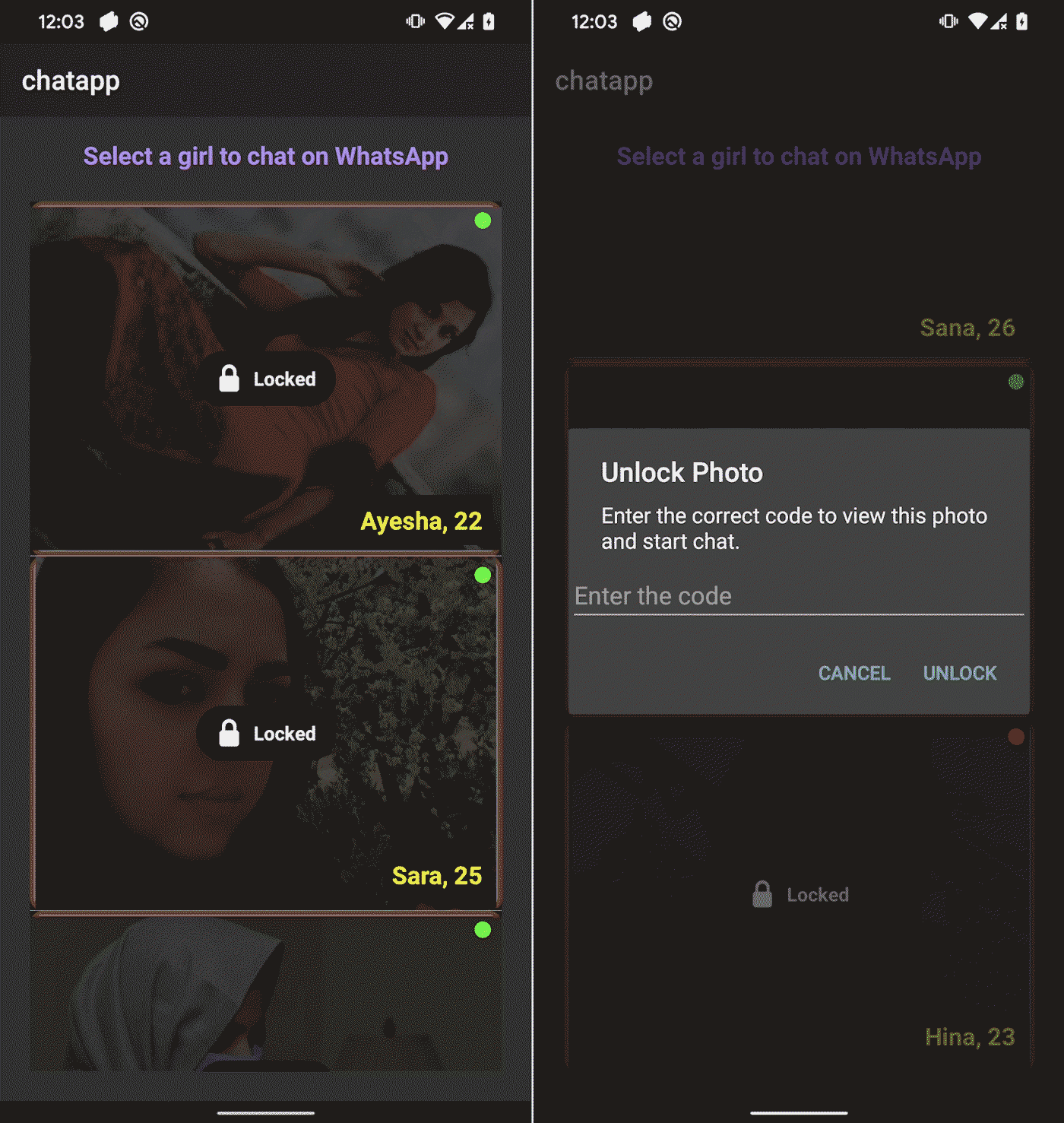
image 14. GhostChat deceptively hides user profiles behind a code
GhostChat and ClickFix
The group operating GhostChat malware also worked with a malicious payload in a separate ClickFix-based attack. ClickFix is a social engineering technique that tricks users into manually executing malicious code on their devices by following seemingly legitimate instructions, like fake “Verify you are human” CAPTCHA.
This attack used a fake website impersonating Pakistan’s Computer Emergency Response Team (PKCERT) displaying a fabricated security warning allegedly affecting national infrastructure and government networks, and urging users to click an Update button. This action triggered ClickFix instructions, which led to the download and execution of the malicious dynamic-link library (DLL).
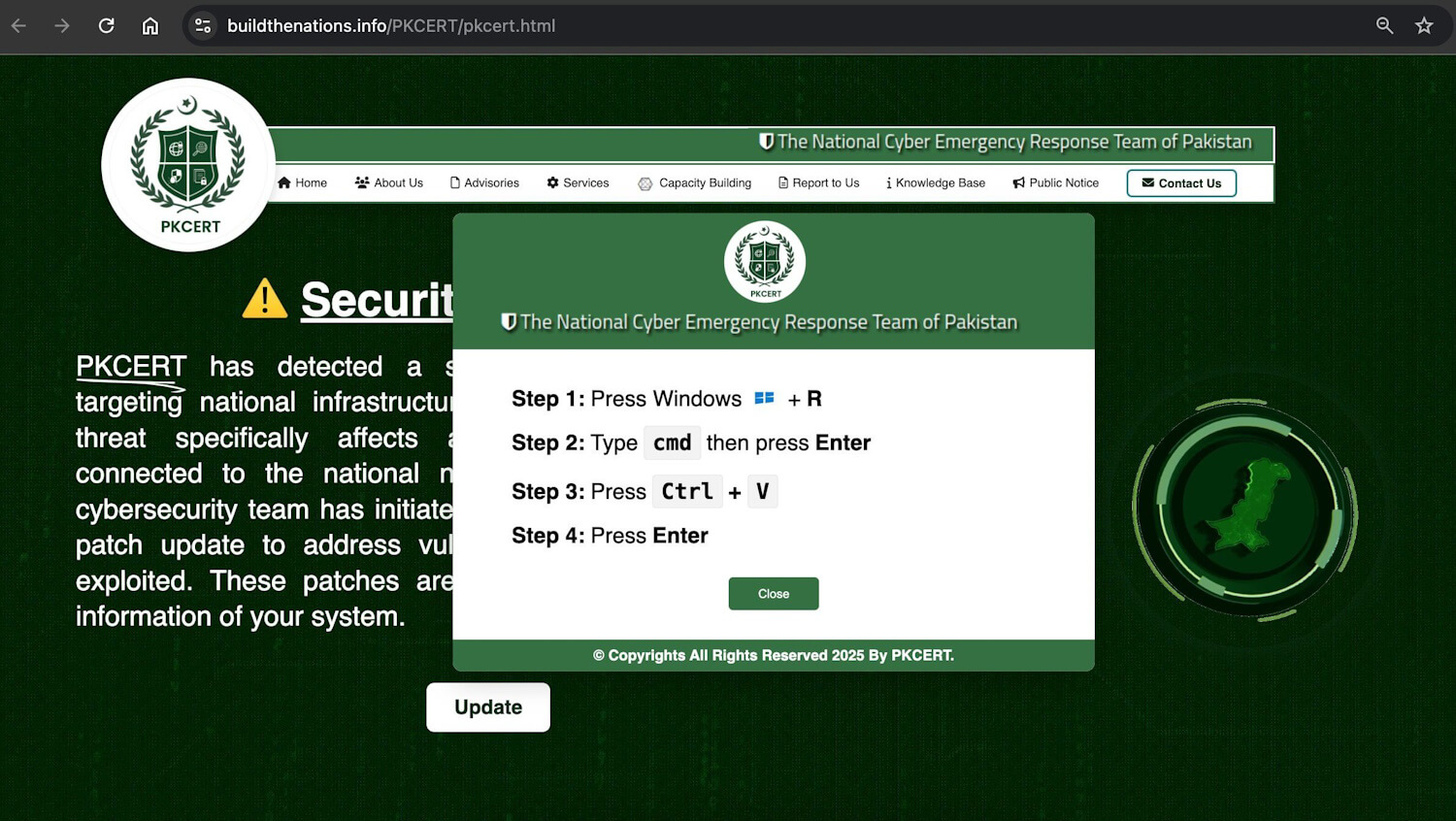
image 15. ClickFix instructions used in the attack
GhostPairing
The same GhostChat cybercriminal group also operated a mobile-focused campaign aimed at WhatsApp users. Using a technique known as GhostPairing, attackers lured victims into joining a fake online community by scanning a QR code to link their Android or iPhone device to WhatsApp Web or Desktop. This way, victims were tricked into pairing their WhatsApp account with the attackers’ device, allowing them to take control over the compromised account. In fact, users received a notification about a new device that had been linked to their account.
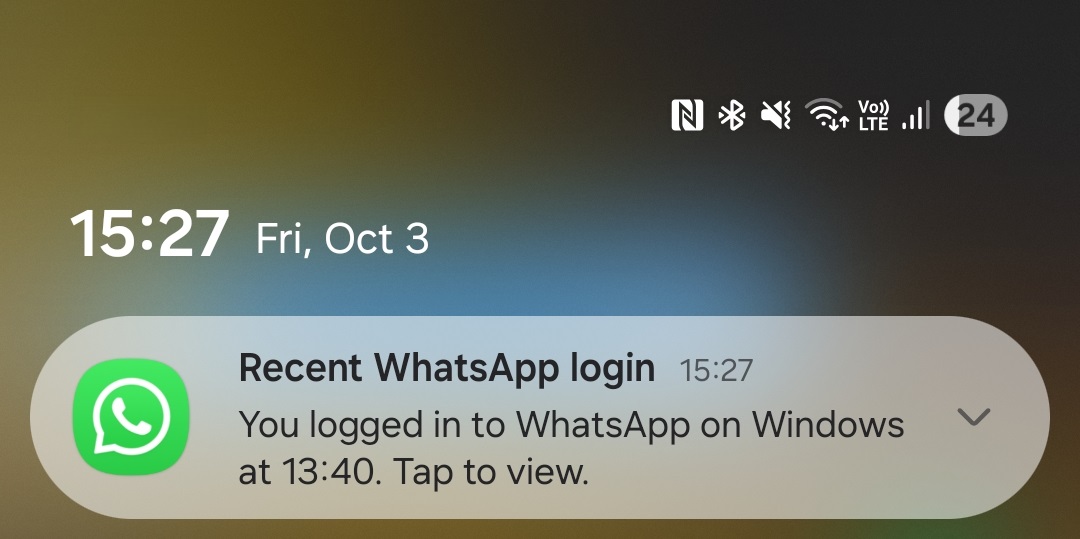
image 16. WhatsApp’s notification informing the user that their account had been linked to another device
PromptSpy
In mid-February 2026, ESET researchers published a blog about the first known case of Android malware that abuses generative AI to analyze the screen activity of a compromised smartphone, likely distributed as a fake banking app. Dubbed PromptSpy, this malware spies on the device by capturing lock‑screen data, gathering device information, taking screenshots, recording the screen as video, and more. It also includes a virtual network computing (VNC) module that lets attackers view the victim’s screen in real time and remotely perform taps, swipes, and text input as if they were physically holding the phone.
Description: ESET senior malware researcher Lukáš Štefanko summarizes this newly discovered threat
The AI‑powered component helps the malicious app remain active by preventing it from being closed. To do this, the malware keeps itself pinned in the recent apps list by executing the “lock app in recent apps” gesture. Because this gesture varies across devices and manufacturers, writing one piece of code to handle all variations is difficult. PromptSpy gets around this by sending Google Gemini a prompt that includes the device’s current screen setup, allowing the AI to analyze interface elements such as text, type, and position. Gemini then returns precise, step‑by‑step instructions showing exactly where the malware needs to tap to stay pinned in the recent apps list.
Stay protected with ESET Mobile Security
ESET Mobile Security can defend users against a wide spectrum of mobile threats, including malicious apps (from both third-party side-loading and official app stores), other malware, hidden threats in files, phishing links, and physical theft.
ESET Mobile Security can block:
Trojans disguising themselves as harmless apps
Spyware secretly monitoring your activity or location
Ransomware locking your files and demanding payment
Adware bombarding you with intrusive pop-ups
Phishing, smishing, and scam links received from notifications and social apps trying to steal your sensitive data
Potentially unwanted applications (PUAs) that may compromise privacy or performance And more.
ESET Mobile Security also offers Payment Protection feature which adds an extra layer of security to apps like Google Pay or your mobile banking app. When active, Payment Protection prevents malicious apps from reading, modifying, or overlaying content on your protected apps—helping to stop phishing attempts and data leaks. .
How to stay safe from Android malware: Key takeaways
There are two main takeaways from these cases:
First, as you can see, some of these cyberattacks and scams can be spotted right away if users pay attention and have some level of security awareness. Research blogs, such as those previously mentioned, may serve as valuable sources. Android users who stay informed about newly discovered malware and emerging scams can enhance their risk awareness, enabling them to better safeguard against future online threats.
Second, certain malicious campaigns are more sophisticated and challenging to spot. Furthermore, cybercriminals often target vulnerable groups, including children and the elderly, who may be less prepared to confront such dangers. In any case, it is always good to have a reliable cybersecurity solution such as ESET Mobile Security that can detect and neutralize these threats, ideally before any damage occurs to your device or data.
Frequently asked questions (FAQs)
What are the most common cyberthreats targeting Android users?
Android users commonly encounter scams such as fake investment schemes, fraudulent tech‑support offers, and Android‑specific malware hidden inside apps that appear legitimate. Many attacks begin with phishing messages sent through SMS, social networks, or various chat applications.
What are the newest Android threats emerging in the AI era?
ESET researchers have identified a new AI‑powered Android malware named PromptSpy, enhanced scam techniques supported by AI‑generated deepfakes, and increasingly sophisticated social‑engineering attacks. These emerging threats are more difficult for both users and automated detection systems to identify.
What does a typical Android spyware campaign look like?
Usually it begins with social engineering luring users into installing a legitimate-looking but malicious app. Attackers commonly distribute such malware through messaging apps, SMS smishing, or deceptive websites that mimic official app stores. These malicious apps frequently come with instructions that encourage victims to bypass Android’s built‑in security warnings and enable installation from unknown sources.
Once installed, the spyware requests extensive permissions, such as access to messages, call logs, camera, and storage. Then, it begins harvesting sensitive data, including chat messages, photos, credentials, and even takes snapshots with a phone’s front camera.
What is the fastest-growing Android threat?
In recent years, cybercriminals have started to exploit near-field communication (NFC) technology, which enables contactless transactions. NFC threats continued to grow in scale and sophistication, with an 87% increase in ESET telemetry and several notable upgrades and campaigns observed in H2 2025.