The attackers spread malicious apps through six Facebook profiles, which were taken down after ESET notified Facebook
BRATISLAVA, KOŠICE — ESET researchers have investigated a targeted mobile espionage campaign against the Kurdish ethnic group. This campaign has been active since at least March 2020, distributing (via dedicated Facebook profiles) two Android backdoors known as 888 RAT and SpyNote, disguised as legitimate apps. These profiles appeared to be providing Android news in Kurdish, and news for the Kurds’ supporters. ESET Research identified six Facebook profiles distributing Android spying apps as part of this campaign, conducted by the BladeHawk group. The profiles shared the espionage apps to Facebook public groups, most of which were supporters of Masoud Barzani, former President of the Kurdistan Region, an autonomous region in northern Iraq. Altogether, the targeted Facebook groups have over 11,000 followers.
“We reported these profiles to Facebook and they have all been taken down. Two of the profiles were aimed at tech users while the other four posed as Kurd supporters,” says ESET researcher Lukáš Štefanko, who investigated this BladeHawk campaign.
ESET Research identified 28 unique Facebook posts as part of this BladeHawk campaign. Each of these posts contained fake app descriptions and links from which ESET researchers were able to download 17 unique APKs. Some of the APK web links pointed directly to the malicious app, whereas others pointed to the third-party upload service top4top.io, which tracks the number of file downloads. The spying apps were downloaded 1,418 times.
Most of the malicious Facebook posts led to downloads of the commercial, multiplatform 888 RAT, which has been available on the black market since 2018. Android 888 RAT is capable of executing 42 commands received from its command and control (C&C) server. It can steal and delete files from a device, take screenshots, get device location, phish Facebook credentials, get a list of installed apps, steal user photos, take photos, record surrounding audio and phone calls, make calls, steal SMS messages, steal the device’s contact list, and send text messages.
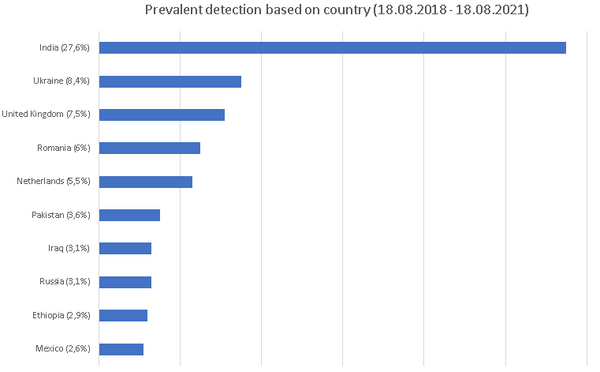
This espionage activity discovered by ESET Research is directly connected to two cases publicly disclosed in 2020. In one case, the QiAnXin Threat Intelligence Center named the group behind the attacks BladeHawk, which ESET has adopted. Both campaigns were distributed via Facebook, using malware that was built with commercial, automated tools (888 RAT and SpyNote), with all samples of the malware using the same C&C servers. Since 2018, ESET products have identified hundreds of instances of Android devices where the 888 RAT was deployed.
For more technical details on the latest BladeHawk campaign, read the blog post “BladeHawk group: Android espionage against Kurdish ethnic group” on WeLiveSecurity. Make sure to follow ESET Research on Twitter for the latest news from ESET Research.
About ESET
For more than 30 years, ESET® has been developing industry-leading IT security software and services to protect businesses, critical infrastructure and consumers worldwide from increasingly sophisticated digital threats. From endpoint and mobile security to endpoint detection and response, as well as encryption and multifactor authentication, ESET’s high-performing, easy-to-use solutions unobtrusively protect and monitor 24/7, updating defenses in real time to keep users safe and businesses running without interruption. Evolving threats require an evolving IT security company that enables the safe use of technology. This is backed by ESET’s R&D centers worldwide, working in support of our shared future. For more information, visit www.eset.com or follow us on LinkedIn, Facebook, and Twitter.