Zakaj bi morala mala in srednja podjetja skrbeti za gesla?
Glede na Verizonovo poročilo o preiskavi kršitev podatkov za leto 2017 kar 81% kršitev podatkov povzročajo šibka ali ukradena gesla. Glede na to, da je v spletu pricurljalo več kot 5 milijard gesel, osnovna zaščita z geslom postane neučinkovita.
In če menite, da vaša organizacija nima ničesar, kar bi zanimalo kiber kriminalce, pomislite znova. Mala in srednje velika podjetja so najboljša točka za kiber kriminalce, saj imajo dragocenejše podatke in sredstva kot potrošniki, vendar so bolj ranljiva kot podjetja, ki imajo večje proračune za varnost.
Preberi več
To težavo povečuje vse večje število podjetij, ki v svojo informacijsko infrastrukturo vključujejo "pametne" naprave. Medtem ko jim internet stvari (IoT) pomaga pri hitrejšem in gladkem poslovanju, so te naprave pogosto ranljive in delujejo z javno dostopnimi privzetimi skrbniškimi uporabniškimi imeni in gesli, kar predstavlja tveganje, ki lahko povzroči škodljive posledice.
Poleg tega nova splošna uredba EU o varstvu podatkov (GDPR) določa, da morajo organizacije vseh velikosti zagotoviti varnost svojih podatkov z izvajanjem "ustreznih tehničnih in organizacijskih ukrepov". Če torej pride do kršitve in so na mestu le preprosta in statična gesla, lahko pričakujemo veliko globo.
Po vsem svetu se zakoni in predpisi o zasebnosti zaostrujejo. Nedavno sprejete zahteve glede poročanja o kršitvah podatkov (NDB) iz avstralskega zakona o zasebnosti in predpisi o zasebnosti različnih zveznih držav ZDA s strogimi zahtevami glede poročanja o kršitvah podatkov nadgrajujejo standarde za vse, ki imajo podatke o prebivalcih teh jurisdikcij.
How do attackers steal passwords?
1. Simple, real-world techniques include shoulder surfing with attackers observing potential victims when they type their passwords.
2. Attackers also manipulate the “human weakness” of their victims via social engineering. A professionally-crafted online form or an email (phishing attack) apparently from a trustworthy sender can persuade even well-trained users to divulge their passwords.
3. Cybercriminals with foothold in organization’s network can use malware to search fordocuments containing passwords or log password keystrokes and send this information to their C&C server. Black hats can also extract encrypted password files and crack them offline.
4. More demanding attack techniques include intercepting the network traffic of employee devices that are used remotely or in a public place.
5. One of the most popular ways to break password protection is to brute force them. Automated scripts try millions of password combinations over a short period of time until the correct one is found. This is why it has become necessary for passwords to become longer over the years. The more complex the password is, the more time cybercriminals need to guess it.

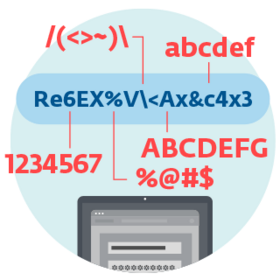
How to build a good password policy?
To ensure your organization has an effective password policy it’s advisable to follow specific procedures:
- Employees need to be trained on how to create a strong password. »
- IT departments should implement rules when setting and enforcing a company password policy. »
- All organizations are recommended to implement additional protective measures to increase password security throughout the entire organization.
What else can your organization do to protect its passwords?
To better protect the passwords of your organization's employees, use of two-factor authentication (2FA) is recommended. This verifies the account holder’s identity with a one-time passcode – something the user has – in addition to the username and password – something the user knows – thus protecting access to company systems even in cases where the credentials are leaked or stolen.
As SMS and mobile devices are frequently subject to malware attacks, modern 2FA solutions refrain from using SMS verification and instead opt for push notifications, as they are more secure as well as user-friendly. To further increase the security of the authentication process, organizations can add biometry – something the user is – by implementing multi-factor authentication (MFA).
ESET’s powerful 2FA protects passwords

Single-tap, mobile-based authentication provides help in securing your data in a hassle-free way in addition to meeting required compliances. It employs user-friendly push notifications for both Android and iOS, has an easy management, and fast roll-out within 10 minutes. Try now and see how it works.


