1bn+
users worldwide
500k+
business customers
ESET Mail Security za IBM Domino
Dodatna plast zaščite elektronske pošte v realnem času pred ciljnimi napadi , lažnim predstavljanjem in zlonamerno programsko opremo, ki popolnoma dopolnjujejo zaščite ESET z:

Protivirusna programska zaščita

Proti nezaželjeni pošti

Preprečevanje lažnega predstavljanja

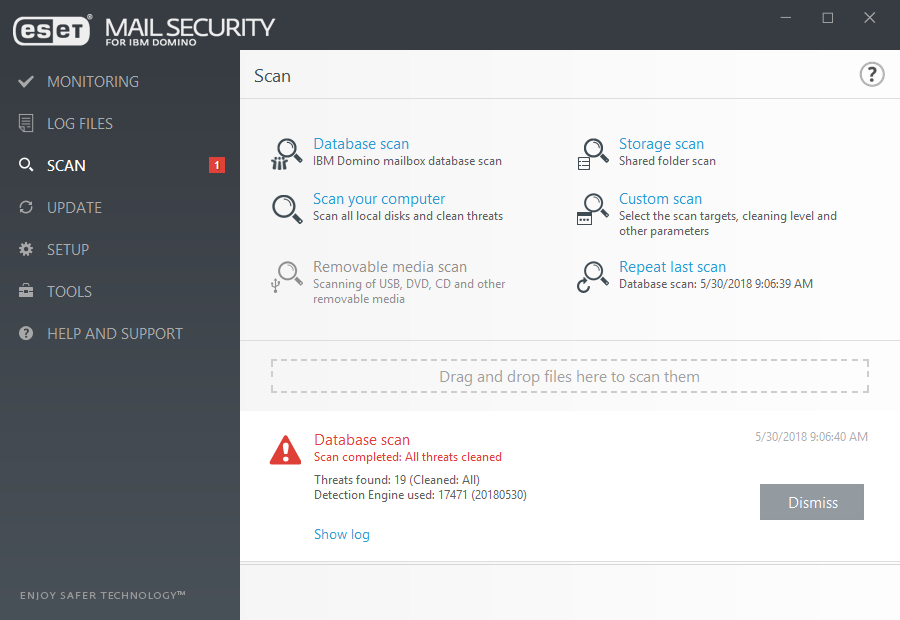
Skeniranje baze podatkov na zahtevo
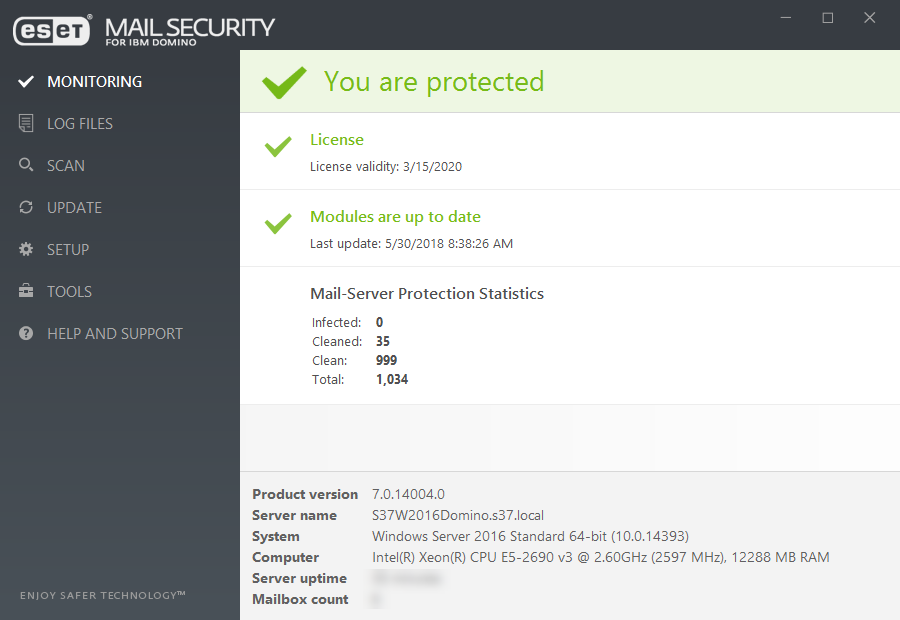
Zaščitena tehnologija
Rešitve ESET Mail Security uporabljajo lastno razvito zaščito proti nezaželeni elektronski pošti, zaščito proti lažnemu predstavljanju in strežniku, ki združuje strojno učenje in človeško znanje v eno nagrajeno platformo za poštno varnost.
Prilagodljiv in fleksibilen
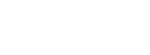
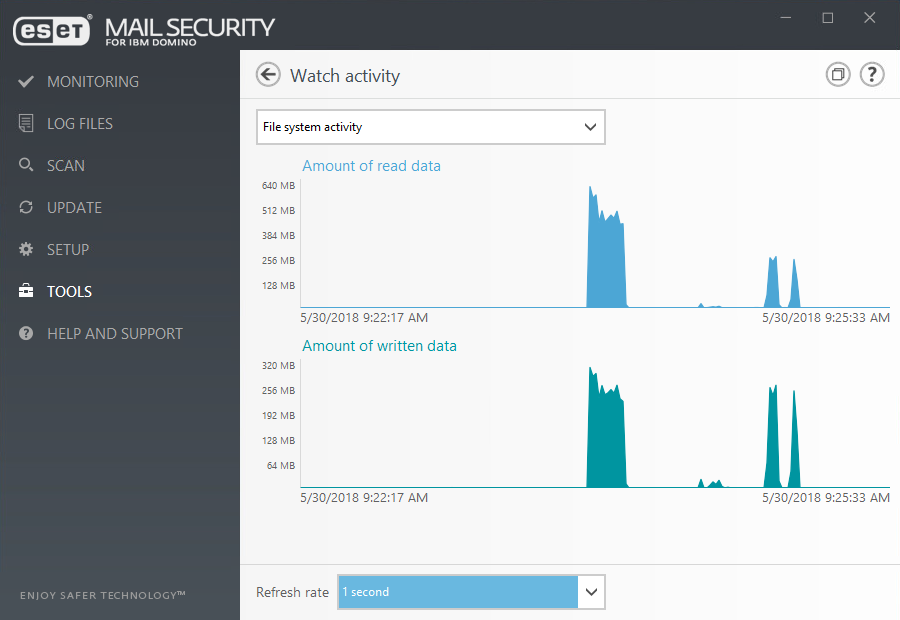
ESET Mail Security omogoča namestitev na podlagi komponente, ki skrbniku omogoča, da izbere le določen del rešitve. Prav tako ESET Mail Security omogoča izključitev določenih predmetov ali procesov od skeniranja ob dostopu s čimer zmanjšuje motnje v procesu in izboljša varnostno kopiranje celovitih procesov.
Use cases
PROBLEM
Users are constantly targeted via phishing campaigns that may contain other malicious components.
SOLUTION
- Early warning system such as ESET Threat Intelligence notifies about a phishing campaign.
- Rules can be implemented in ESET Mail Security to prevent emails from being received from known malicious countries and domains.
- ESET Mail Security uses a sophisticated parser that searches message body and subject line to identify malicious links.
- Any email containing malicious files or links is quarantined and prevented from being received by the users.

protected by ESET since 2017
more than 9,000 endpoints
protected by ESET since 2016
more than 32,000 endpoints
The ESET difference
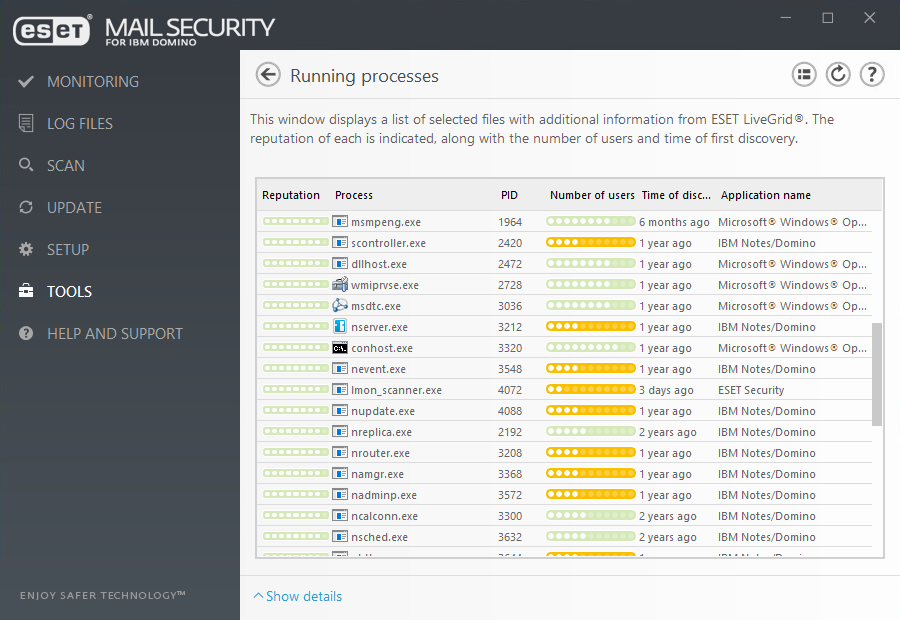
Antispam
Using our own proprietary award-winning engine, spam is prevented from ever reaching your users’ mailboxes. Includes SPF and DKIM validation, backscatter protection and SMTP protection.
Antimalware
Our second layer of protection built into ESET Mail Security provides detection of suspicious or malicious attachments to prevent users from being infected.
Anti-phishing protection
Prevents users from accessing web pages known for phishing by parsing messages body and subjects to identify URLs. URLs are then compared against the phishing database and rules to decide whether they are good or bad.
On-demand database scan
On-demand database scanner provides option to choose the targets to scan. Also, you can use the scheduler to run the database scan at a specific time or at an event.
Rules
ESET’s comprehensive rule system allows administrators to manually define email filtering conditions and actions to take with filtered emails.
Mail quarantine manager
Admin can inspect objects in this special IBM Domino database and decide to delete or release them. This feature offers simple management of emails quarantined by the transport agent.
ESET MAIL SECURITY FOR IBM DOMINO
Make an enquiry
Leave us your contact details to receive an offer tailored to your company's needs.
Try before you buy
Why not download a free trial license with absolutely no commitment on your side.
System Requirements
- Operating systems:
Microsoft Windows Server 2016, 2012 R2, 2012, 2008 R2, 2008 SP2, 2003 R2 SP2
IBM Domino 6.5.4 and newer - Compatible with ESET Security Management Center and ESET Remote Administrator 6. See more information about ESET Remote Administrator compatibility.
Looking for the complete security of your network?
Related bundled solutions
ESET Targeted Attack Protection
- Security Management Center
- Endpoint Protection Platform
- Cloud Sandbox Analysis
- Endpoint Detection & Response
ESET Secure Business
- Security Management Center
- Endpoint Security
- File Server Security
- Mail Security
ESET Secure Business Cloud
- Cloud Administrator
- Endpoint Security
- File Server Security
- Mail Security
ESET Identity & Data Protection
- Two-factor Authentication
- Endpoint Encryption