The cybersecurity landscape of 2026 is defined by AI accelerated attacks, expanding hybrid infrastructures, and unprecedented regulatory pressure. These forces have made the Zero Trust model a best practice as well as an essential architecture for cyber resilience. Organizations worldwide are prioritizing Zero Trust to reduce breach impact, secure identity-driven ecosystems, and improve operational continuity in an era where implicit trust is a liability.
Key points of this article:
- Zero Trust is now a resilience baseline instead of an optional add‑on. AI‑driven attacks, identity sprawl, and hyperconnected cloud ecosystems have made implicit trust a liability.
- Identity is the new perimeter. Compromised credentials remain the leading cause of breaches, and Zero Trust responds by continuously verifying every user, device, and session with least‑privilege access.
- Microsegmentation and monitoring contain damage. Segmenting critical assets and continuously monitoring behavior dramatically reduce lateral movement and breach impact.
- Regulation is accelerating Zero Trust adoption. Frameworks such as NIST SP 800‑207, NIS2, DORA, GDPR, and ISO 27001 increasingly expect Zero‑Trust‑aligned controls.
- SMBs can start small and still benefit. Enforcing MFA, tightening access, and using managed detection and response services provide a practical Zero Trust on‑ramp without requiring a full SOC.
What the Zero Trust model means in 2026?
Think about how a hotel key card works: instead of allowing you to open every door in the building, it opens only your own room door during your stay and it stops working the moment you check out. Traditional network security is the opposite of that. Once you authenticate at the perimeter, you often have access to far more than you need, for as long as you stay connected. Zero Trust flips the model back to the hotel key card setup.
Zero Trust is a modern cybersecurity strategy built on a simple principle: trust no user, device, workload, or service by default, and continuously authenticate and authorize everything. It traditionally leverages tools such as segmentation, identity-and-access controls and visibility, but nowadays goes beyond that.
In 2026, Zero Trust isn’t understood as a single technology but as a continuous risk evaluation framework spanning identity, endpoints, cloud workloads, data flows, and applications. This shift reflects its role as a foundation for wider cyber resilience efforts and hybrid-cloud security.
Why Zero Trust has become a 2026 imperative
16 years after Zero Trust was introduced by John Kindervag, the core risks it set out to solve remain firmly in place, but the threat landscape around them has intensified dramatically as attackers now leverage AI-driven techniques and increasingly hyperconnected environments.
AI driven cyberattacks are scaling faster than ever
Attackers now leverage generative AI for automated phishing, vulnerability discovery, and lateral movement across networks, greatly increasing the speed and precision of intrusions. This makes continuous verification, a core Zero Trust principle, indispensable. The rise of AI automated attacks and the growing influence of quantum computing also underscore why Zero Trust remains a cornerstone of modern security operations.
One of the most widely cited examples of an AI‑enabled intrusion underscoring the importance of Zero Trust is the 2023 breach of MGM Resorts International, a hotel and gaming giant. The group known as Scattered Spider reportedly used AI to replicate an employee’s voice from a public LinkedIn video, then phoned the help desk while impersonating that employee to obtain access credentials.
The incident cost the company an estimated $110 million, including around $10 million spent on technology consulting, legal services, and other third party advisors. The attack illustrated how trusting a familiar voice or what appears to be a legitimate internal request can become a serious point of failure.
Identity sprawl is expanding faster than organizations can control
As organizations expand across cloud and SaaS ecosystems, the volume of human, service, and machine identities has surged. Attackers are exploiting this explosion. According to the 2025 Verizon Data Breach Investigation Report (DBIR), stolen credentials remain the most common initial access vector, appearing in 22% of breaches with a known entry point, narrowly ahead of vulnerability exploitation at 20% and well above phishing at 15%.
Identity abuse becomes even more extreme in specific patterns: within Basic Web Application Attacks, 88% of breaches involve stolen credentials, underscoring how fragile identity trust remains. Meanwhile, Identity Defined Security Alliance (IDSA) research showed that 57% of organizations viewed managing identity sprawl as a major priority in 2024, and only 10% reported no identity‑related incident that year. The remaining 90% experienced at least one identity related security incident, many of which resulted in direct business impact.
This reality makes clear that identity now defines the perimeter, and Zero Trust requires every user and machine identity to be continuously authenticated and restricted to least privilege access. In a more recent case, disclosed in early 2025, attackers used compromised credentials to log into PowerSchool’s “PowerSource” customer support portal. That single stolen login gave them access to data for school districts using the service, affecting 62 million student records—in some cases, spanning four decades of history. The breach shows how one trusted vendor account can open the door to sensitive data across many downstream environments.
Hyperconnected environments have eroded traditional trust boundaries
Modern organizations operate in sprawling, hyperconnected environments where cloud services, APIs, SaaS tools, IoT devices, and third‑party platforms continuously exchange data. The 2025 IBM Cost of a Data Breach Report shows how this complexity expands risk: 30% of breaches involved data distributed across multiple environments, and those incidents were the most expensive, averaging USD 5.05 million. They also took the longest to resolve, with cross‑environment breaches requiring 276 days to identify and contain, which is far more than on‑premises or single‑cloud breaches.
This interconnectedness means one weak integration can expose downstream customers. A clear example came from the Snowflake‑related credential‑theft campaign reported in 2024, where attackers used stolen credentials to compromise around 100 customer accounts and exfiltrated data across multiple cloud tenants. It demonstrated how interlinked SaaS ecosystems can magnify the impact of a single compromised credential.
In such conditions, network location offers no protection. Zero Trust’s insistence on continuous verification and least‑privilege access is the only defensible model for constraining blast radius in a world where everything is connected to everything else.
Core principles of Zero Trust
The following principles stem from a foundational Zero Trust idea: everything is compromised until proven otherwise. When no user, device, or connection is trusted by default, implicit trust, and the attack paths it create, disappear.
1. Assume breach
Design your security posture as if attackers are already inside. This is the most uncomfortable principle for organizations used to trusting their internal network, but it is the one that changes behavior most fundamentally. Assuming breach means encrypting all traffic, including internal traffic between services.
It means treating internal network traffic with the same suspicion as inbound traffic from the public internet. The SolarWinds intrusion persisted for months in part because internal traffic and trusted relationships weren’t scrutinized with the rigor Zero Trust requires. Assuming breach also means segmenting the network so that a compromised account or device in one zone can’t freely access others.
2. Microsegmentation to contain lateral movement
Microsegmentation has shifted from an advanced capability to a baseline Zero Trust requirement. It helps contain ransomware and lateral movement, especially in multi‑cloud and containerized environments.
By breaking the environment into smaller, isolated zones with tightly scoped access rules, microsegmentation ensures that even if attackers gain a foothold, they can’t freely traverse the network. Every workload, service, and data flow is treated as a boundary to be protected, dramatically reducing the blast radius of a breach and aligning day‑to‑day operations with an “assume breach” mindset.
3. Least-privilege access
This principle ensures every identity (human or machine) receives only the minimum permissions necessary to perform its task. A finance analyst doesn’t need access to the engineering codebase, and a contractor brought in for a two-week project doesn’t need permanent credentials. The principle simply applies now uniformly across employees, applications, machine identities, workloads, and APIs, reflecting how expansive modern access surfaces have become.
Just‑in‑time access and real‑time revocation have also become standard, reducing the window of opportunity for attackers who obtain valid credentials. The contractor analogy works here too: you give a contractor a key to the specific room they are working in for the specific days they are on site; you don’t hand them a master key on day one and hope they return it when they leave.
By limiting what each identity can reach or modify, organizations dramatically shrink pathways for lateral movement and reduce the operational impact of inevitable compromise.
4. Continuous monitoring and adaptive policy enforcement
Zero Trust requires a living, responsive control plane—one that evaluates signals continuously and adapts in real time. AI‑enhanced analytics now drive real‑time anomaly detection, automated policy tuning, instant risk scoring, and even autonomous containment actions.
In hybrid and multi‑cloud environments, where conditions shift by the minute, static controls can’t keep up. Continuous monitoring and adaptive enforcement ensure that access decisions evolve with user behavior, device posture, workload context, and emerging threats. This turns Zero Trust from a set of rules into an always‑on decision engine.
Zero Trust architecture: how it actually works
The three core components
NIST SP 800-207 defines the technical anatomy of a Zero Trust architecture around three components that work together on every access request. Since it is a strategic framework, it can be scaled to organizations of any size, including SMBs.
Policy engine
The decision-maker. It evaluates the access request against all available data points, including user identity, device state, threat intelligence, and policy rules, and decides whether to permit or deny. Think of it as the rulebook and the judge combined.
Policy administrator
The enforcer. It executes the Policy Engine's decision by establishing or terminating the access session. It generates and revokes credentials or tokens for the specific session. If the Policy Engine says no, the Policy Administrator closes the door.
Policy enforcement point
The gatekeeper. It sits between the user and the resource, and it intercepts every access attempt, consults the Policy Administrator, and either allows the connection or blocks it. No request reaches the resource without passing through the Policy Enforcement Point.
The hotel key card analogy
In hotel terms, the Policy Enforcement Point is the door lock that reads your key card. The Policy Administrator is the front desk system that programs and revokes key cards. The Policy Engine is the reservation and policy system that decides which room you get and when your key should work.
How a Zero Trust access request works, step by step
A remote employee on their home laptop wants to open the company finance application at 7pm on a Tuesday. Here is what happens under a Zero Trust architecture:
- Request intercepted: The employee clicks the finance app. The request hits the Policy Enforcement Point before anything else happens.
- Context evaluated: The Policy Engine checks: is the user's identity confirmed via multi-factor authentication (MFA)? Is this device registered and compliant? Is 7pm access from this location within the user's normal pattern? Does this user's role permit access to the finance app?
- Risk scored: All signals are weighed. High-risk indicators, such as an unrecognized device or a location that doesn’t match previous logins, can trigger step-up authentication or denial.
- Access granted, scoped, and timed: The Policy Administrator issues session credentials for the finance application only. Not the network, not adjacent applications. The session is time-limited.
- Session monitored continuously: Behavior during the session is logged and analyzed. Unusual activity, large file downloads or accessing screens outside normal workflows can trigger re-verification mid-session or revocation.
The entire process runs in milliseconds. When policies are well-designed, legitimate users experience minimal friction, and additional checks only appear when context signals elevated risk.
How to implement Zero Trust
Zero Trust matures in stages. Full maturity across every pillar is rare, but meaningful progress is achievable for organizations of any size when the work is sequenced correctly.
The most effective programs start where risk is highest and improvements are easiest to measure: identity and device access. Enforcing MFA, tightening access rights, and gaining basic visibility into devices reduce breach exposure faster than almost any other control. Besides, they don’t require rebuilding your entire environment.
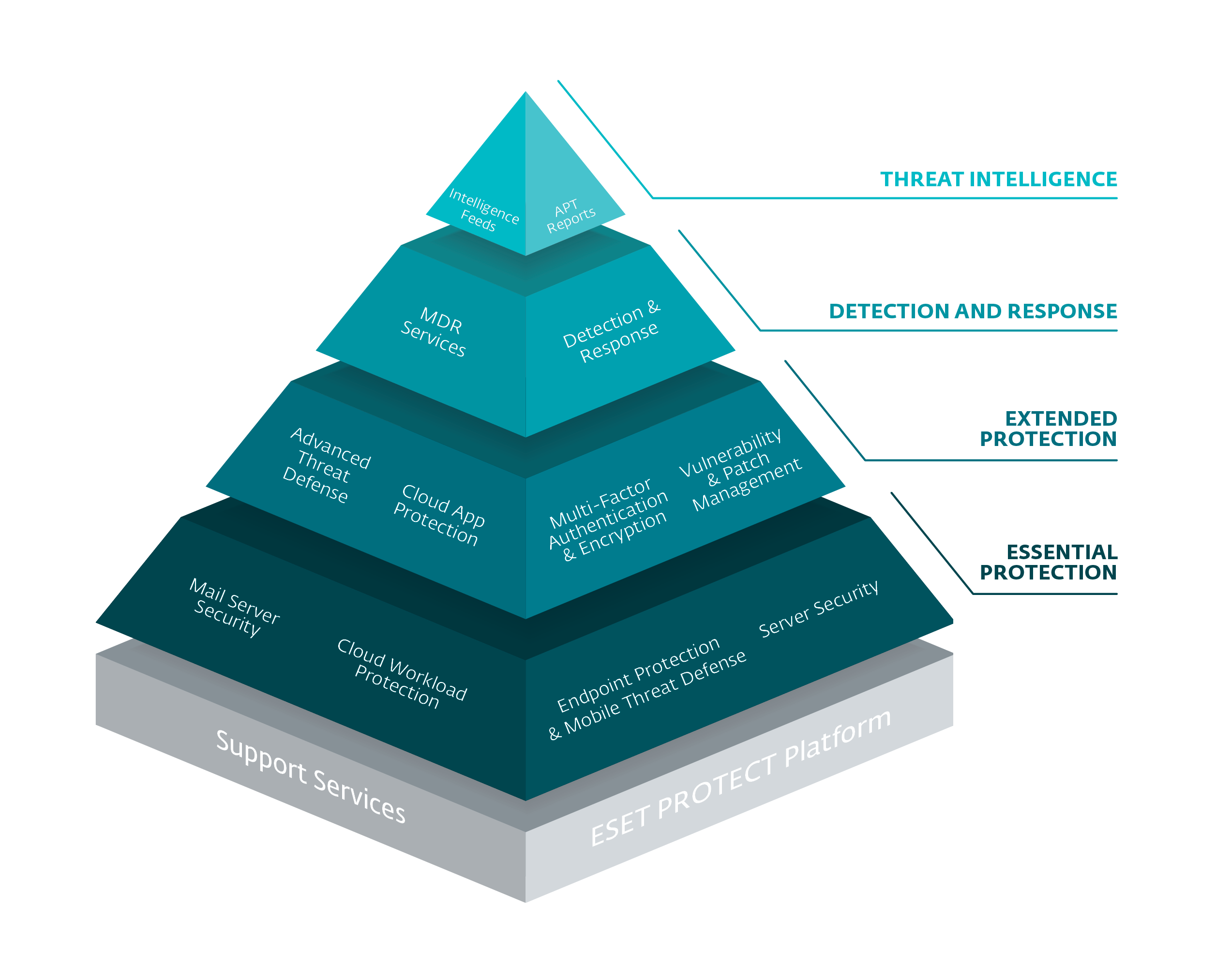
Security matures in layers. Frameworks like the ESET’s IT Security Maturity Model reflect this progression: from basic endpoint protection through zero trust readiness with data encryption, MFA, and cloud sandboxing, toward proactive inspection and anticipatory intelligence with threat monitoring, forensics, and MDR.
Six practical steps to begin Zero Trust
1. Know what you have.
Inventory user accounts, devices, applications, and data sources. Most SMBs uncover forgotten assets and shadow IT here. The first real risk reduction comes from simply knowing your environment.
3. Segment your crown jewels first.
Create small, protected zones around your most critical data, key applications, and admin accounts. Don’t try to segment the whole network; start where compromise would hurt most.
5. Add monitoring you can act on.
Deploy EDR or XDR to detect suspicious behavior and give you visibility you don’t have today. Alerts should be actionable, not noisy.
2. Map who accesses what.
Identify which users access which systems, from where, and under what conditions. This exposes implicit trust paths you’ll later replace with explicit, verified access.
4. Tighten identity and access.
Enforce MFA for every user. Apply role‑based access so people only reach what their job requires, and use privileged access management for admin accounts.
6. Automate where possible.
Use tools that automatically enforce policy, re‑verify high‑risk sessions, and cut off suspicious behavior. Manual enforcement doesn’t scale, especially for small teams.
Zero Trust for small and mid‑sized businesses
Since attackers don’t care about headcount, and the core principles are size‑agnostic, Zero Trust is for organizations of any size. SMBs can make measurable progress without a SOC:
- Enable MFA for all accounts to sharply cut down credential based attacks.
- Apply role‑based access so employees only reach what they genuinely need.
- Use modern endpoint protection with behavioral detection.
- Consider Managed Detection & Response (MDR) to provide 24/7 monitoring your internal team can’t cover.
ESET PROTECT supports this progression: MFA, encryption, and sandboxing at entry levels, and XDR and MDR when you need broader coverage. The path for SMBs to Zero Trust readiness is incremental and achievable.
Regulatory pressure and compliance in 2026
As digital threats evolve and become more systematic, the global regulatory landscape is tightening, which shifted Zero Trust from best practice to compliance expectation. Gartner identifies regulatory volatility as one of the top cybersecurity drivers for 2026, noting that shifting global mandates are elevating cybersecurity into a critical business risk domain.
In this environment, organizations increasingly turn to Zero Trust approaches to demonstrate control, manage compliance obligations, and maintain continuous oversight across distributed environments.
Across jurisdictions, regulators increasingly expect organizations to prove access governance, network segmentation, and identity verification maturity, all of which map directly to core Zero Trust principles.
United States: from guidance to mandate
Zero Trust has become a formal requirement for the US public sector. NIST SP 800‑207, published in 2020, remains the globally referenced Zero Trust architecture standard, offering a vendor‑neutral blueprint for implementation.
Executive Order 14028 (May 2021) and the OMB M‑22‑09 memorandum (January 2022) set FY2024 as the federal deadline for Zero Trust adoption, turning Zero Trust into a compliance obligation for all federal agencies. These mandates historically influence private‑sector adoption as well, accelerating broader business alignment.
Europe: NIS2, CRA, DORA, GDPR, and ISO 27001
In the EU, Zero Trust aligns closely with the requirements of major regulatory frameworks, even when not named explicitly.
- NIS2 obligates organizations to implement “appropriate technical and organizational measures,” including strong access controls, incident detection, and supply‑chain security—capabilities inherent to Zero Trust design.
- Cyber Resilience Act (CRA), which takes effect in late 2026, introduces security‑by‑design requirements for connected products, obligating manufacturers to report actively exploited vulnerabilities and meet strict security standards, with fines reaching up to 2.5% of global revenue for non‑compliance.
- DORA demands rigorous ICT risk management and continuous oversight for financial entities, reinforcing Zero Trust expectations around identity, segmentation, and monitoring.
- GDPR Articles 5 and 25 (data minimization and privacy‑by‑design) naturally align with Zero Trust’s least‑privilege and data‑centric controls.
- ISO/IEC 27001:2022 strengthens expectations for access management, cryptography, and continuous monitoring, again mirroring Zero Trust operational principles.
Why Zero Trust strengthens compliance outcomes
Zero Trust architectures provide what regulators increasingly demand:
- Granular logs for auditability
- Explicit access policies backed by evidence
- Continuous monitoring to demonstrate ongoing control
- Segmentation to limit blast radius and reduce systemic risk
As cyber regulations mature globally, Zero Trust is becoming both strategic security model and a compliance framework—one capable of proving that organizations are actively governing identities, access paths, systems, and data across hybrid, multi‑cloud, and SaaS ecosystems.
Zero Trust challenges: what to expect
Most guides on Zero Trust skip this part, yet it’s where real programs succeed or fail. The practical challenges are well documented by independent research.
Identity governance remains the biggest obstacle. Verizon’s 2025 DBIR shows that 33% of breaches in SMBs stemmed from compromised credentials in 2025, and in web applications the number climbed from 77% in 2024 to 88% in 2025, highlighting how difficult it remains for organizations to enforce strong, consistent identity controls across users and systems.
Technical complexity and multi-cloud sprawl create additional friction. IBM’s 2025 Cost of a Data Breach Report notes that security‑system complexity increases breach costs by more than $200,000, and that breaches involving data spread across multiple environments are the slowest to contain (276 days). These are signals that many organizations, including SMBs, struggle to retrofit Zero Trust controls into fragmented environments.
Operational alignment is another barrier. Research from the Cloud Security Alliance finds that while organizations often list Zero Trust and least‑privilege as priorities, governance, measurement, and cross‑team coordination lag behind, making it difficult to sustain progress beyond initial pilots.
None of this means Zero Trust isn’t worth pursuing. It simply means expectations need to match reality: the most successful organizations start with a specific problem, deploy controls that measurably solve it, and expand from there rather than trying to tackle everything at once on day one.
User experience remains critical. Poorly Zero Trust strategy creates authentication fatigue, while a well-designed strategy uses risk‑based adaptive policies: low risk actions stay smooth, and higher risk behaviors trigger step up verification. The goal is to make unauthorized access harder while keeping legitimate access natural.
The bottom line on challenges
Start where the impact is highest: identity controls and endpoint visibility. Build a phased roadmap. Measure progress against the CISA maturity model or ESET’s IT Security Maturity Model. And most importantly, treat Zero Trust as an ongoing discipline instead of a project with an end date.
Business benefits of Zero Trust in 2026
Despite the challenges, modern Zero Trust programs deliver clear, resilience driven outcomes:
- Reduced ransomware and breach impact: Microsegmentation, identity hardening, and continuous verification sharply limit lateral movement and reduce the scope of incidents.
- Improved cloud security: Zero Trust enables consistent access control and policy enforcement across hybrid and multi cloud environments, reducing misconfiguration driven exposures.
- Stronger compliance posture: Regulatory bodies increasingly expect Zero Trust aligned controls, making the model a natural accelerator for demonstrating governance and audit readiness.
- Enhanced operational resilience: With executive accountability rising, Zero Trust strengthens governance, reporting, and visibility—helping organizations anticipate, absorb, and recover from disruptions more effectively.
Start your Zero Trust journey with ESET
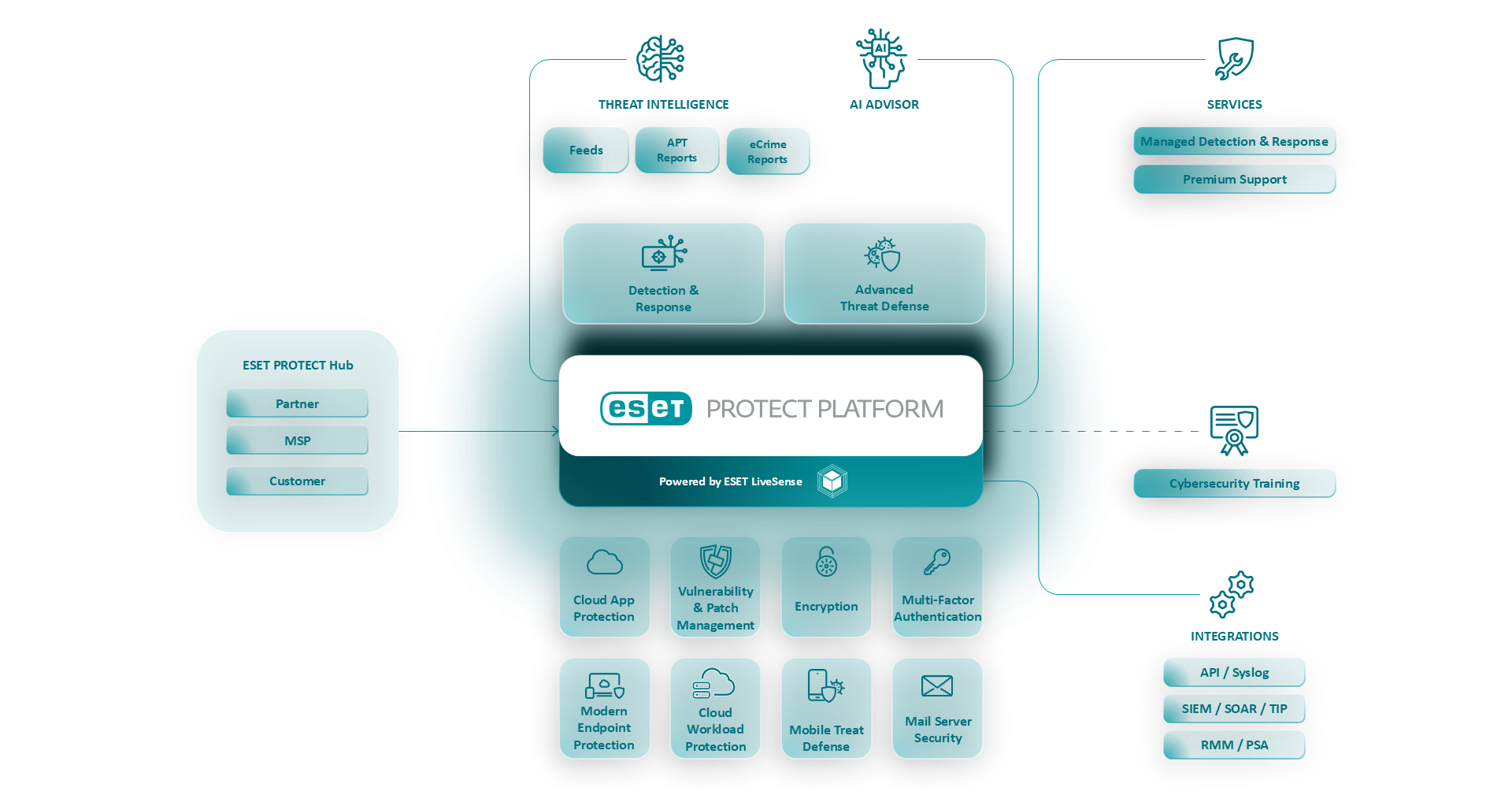
As we already discussed, Zero Trust is a strategy, but you still need practical tools to make it real. ESET PROTECT is designed to do exactly that, aligning to the three core Zero Trust pillars: continuous verification, least‑privilege access, and an assume‑breach mindset.
For continuous verification, ESET PROTECT MDR provides 24/7 monitoring, detection, and response, and delivers the XDR capabilities needed for deep endpoint visibility and behavior analysis. ESET LiveGuard Advanced adds cloud‑based, real‑time analysis of new and unknown threats via sandboxing, while ESET Threat Intelligence identifies and blocks malicious infrastructure before it reaches your network. Together, these tools provide the deep visibility and proactive insights needed to maintain a prevention‑first security posture.
To enforce least‑privilege access, ESET Secure Authentication delivers strong MFA, ESET Full Disk Encryption protects data on devices, and the ESET PROTECT Console enables centralized, role‑based access and consistent policy enforcement across endpoints, servers, and mobile devices.
For an assumed‑breach, breach‑ready response, ESET PROTECT MDR offers 24/7 managed detection and response with expert analysis and proactive threat hunting. Multilayered endpoint and server protection, combined with ESET Vulnerability & Patch Management and ESET Cloud Office Security, help close exploitable gaps and protect collaboration platforms from phishing, malware, and business email compromise.
Combined with ESET’s IT Security Maturity Model, these capabilities let you start from where you are today and grow Zero Trust controls at a pace that fits your team and your budget.
Building a resilient Zero Trust environment with ESET
Conclusion: Zero Trust is the cyber resilience standard of 2026
As organizations face AI‑enabled attacks, regulatory pressure, and increasingly complex hybrid environments, Zero Trust has evolved from a concept into the reference architecture for modern cybersecurity. It addresses the structural weaknesses exposed by identity sprawl, hyperconnected ecosystems, and fragmented tooling—not with a single product, but with a strategy grounded in continuous verification, least‑privilege access, and an assume‑breach mindset.
The path is iterative, and most organizations will spend years maturing across identity, devices, networks, applications, and data. But starting with identity controls, segmentation around critical assets, and monitoring you can act on already delivers measurable risk reduction.
Whether you have in-house personal or technical capabilities, or partner with platforms such as ESET PROTECT Platform for XDR, MDR, and Zero‑Trust‑aligned controls, the direction of travel is the same. Zero Trust is the strategic security model that lets businesses adapt, survive, and grow in an unpredictable digital environment.
FAQ
What is the concept of Zero Trust?
Zero Trust is a security model based on the principle that no user, device, or application is trusted by default, whether inside or outside the network. Every access request is verified, authenticated, and authorized in real time before access is granted. Trust is never assumed; it is continuously earned based on context and risk signals.
What are the three principles of Zero Trust?
The three principles, defined in NIST SP 800-207, are: Verify explicitly, meaning authenticate and authorize every request using all available data points; Use least privilege access, meaning grant only the minimum access needed for the specific task and only for as long as needed; Assume breach, meaning design security as if attackers are already inside and minimize the damage they can do. In this article, we expand on these foundations with four practical principles for 2026 implementations.
What are the 5 pillars of Zero Trust?
The CISA Zero Trust Maturity Model (2023) defines five pillars: Identity, Devices, Networks, Applications and Workloads, and Data. Each pillar represents a technology domain where Zero Trust principles must be applied. Most organizations start with Identity because it delivers the fastest return on investment.
What is the difference between Zero Trust and a VPN?
A VPN authenticates a user and grants them access to the network. Zero trust as a strategic model authenticates a user and grants access to a specific application, continuously verified based on identity, device state, and context. A compromised VPN account can move laterally across the network. A compromised account under Zero Trust is restricted to the specific apps it was verified to access, with behavior monitored throughout the session.
Is Zero Trust the same as ZTNA?
No. Zero trust is a security strategy, an architectural philosophy. Zero Trust Network Access (ZTNA) is a technology category that implements Zero Trust principles for application access control. ZTNA is one enabling technology within a broader Zero Trust programme. Other enabling technologies include MFA, endpoint detection and response (XDR), identity and access management, and micro-segmentation.
Does Zero Trust work for small businesses?
The principles scale to any organization size. Small businesses can make meaningful Zero Trust progress by enforcing MFA on all accounts, applying role-based access control, deploying endpoint protection with behavioral detection, and using a managed detection and response (MDR) service for continuous monitoring without requiring an in-house security team. Starting with identity controls is both the most accessible and the highest-impact entry point.
What is the NIST Zero Trust framework?
NIST Special Publication 800-207, published in August 2020, is the definitive, vendor-neutral reference for Zero Trust architecture. It defines the core components of a ZTA (Policy Engine, Policy Administrator, Policy Enforcement Point), outlines the three foundational principles, and provides implementation guidance applicable across sectors and organization sizes. It is the document all








