In the current AI era, cyberthreats are evolving so quickly that even blog posts only a few weeks old can become outdated in the blink of an eye. During Black Friday 2025, we wrote about new threats targeting Android users ahead of the shopping season and, oh boy, it looks like it’s time to update the list.
Since then, ESET researchers have identified new AI‑powered threats as well as updates to known malware families. These improvements make malicious apps and campaigns significantly harder for both humans and automated systems to detect. Unfortunately, these dangers aren’t limited to high-profile government or enterprise targets. Everyday Android users can encounter these threats while browsing the internet or checking social media.
In this rapidly shifting threat landscape, it has never been more important to rely on cutting‑edge AI-powered cybersecurity solutions ... fighting fire with fire, sort of. Above all, proactive protection is essential to stop threats before they can steal users’ data or money.
Key points of this article:
- ESET researchers have seen notable advancements in Android threats, with cybercriminals developing new AI-powered techniques and increasingly sophisticated scams.
- ESET researchers have recently uncovered the first known case of Android malware using generative AI to maintain persistence on a compromised device – preventing the user from closing or disabling it.
- The NGate attack scenario, which abuses near‑field communication (NFC) technology used for contactless payments, is growing in both volume and sophistication. Complex, multi‑stage scams can now rely on more capable malware to improve their success rate.
- The notorious Nomani scams, which use deepfakes to promote fraudulent services and products, have become harder to detect as more advanced AI tools enhance the realism of manipulated content.
- As the public becomes more aware of common cyberthreats and scam indicators, attackers are adjusting their tactics to avoid triggering typical red flags. Facing these evolving threats, Android users need a reliable, AI‑powered cybersecurity solution capable of detecting even novel attack methods.
AI-powered malware is studying your screen on the fly
Recently, ESET researchers uncovered the first known case of Android malware that abuses generative AI to analyze the screen activity of a compromised smartphone. ESET researchers presume that the malware could be distributed as a fake banking app.
Dubbed PromptSpy, this malware family spies on the device by capturing lock‑screen data, gathering device information, taking screenshots, recording screen activity as video, and more. It includes a Virtual Network Computing (VNC) module that allows attackers to view the victim’s screen in real time and remotely perform taps, swipes, and text input as if they were physically holding the phone. This is only possible if the victim is tricked into manually enabling accessibility services.
As for the AI-powered aspect, it helps keep the malicious app running. To avoid being closed, the malware keeps itself pinned in the recent apps list by executing the “lock app in recent apps” gesture. Because this gesture differs between devices and manufacturers, writing universal code for it is challenging, but the AI portion helps the attackers bypass this exact limitation.
How? Well, PromptSpy sends Google Gemini a prompt containing the current screen setup, specifically the recent apps list, giving the AI a detailed view of every user interface element, such as text, type, and exact position on the display. Based on this information, Gemini returns precise, step‑by‑step instructions that tell the malware where to tap to remain pinned in the recent apps list.
Description: ESET senior malware researcher Lukáš Štefanko summarizes this newly discovered threat.
Money-stealing attacks combine multiple scams
During the summer of 2024, ESET researchers published a blog about a new attack scenario combining social engineering with the NGate malware, which abuses near-field communications (NFC) technology used for contactless payments.
The attack was notable for using the following stages and techniques:
Phishing – The victims received SMS messages about a tax return that included a link to a phishing website.
Impersonation – The website was impersonating a bank, and most likely tried to trick the victim into installing a data-stealing Progressive Web App (PWA), an app built using web platform technologies.
Malware – Once the victim installed the app and typed in their credentials, the attacker instantly gained access to the victim’s account.
Fake tech support – The attacker then called the victim, pretending to be a bank employee and informing them that their account had been compromised. To “solve” the problem, they advised the victim to install another app – loaded with the unique NGate malware.
Malware/data theft – ESET researchers suspect that within the NGate app, the victims would enter their old PIN to create a new one and place their card at the back of their smartphone to verify or apply the change, effectively sending this data to the attackers as well.
Execution – With card PIN codes and NFC data, cybercriminals could facilitate unauthorized ATM withdrawals from the victims’ bank accounts.
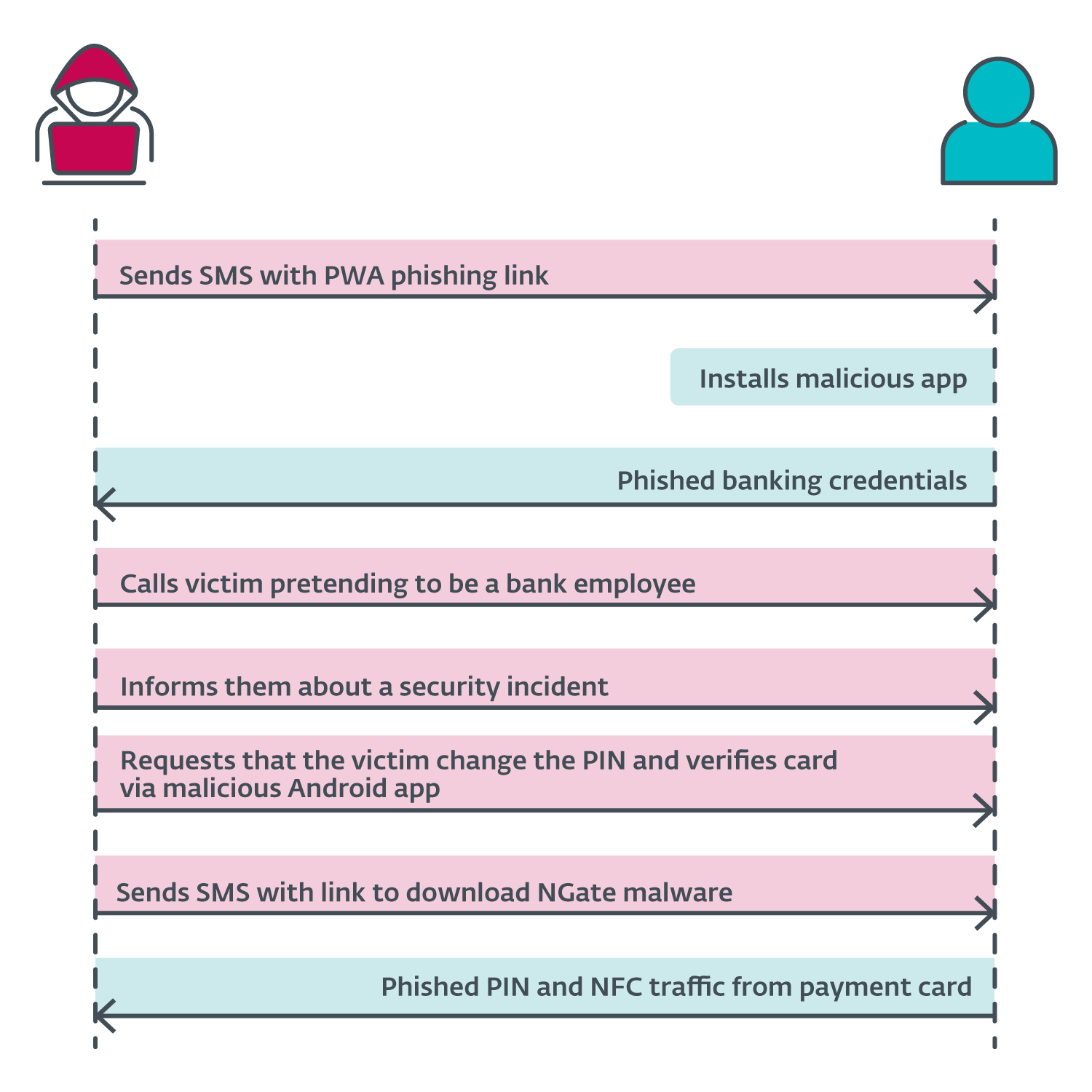
image 1. The specific attack scenario for the 2024 NGate malicious campaign
Since then, ESET experts have seen multiple, more sophisticated variations of this attack scenario.
In fact, one of the latest upgrades was spotted by ESET researchers in late 2025. This version can also harvest saved contacts – a previously undocumented functionality of this malware. ESET researchers believe that contact harvesting is supposed to increase the success rate of the fake support calls, with them expecting new waves of NFC-related attacks as a result.
But that’s not all. The latest ESET Threat Report also highlights the RatOn malware, first identified by ThreatFabric. This mega-hybrid malware combines NFC fraud with multiple malicious features:
Remote control – The malware tricks victims into granting accessibility service access, device admin privilege, and more, allowing the attackers to perform malicious actions remotely.
Accessibility service abuse – Using this access, attackers can grant themselves additional permissions within the compromised device, such as to read/write contacts and manage system settings.
Overlay attacks + ransomware-like capabilities – The malware can place a fake screen layer over the real one, informing the victim that they need to pay a $200 cryptocurrency ransom to unlock their phone.
Automated Transfer System (ATS) capabilities – The malware can interact directly with legitimate banking apps and cryptocurrency wallets without the user’s knowledge to make illegitimate transactions.
NFC-related threats have been evolving, not only in sophistication but also in scale. At first, ESET researchers detected the astronomic thirtyfold-plus growth in H1 2025, and the number of detections is still rising – ESET telemetry shows that the detections grew by 87% between H1 and H2 2025.
“We expect that the appetite of threat actors for exploiting NFC technology will continue to grow in 2026, leveraging NGate or similar malware, and adopting techniques and social engineering approaches used by other cybercriminal groups,” says Lukáš Štefanko, ESET senior malware researcher.
Nomani scams are more advanced and harder to spot
In 2024, social media platforms were flooded with scam ads promoting “secret” investment opportunities, miraculous dietary supplements, and bogus legal or law enforcement assistance. To increase credibility, cybercriminals misused brands of well-known local and global companies and deployed AI-generated deepfake videos featuring famous personalities.
“One million dollars in your trading account in just six months,” claims a deepfake of Elon Musk in one of these fraudulent ads.
The main goal of these fraudsters is to lure victims to phishing websites and online forms designed to harvest personal information. ESET researchers named this scam cluster Nomani, short for “no money,” because, as the name suggests, victims are left with no miraculous investment returns, only no money.
A year later, ESET telemetry shows that this deceptive activity has continued to grow, rising another 62% year over year and reaching hundreds of thousands of detections worldwide, with more than 64,000 unique URLs blocked throughout 2025.
Description: Join ESET Security Awareness Specialist Ondrej Kubovič as he uncovers the Nomani scam: deepfake versions of famous personalities making false promises!
Since their initial discovery, Nomani scams have seen several notable upgrades:
- Deepfakes now appear in higher resolution with fewer unnatural movements and more natural breathing, along with improved audio–video synchronization – all of which make them increasingly difficult for users to recognize as fake.
- Ad content and associated phishing pages now frequently mirror current events and news trends, increasing their relevance and impact.
- To evade detection by social media advertising systems, scammers drastically shorten the lifespan of their campaigns to just a few hours and use tracking mechanisms to redirect users to benign “cloaking” pages when they don’t fit the targeted profile.
- Attackers increasingly abuse legitimate advertising tools, such as built-in forms and surveys, instead of linking to external phishing sites – reducing their traceability while still collecting sensitive data.
- Phishing website templates have also improved, with more polished language and design. Their HTML code increasingly shows signs of AI-generated elements.
How can you protect Android smartphones in the AI era?
As you can see, even sophisticated AI-powered attacks require some degree of human interaction. This means the first line of defense remains human awareness and caution:
- Don’t trust “miracle” offers – some things are just too good to be true. Deepfakes are clearly improving, but their content is still full of red flags. A famous personality promoting a miraculous investment, diet pill, or legal service is a classic one.
- Stay calm during unexpected or urgent calls. Always verify the caller’s identity directly with the institution they claim to represent. High‑pressure tactics, requests for sensitive data, or demands for payment in hard‑to‑trace ways (like cryptocurrencies) are strong indicators of fraud.
- Try not to download apps outside of official app stores. Double‑check details, such as the domain name, contact information, the “About Us” page, and user reviews to avoid copycat sites distributing malware.
- Review app permissions carefully. Be cautious when an app requests access (including accessibility settings) it doesn’t seem to need (for instance, a banking app shouldn’t require access to your contacts); unnecessary permissions are usually a sign of malicious behavior.
- Learn to recognize signs of device compromise. Repeated and unusual overheating, rapid battery drain, strange pop-ups, or apps you didn’t install willingly can all signal malware activity.
Malware can sneak onto your device and cause chaos in your digital life and beyond. Learn how to spot the signs and protect your phone from any future attacks.
As a second line of defense, you need reliable cybersecurity protection that can recognize even threats that have never been seen before and stop attacks at early stages before they can do any harm.
ESET Mobile Security for Android uses advanced AI antimalware technologies to identify and stop emerging threats, including new malware families such as the recently uncovered PromptSpy.
How ESET can protect your device:
AI-Powered Antimalware – If scammers try to trick users into downloading and installing malware, ESET Mobile Security can protect them against malicious app installs and other malware. The antivirus can also check all files and device folders available via USB On-The-Go connections.
Anti-Phishing – ESET Anti-Phishing protects against malicious websites delivering malware or attempting to acquire your sensitive information, such as usernames, passwords, banking information, or credit card details, on most popular Android browsers.
ESET Anti-Phishing includes web browser protection, social application protection, SMS/notification protection, and the Link Scanner, which can recognize phishing links coming from apps.
Payment Protection – This feature adds an extra layer of security to apps like Google Pay or your mobile banking app. When active, Payment Protection prevents malicious apps from reading, modifying, or overlaying content on your protected apps.
Adware Detector – This tool identifies intrusive adware masquerading as harmless apps (e.g., calculators or flashlights) that display full‑screen ads even when not in use.
Call Filter – This tool provides another layer of protection against spam and scam calls. Call Filter allows users to create customized rules for blocking and filtering incoming calls.
Staying protected as Android threats evolve
From new AI‑powered malware like PromptSpy to increasingly sophisticated NFC‑based attacks and harder‑to‑spot Nomani scams, these real‑world examples highlight how cybercriminals are escalating their efforts to deceive users and steal data or money.
While human awareness remains the first line of defense, having a reliable cybersecurity solution capable of detecting never‑before‑seen threats is more essential than ever before.
Frequently asked questions (FAQs)
What are the newest Android threats emerging in the AI era?
Cyberthreats targeting Android devices are evolving rapidly. These threats are also driven by advances in artificial intelligence. ESET researchers have identified new AI‑powered malware, upgraded scam techniques, and more sophisticated social‑engineering attacks. These threats are harder for both users and automated systems to detect, making proactive protection essential.
What is PromptSpy, and why is it significant?
PromptSpy is the first known Android malware abusing generative AI for context-aware user interface manipulation in order to stay persistently active. It collects sensitive information, captures screenshots, records the screen, and more. AI works to maliciously keep it pinned in the recent apps list by interpreting screen elements and generating precise tapping instructions.
How do NFC‑based attacks like NGate and RatOn work?
NFC‑related fraud is growing in both scale and sophistication. Attackers often combine multiple scams – such as phishing, impersonation, fake tech‑support calls, and malicious apps – to access victims’ bank accounts. The key element here is NFC data cloning, enabling unauthorized ATM withdrawals.
What are Nomani scams, and why are they harder to detect now?
Nomani scams are deceptive online ads that promote fake investment opportunities, miracle cures, or legal services. They frequently use AI‑generated deepfake videos of celebrities to build credibility. These scams have become harder to spot due to higher‑quality deepfakes, better‑designed phishing pages, shorter ad lifespans, and the use of legitimate advertising tools such as built‑in forms instead of external links.
How can Android users protect themselves from these AI‑powered threats?
While awareness remains the first layer of defense, users also need modern security tools that can detect new and unknown threats. Best practices include downloading apps only from official stores, verifying unexpected calls, reviewing app permissions, and watching for signs of device compromise. Solutions like ESET Mobile Security for Android provide AI‑powered antimalware, anti‑phishing, payment protection, adware detection, and call filtering to block advanced attacks early.