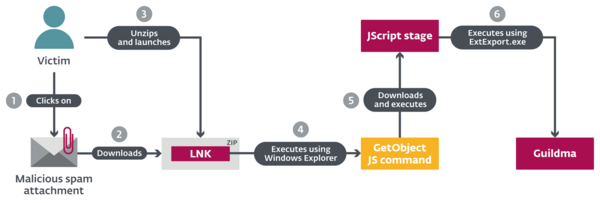
BRATISLAVA, PRAGUE – In the latest installment about Latin American banking trojans, ESET researchers take a deep look at the most impactful and advanced banking trojan we have seen in this series and in the region: Guildma. This malware is specifically targeting banking institutions and attempts to steal credentials for email accounts, e-shops and streaming services in Brazil. It affects at least 10 times as many victims as other Latin American banking trojans that ESET Research has analyzed. During its peak – a massive campaign in 2019 – ESET recorded up to 50,000 attacks per day. Guildma spreads exclusively via spam emails with malicious attachments.
In one of its latest versions, Guildma employs a new way of distributing command and control servers, abusing YouTube and Facebook profiles. However, the authors stopped using Facebook almost immediately and, at least at this time, are relying fully on YouTube.
“Guildma uses very innovative methods of execution and sophisticated attack techniques. The actual attack is orchestrated by its C&C server. This gives the authors greater flexibility to react to countermeasures implemented by the targeted banks,” explains Robert Šuman, the ESET researcher leading the team analyzing Guildma.
Guildma boasts a backdoor with multiple functionalities, including taking screenshots, capturing keystrokes, emulating keyboard and mouse, blocking shortcuts (such as disabling Alt + F4 to make it harder to get rid of fake windows it may display), downloading and executing files, and/or rebooting the machine. In addition, Guildma is very modular and currently consists of at least 10 modules. The malware uses tools already present on the machine and reuses its own techniques. “New techniques are added every once in a while, but for the most part, the developers seem to simply reuse techniques from older versions,” says Šuman.
In one of the earlier 2019 versions, Guildma added the capability to target institutions (mainly banks) outside of Brazil. Despite that, over the past 14 months, ESET has not observed any international campaigns outside Brazil. The attackers went as far as to block any downloads from non-Brazilian IP addresses.
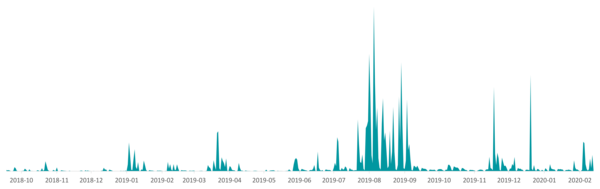
Guildma campaigns were ramping up slowly until a massive campaign in August 2019, when ESET Research recorded up to 50,000 samples per day. This campaign went on for almost two months and accounted for more than double the amount of detections seen in the 10 months prior.
The trojan has seemingly gone through many versions during its development, but there was usually very little development between versions due to its clunky architecture.
Guildma shares several prevailing characteristics of Latin American banking trojans. For more technical details, read the blog post Guildma: The devil drives electric on WeLiveSecurity. Make sure to follow ESET Research on Twitter for the latest news from ESET Research.
About ESET
For more than 30 years, ESET® has been developing industry-leading IT security software and services for businesses and consumers worldwide. With solutions ranging from endpoint and mobile security to encryption and two-factor authentication, ESET’s high-performing, easy-to-use products give consumers and businesses the peace of mind to enjoy the full potential of their technology. ESET unobtrusively protects and monitors 24/7, updating defenses in real time to keep users safe and businesses running without interruption. Evolving threats require an evolving IT security company. Backed by R&D centers worldwide, ESET is the first IT security company to earn 100 Virus Bulletin VB100 awards, identifying every single “in-the-wild” malware without interruption since 2003. For more information, visit www.eset.com or follow us on LinkedIn, Facebook, and Twitter.