BRATISLAVA - The Dukes (aka APT29 and Cozy Bear) briefly stole the spotlight after their suspected involvement in the breach of the Democratic National Committee in the run-up to the 2016 US elections. After an attack in Norway in January 2017 and despite a suspected comeback in November 2018, the Dukes seemingly vanished from the cyberespionage scene. However, ESET researchers have discovered an operation dubbed “Ghost,” which started much earlier, in 2013, and is still ongoing. The Dukes have infiltrated an EU Member State’s embassy in Washington, DC, and Ministries of Foreign Affairs in at least three different countries in Europe.
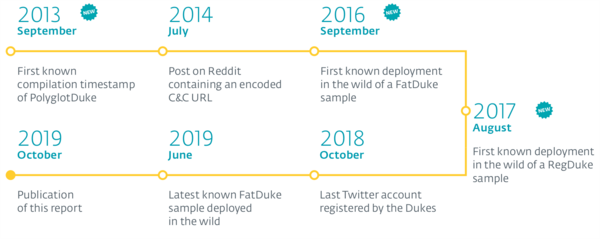
ESET has identified three new malware families associated with the Dukes – PolyglotDuke, RegDuke and FatDuke. “One of the first public traces of this campaign can be found on Reddit in July 2014,” says ESET researcher Matthieu Faou. “We can confirm with high confidence that the same group is behind Operation Ghost and the DNC attack,” he adds.
The attribution of these attacks to the Dukes is based on several similarities in the tactics observed in this campaign, as compared with previous ones. Specifically, the Dukes have used Twitter and Reddit to host Command & Control URLs and have employed stenography in pictures to hide malicious payloads or commands. Moreover, Ministries of Foreign Affairs have continued to be targeted – two of the three targets were previously compromised by the group, with at least one machine having the “old” Dukes still installed from several months before. Further proof is indicated by the strong code similarities between already documented samples and Operation Ghost.
“In 2013, at the first known compilation date of PolyglotDuke, only MiniDuke had been documented, and thus, we believe Operation Ghost was running simultaneously with the other campaigns, and has flown under the radar until now,” explains Faou.
In Operation Ghost, the Dukes have used a limited number of tools, but they have relied on numerous interesting tactics to avoid detection. The Dukes are very persistent, and are systematically stealing credentials and using them to move laterally in the network. ESET has seen them using administrative credentials to compromise or re-compromise machines in the same local network.
The Dukes have a sophisticated malware platform, which is divided into four stages. First, it fetches its C&C URL via Twitter or other social networks and websites. Second, it uses Dropbox to receive commands from the attackers. Third, it drops a simple backdoor, which in turn, drops a more sophisticated backdoor in the last stage with a lot of functionalities and a flexible configuration.
For more details, read the blogpost, “Operation Ghost: The Dukes aren’t back – they never left” and find a detailed whitepaper here. Make sure to follow ESET research on Twitter for the latest news from ESET Research.
About ESET
For 30 years, ESET® has been developing industry-leading IT security software and services for businesses and consumers worldwide. With solutions ranging from endpoint and mobile security to encryption and two-factor authentication, ESET’s high-performing, easy-to-use products give consumers and businesses the peace of mind to enjoy the full potential of their technology. ESET unobtrusively protects and monitors 24/7, updating defenses in real time to keep users safe and businesses running without interruption. Evolving threats require an evolving IT security company. Backed by R&D centers worldwide, ESET became the first IT security company to earn 100 Virus Bulletin VB100 awards, identifying every single ‘in-the-wild’ malware without interruption since 2003. For more information, visit www.eset.com or follow us on LinkedIn, Facebook and Twitter.