In part one, I looked at some of the threats surrounding the use of hot wallets, specifically, clippers and fake login pages. These threats are particularly lethal due to the fact that hot wallets are always connected to the internet. Here, I continue my overview of the cryptocurrency wallet threat landscape by taking a look at malware-laced links as another top danger to hot wallet users, along with some security considerations relevant for cold wallet users.
Bad links and more bad links
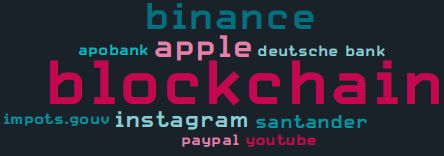
Have you ever clicked on a link that looked like “blockchain.com” but turned out to be something else? This is called a homoglyph attack. By replacing certain characters in the domain name with ones that either look similar or identical to human eyes (but are actually different to computers), phishing operators can craft links that appear to lead to popular websites that actually resolve to malicious sites. ESET telemetry for Q2 2020 showed attackers were focusing on cryptocurrency exchanges with blockchain.com and binance.com being the most targeted domains:
Without a security solution like ESET Internet Security installed on my machine, or short of a detective’s eye for picking up on the character switch — a highly unlikely event — nothing would stop me from getting phished.
Phishing can also happen via another, very typical path — spam emails attempting to clog my inbox. Clicking on malicious links in these spam messages and potentially giving banking trojans, such as Mekotio, a chance to do damage on my PC is quite unwelcome. Some variants of Mekotio, for example, attempt to steal bitcoins by replacing the bitcoin wallet address in the clipboard.
If I never copy and paste my wallet address, well, a keylogger is standard equipment for a lot of malware. So again, if it weren’t for my Banking & Payment Protection, packaged as part of my ESET Internet Security solution for protection against keyloggers, I would have much less confidence when typing in my wallet address via a browser.
Before leaving the topic of bad links, if you are still using torrents to download cracked or pirated software and games and then switching over to an exchange to do a little crypto trading, think again. As one more deterrent against the use of torrent sites, malware like KryptoCibule is found on some of these platforms. KryptoCibule tries to hijack cryptocurrency transactions by replacing wallet addresses in the clipboard and exfiltrating any cryptocurrency-related files it finds on the victim’s machine.
Cold wallets — limiting the threats to a physical playing field
As the more well-versed crypto traders are aware, the best way to minimize the dangers that beset the use of hot wallets is to use a cold wallet. Two popular options are Ledger and Trezor. By creating an air gap between your wallet and the internet, the risks take on a predominantly physical outlook.
There is the obvious risk of losing your cold wallet, having it stolen or, less likely but possible, tampering occurring along the supply chain. Then, in the hands of knowledgeable hardware hackers, both Trezor and Ledger have been coaxed to give up the key and recovery phrase.
While using cold wallets decreases numerous cyber risks, the parallel decrease in ease of use can still remain a bit of a sore tooth for some. And our “friendly” malware operators have just the solution to soothe that pain — Google Chrome extensions and Firefox add-ons that integrate your Ledger wallet with the browser. So, back to the world of hot wallets.
“Now, you can access wallet functionality directly from your browser to quickly and easily make cryptocurrency transactions. All you have to do is share your 12/24-word recovery phrase to sign up.” You can easily guess the glib words that these hackers might use to persuade potential victims.
After sharing your recovery phrase, the attackers can quickly clone your hardware wallet and take over your crypto-assets. Total losses for this type of scam exceed $250,000, according to some reports. ESET detects these threats as JS/ExtenBro.CryptoSteal.
Recommendations
1. Keep your devices updated and always use a reliable security solution, such as ESET Internet Security or ESET Mobile Security, to protect them from the latest threats.
2. If you’d like to download a cryptocurrency wallet app, first make sure your selected service really offers a mobile, desktop or online wallet by checking the service’s official website.
3. When downloading mobile wallet apps from Google Play, review the number of downloads, the app ratings and reviews. Be cautious of newly published apps with positive reviews that seem too good to be true.
4. Where the option is available, always use multifactor authentication to protect your wallet accounts with an extra layer of security.
5. Think twice about where you are sharing your wallet recovery phrase and key.
6. Type your wallet address, instead of copying and pasting it, and double-check the address before using it.
7. Determine whether the app provider offers insurance/consumer protection against coin losses.
Considering e-trading? Many of these practices are relevant there too. Have a read about e-trading and the wider use of FinTech apps.