User-friendly online cybersecurity training
A simple and comprehensive approach that encourages awareness and supports the security frameworks often required by insurers.

Email protection
What to look for, what to avoid

Web protection
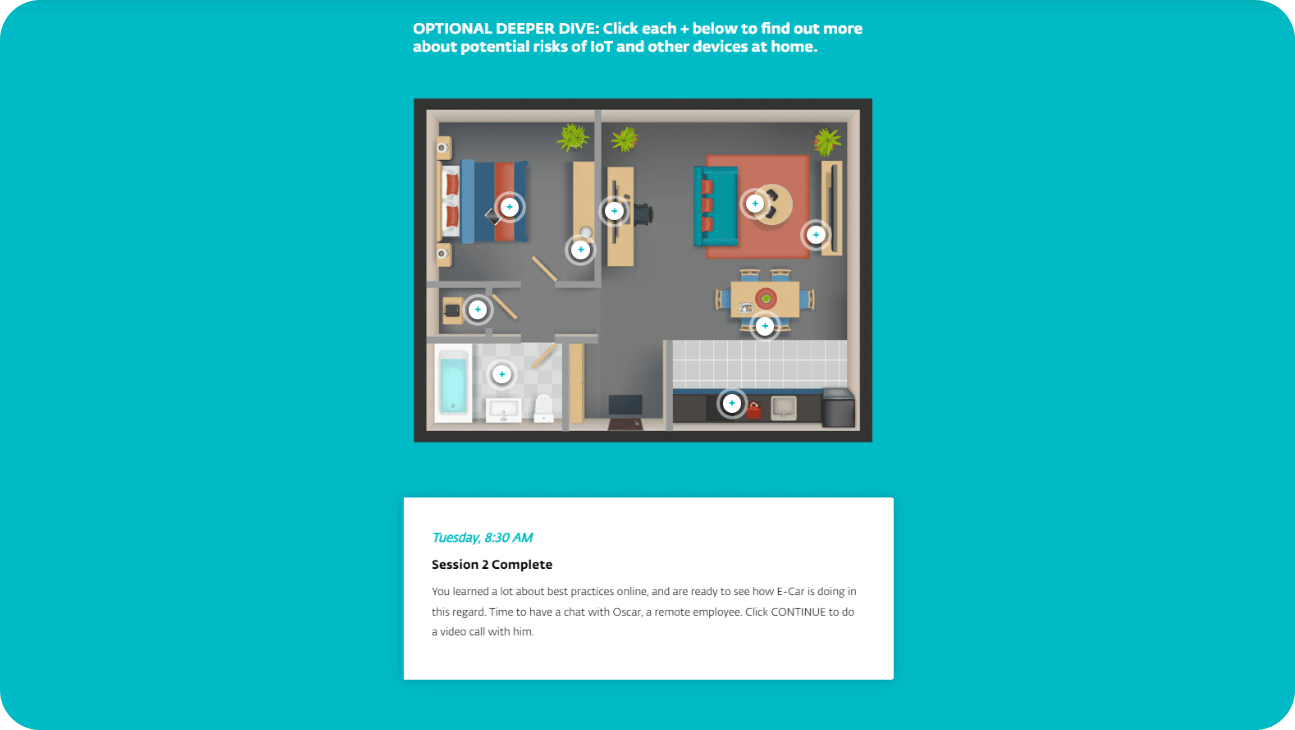
Wi-Fi, IoT and search engine security

Social engineering
How to recognize scams, what to do

Threats overview
Malware, phishing & insider threats

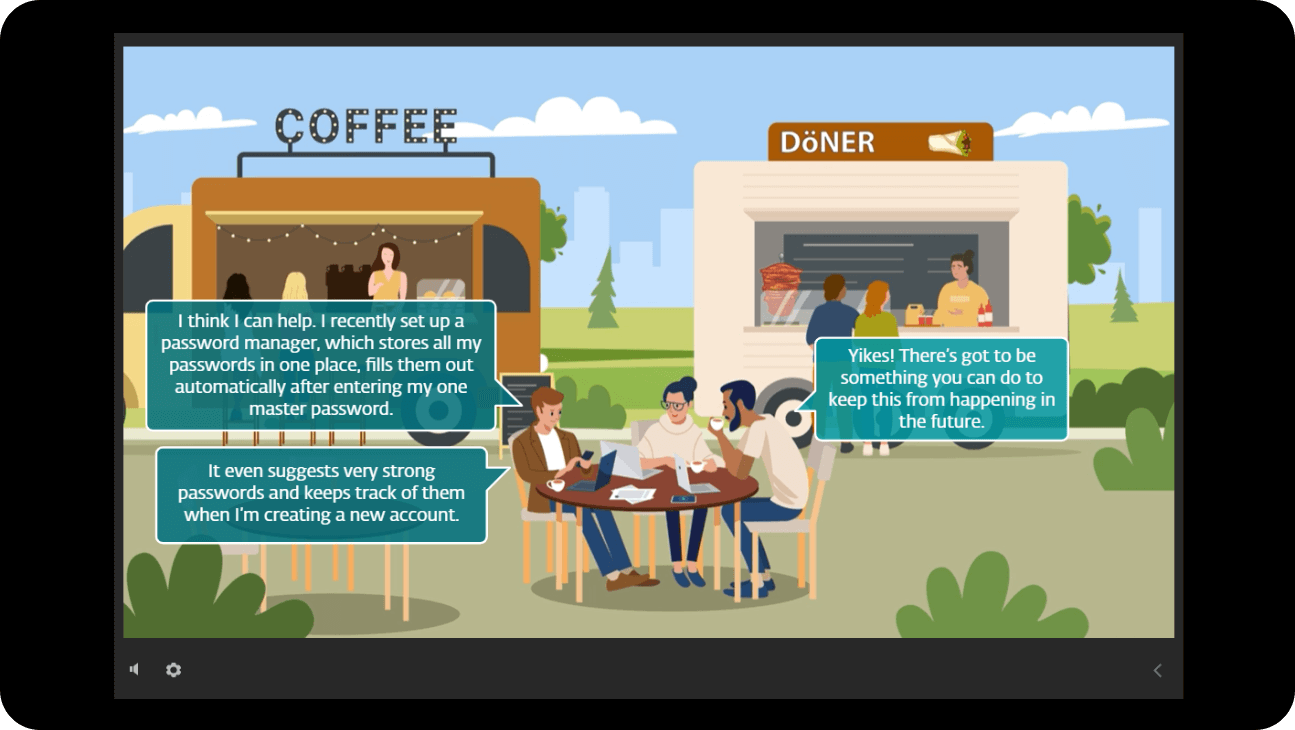
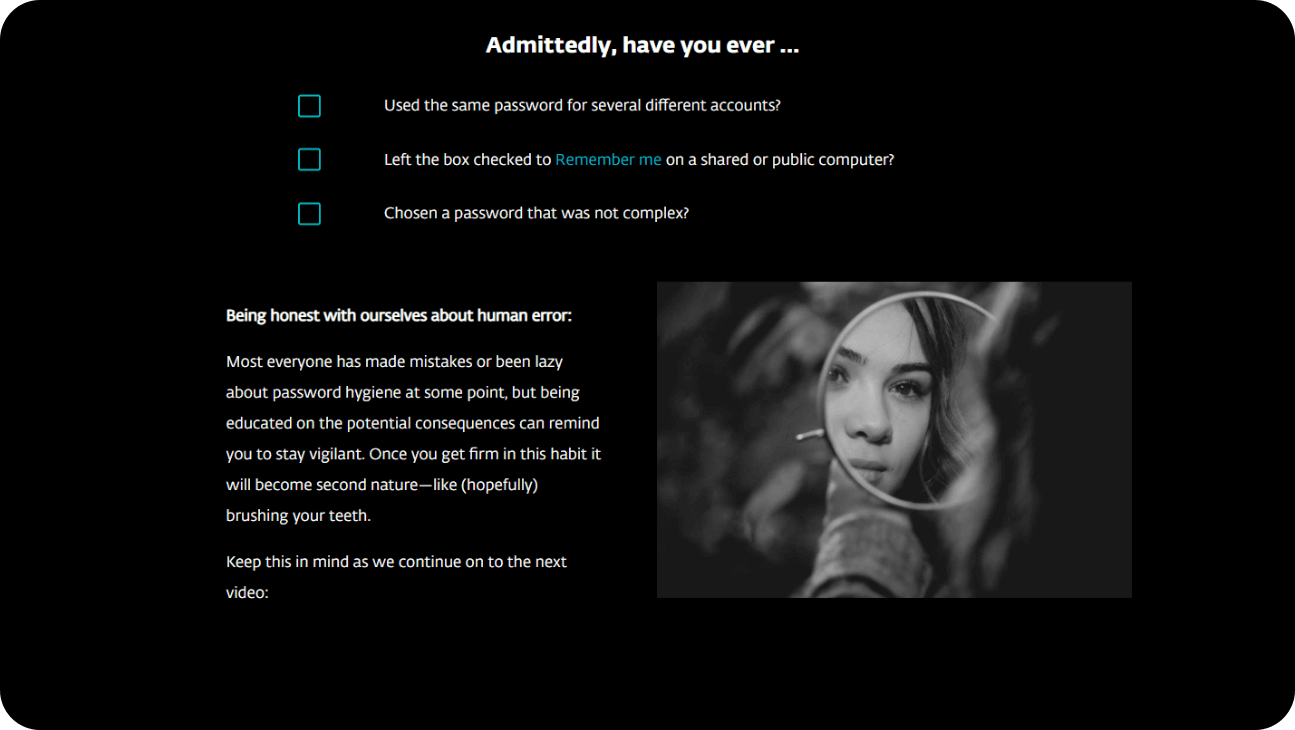
Password policies
Best practices like 2FA, and how to use them

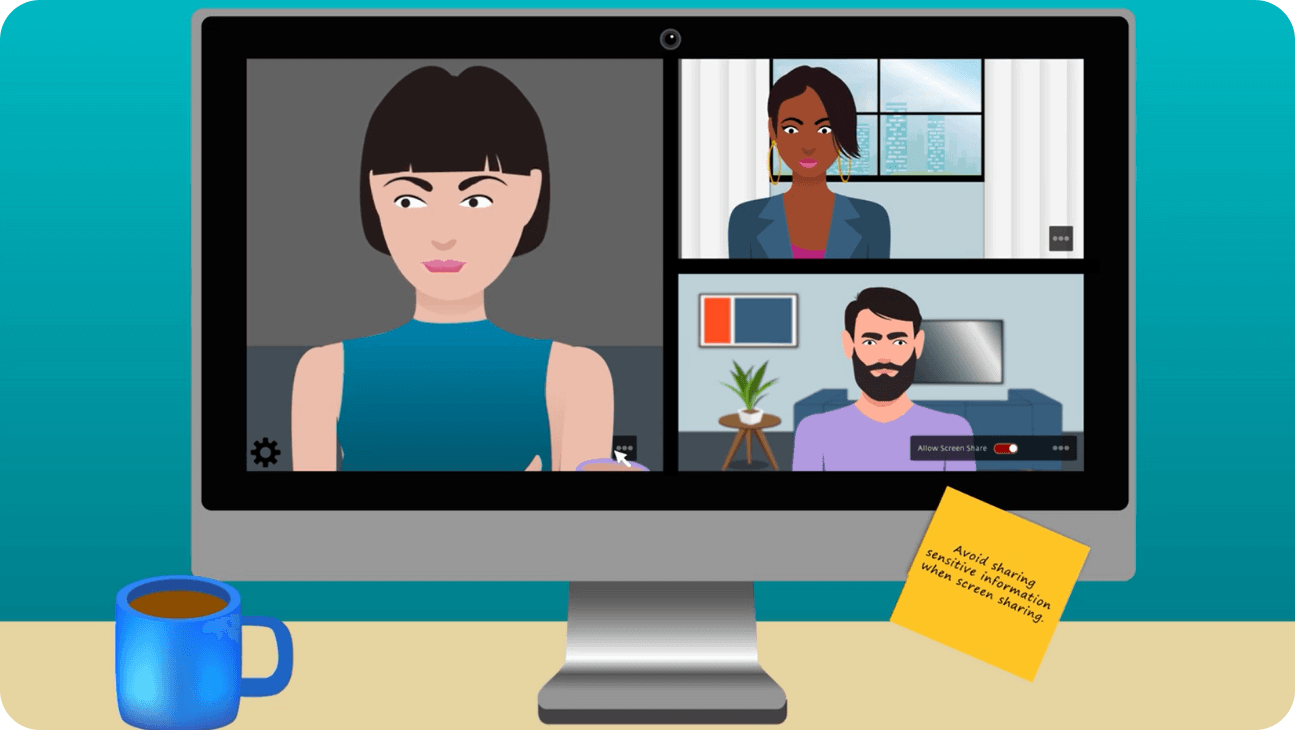
Remote workforce
Stay safe while working from home
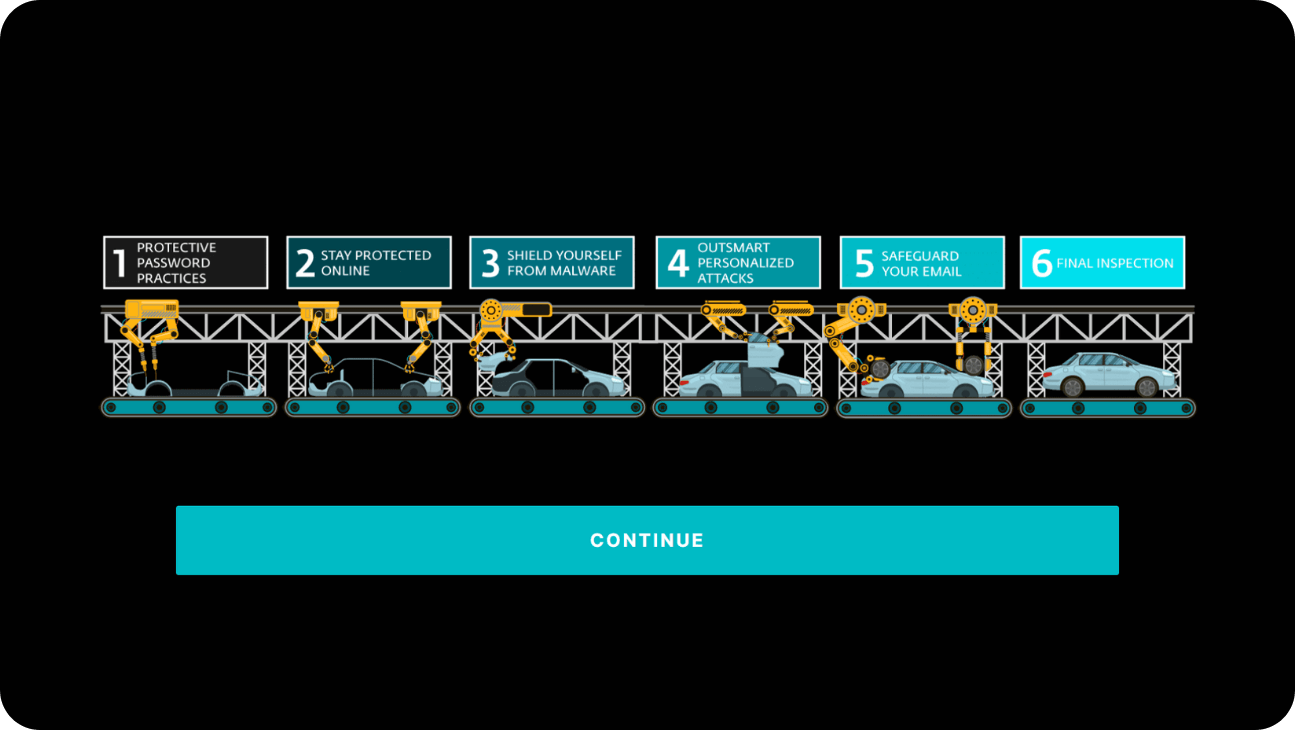
What do you get with ESET Cybersecurity Awareness Training?
- Learn techniques that will protect your organization, and your personal privacy
- Share easily with your employees and colleagues
- Choose from 19 cybersecurity topics in 5 main categories
- Enjoy interactive video content
- ESET Cybersecurity Awareness Training includes a final recap quiz
- Start training immediately after filling out the form
Digital Security Guide
Digital Security Guide is ESET's content platform for small and medium business owners and IT administrators to help stay up to date on new data security and cybersecurity regulations, technologies, or emerging threats.
Cybersecurity frameworks are structured guidelines, best practices, and standards designed to help organizations manage and improve their cybersecurity posture. While cybersecurity may appear complex,…
When an annual security training email hits their inbox, many employees tend to either ignore it or search for shortcuts to breeze through the final test. They just want to check it off their list.…
A comprehensive guide emphasizing a prevention-first, risk-based approach.
The transformative impact of AI on cybersecurity.