Why do customers appreciate our server security?
Multilayered defense
A single layer of defense is not enough for today's constantly evolving threat landscape. ESET protection for file servers detects malware pre-execution, during execution and post-execution.
Central management
ESET Server Security solutions can be managed from the ESET PROTECT management console, which is a cloud-based, unified threat management tool.
Cross-platform Support
Protect your file servers on multiple OSes and platforms including Windows Server, Microsoft 365, OneDrive and Linux.
Common use cases
Worried about
Fileless malware?
Fileless malware is a relatively new threat, and due to only existing in memory, it requires a different approach than traditional file-based malware.
Worried about
Ransomware?
Some businesses require extra insurance against ransomware attacks. They also want to ensure their network drives are safe from undesired encryption.
Worried about
Zero-day threats?
Zero-day threats are a major concern for businesses due to not knowing how to protect themselves against something that they have never seen before.
What makes our solutions a perfect fit for your needs?
Server security
Server security
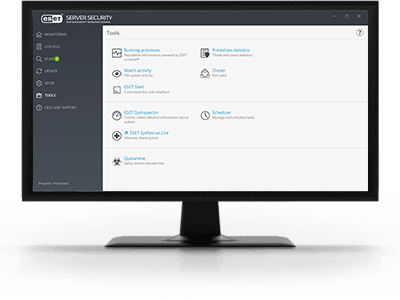
ESET Server Security
Provides advanced protection for your company’s data passing through all general servers, network file storage including OneDrive, and multi-purpose servers to ensure business continuity.
- Ransomware prevention
- Zero-day threats detection
- Data breaches prevention
- Botnet protection
Watch demos or start a free trial
Explore ESET Server Security features
Web Control
Web Control allows you to block inappropriate, harmful and productivity-reducing websites, ensuring consistent policies across all endpoints and servers. Included in ESET PROTECT Entry and above tiers, it enhances both productivity and security for your entire network.
Server host firewall
Keeps all communications on your Windows server under control by enabling the ESET Server Security firewall, specifically tailored for server environments. Feature available in ESET PROTECT Entry and higher.
Ransomware Shield
An additional layer protecting users from ransomware. Our technology monitors and evaluates all executed applications based on their behavior and reputation.
Vulnerability & Patch Management
Extends Vulnerability & Patch Management capabilities to servers. Fully manageable via the ESET PROTECT Platform, this functionality reduces the attack surface by actively tracking vulnerabilities in operating systems and common applications, enabling efficient patching.
Network Attack Protection
ESET Network Attack Protection improves detection of known vulnerabilities on the network level.
Protection for Linux servers
ESET provides installers for the most popular distributions of Unix-based systems, including the ‘Ready’ variations of RedHat and SuSE that comply with the File-System-Hierarchy standard.
System requirements
Supported operating systems
- Windows
- Linux
Note: Exact features and functionality may vary depending on the OS and version used.
Committed to the highest industry standards

Respected by industry analysts
Awarded in independent tests
Appreciated by customers worldwide
Purchase your file server security solution today
ESET's file server security is available in the following solutions
Modern multilayered endpoint protection featuring cutting-edge AI and easy-to-use management
All included modules:
- Console
- Modern Endpoint Protection
- Server Security
- Mobile Threat Defense
- Full Disk Encryption
- Advanced Threat Defense
- Cloud Workload Protection
- Cloud App Protection
- Mail Server Security
- Vulnerability & Patch Management
- Extended Detection & Response
- Multi-Factor Authentication
- MDR Service
- Premium Support
Best-in-class endpoint protection against ransomware & zero-day threats, backed by powerful data security
All included modules:
- Console
- Modern Endpoint Protection
- Server Security
- Mobile Threat Defense
- Full Disk Encryption
- Advanced Threat Defense
- Cloud Workload Protection
- Cloud App Protection
- Mail Server Security
- Vulnerability & Patch Management
- Extended Detection & Response
- Multi-Factor Authentication
- MDR Service
- Premium Support
Security for SharePoint Server
Advanced protection for SharePoint servers against malicious uploads and unwanted files
Includes: ESET Security for Microsoft SharePoint Server
- Protection against ransomware
- Data breaches prevention
- Zero-day threats detection
- File-less attacks prevention
Complete, multilayered protection for endpoints, cloud applications and email, the number one threat vector
All included modules:
- Console
- Modern Endpoint Protection
- Server Security
- Mobile Threat Defense
- Full Disk Encryption
- Advanced Threat Defense
- Cloud Workload Protection
- Cloud App Protection
- Mail Server Security
- Vulnerability & Patch Management
- Extended Detection & Response
- Multi-Factor Authentication
- MDR Service
- Premium Support
Extended detection and response that delivers enterprise-grade visibility, threat hunting and response options
All included modules:
- Console
- Modern Endpoint Protection
- Server Security
- Mobile Threat Defense
- Full Disk Encryption
- Advanced Threat Defense
- Cloud Workload Protection
- Cloud App Protection
- Mail Server Security
- Vulnerability & Patch Management
- Extended Detection & Response
- Multi-Factor Authentication
- MDR Ultimate Service
- Premium Support Ultimate
All-in-one prevention, detection & response combining enterprise-grade XDR with complete multilayered protection
All included modules:
- Console
- Modern Endpoint Protection
- Server Security
- Mobile Threat Defense
- Full Disk Encryption
- Advanced Threat Defense
- Cloud App Protection
- Cloud Workload Protection
- Mail Server Security
- Vulnerability & Patch Management
- Extended Detection & Response
- Multi-Factor Authentication
- MDR Ultimate Service
- Premium Support Ultimate
Superior protection with continuous threat hunting and monitoring via 24/7 managed detection & response service
All included modules:
- Console
- Modern Endpoint Protection
- Server Security
- Mobile Threat Defense
- Full Disk Encryption
- Advanced Threat Defense
- Cloud Workload Protection
- Cloud App Protection
- Mail Server Security
- Vulnerability & Patch Management
- Extended Detection & Response
- Multi-Factor Authentication
- MDR Service
- Premium Support
Continuous protection for your evolving IT environment, with premium cyber risk management and 24/7 ESET expertise on call
All included modules:
- Console
- Modern Endpoint Protection
- Server Security
- Mobile Threat Defense
- Full Disk Encryption
- Advanced Threat Defense
- Cloud Workload Protection
- Cloud App Protection
- Mail Server Security
- Vulnerability & Patch Management
- Extended Detection & Response
- Multi-Factor Authentication
- MDR Ultimate Service
- Premium Support Ultimate
Cybersecurity Awareness Training
Prevention-first education to ensure employees are the foundation of an organization’s digital security
Includes: ESET Cybersecurity Awareness Training
- Effective training methods
- Simulated phishing campaigns
- Smart management and detailed reporting
- Deep integration with various systems
- Compliance with regulations