1bn+
users worldwide
500k+
business customers
ESET Endpoint Encryption
A simple to use encryption application providing full remote control of endpoint encryption keys and security policy for files on hard drives, portable devices and emails. Ensures:

Zero data breaches

Compliance with requirements

Seamless encryption
Manage devices anywhere
ESET Endpoint Encryption can manage devices anywhere in the world without requiring VPNs nor any firewall exceptions. Management is handled by utilizing HTTPS internet connectivity making it extremely simple for businesses of any size to install and setup.
Zero impact on productivity
The implementation of encryption is completely transparent for the users and requires no action on their part. There is no extra overhead for IT departments and no need for user training.
Fast, seamless deployment
Server installation of ESET Endpoint Encryption usually takes less than 10 minutes, with complete setup of the solution under one hour.
Use cases
PROBLEM
Businesses are in the news every single day notifying their customers that a data breach has occurred.
SOLUTION
- Protect sensitive data with ESET Endpoint Encryption by means of full-disk encryption (FDE).
- Protect vulnerable communications such as Remote Desktop by adding multi-factor authentication.
- Require multi-factor authentication in order to log in to devices that contain sensitive data.

protected by ESET since 2017
more than 9,000 endpoints
protected by ESET since 2016
more than 32,000 endpoints
The ESET difference
No server required
ESET Endpoint Encryption requires no server for deployment and can seamlessly support remote users.
No special hardware required
TPM chips are optional but not required for using Full Disk Encryption.
Fully validated
ESET Endpoint Encryption is FIPS 140-2 validated with 256 bit AES encryption.
Multi-platform
Encryption supported across Windows 10, 8, 8.1, 7, Vista, XP, and Server 2003 – Server 2016 and iOS.
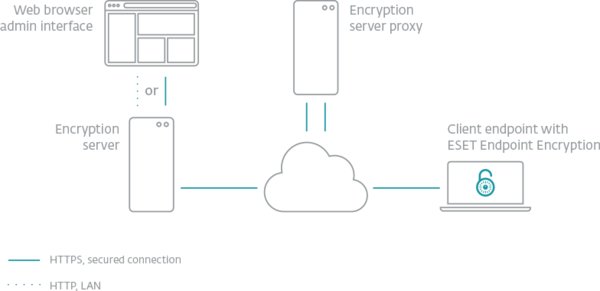
The management of endpoints via server proxy requires no incoming connections, making it extremely safe and easy to set up. No firewall exclusions or open ports are required. The encryption server can run on any Windows PC or server.
Explore our customized solutions
Please leave us your contact details so we can design a personalized offer to fit your requirements.
No commitment.
Supported features
- Full disk encryption (FDE)
- File/folder encryption
- USB encryption
- E-mail encryption
Looking for complete security for your network?
Related enterprise-grade solutions
ESET Identity & Data Protection
- Two-factor Authentication
- Endpoint Encryption
Related SMB solutions
- ESET Secure Authentication
Powerful Two-factor authentication makes access to networks and data safe and problem-free. - Data Loss Prevention
Safetica protects you from expensive data leaks and unnecessary personnel costs. - ESET Endpoint Security
Award-winning multilayered technology combining machine learning, big data and human expertise.