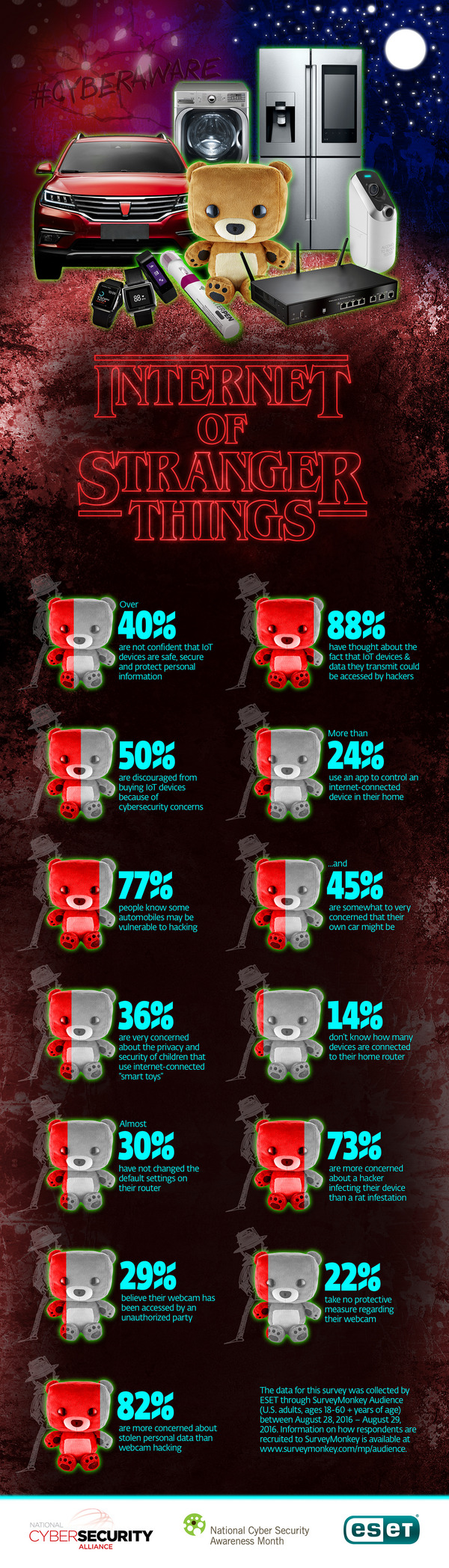
A survey by ESET and the National Cyber Security Alliance reveals nearly one quarter of consumers have an internet-connected device such as a thermostat or appliance in their home, and use an app to control it.
Yet, more than 40% are “not confident at all” that IoT devices are safe, secure, and able to protect personal information.
So take these 5 steps now and in the future to increase security on your own internet of Things.
Then, check out the other survey results on the “Internet of Stranger Things” infographic below, as well as a summary of the survey data and key takeaways.)
1. Change both the default login password on your home router and your Wifi password every 3 months:
As this survey demonstrated, not many consumers change the default password that comes standard on their home routers. This means that a hacker can easily gain access to their router by guessing the password that comes default on common routers. Changing this password to something new every three months ensures that even if you share the password or it’s accessed by some other means, you keep your router more secure.
2. Ensure software for all devices and connected systems is up to date (including router firmware):
Manufacturers and software providers frequently issue product updates throughout the year. While some of these changes include new features that are available, or adjustments to an interface, they are often security related as well. Keeping software up to date on all connected devices ensures you have the latest protection the manufacturer/developer offers. Hint: Check your router’s model number and visit the manufacturer’s site to see whether there is a newer version available to download.
3. Confirm whether your home security software features router protection:
Home security software is one important layer in protecting your personal data and information. Some home security software now features router protection, which allows you to easily view and manage the devices that access your network. If a device that you don’t recognize is accessing your network, you can elect to block it. You can also add a master list of authorized devices and then set it so no other device will be able to join the network.
4. Ensure you understand what data is being collected and stored by your connected devices:
As you know, the data we generate and information we transact online with is extremely valuable if it ends up in the wrong hands. Because of this, it’s critical that you are aware of what data your connected devices collects, how it is stored and how it is shared. While it would cause a red flag if a connected fridge asked to access something such as your home security system, you might not think twice about letting your connected heating system store your weekly data log. However, a criminal that gains access to that log because it’s not securely stored can tell when the home is not heated or the heat is turned down, signifying your home is vacant.
5. Limit device/app privileges:
As with apps accessed on a mobile device, you should look to limit the access and privileges your connected devices have daily. Should your toaster be able to access your contact list? Will the fridge ever need to communicate with your front door lock? Ensure devices and apps don’t have free rein to communicate with entities they don’t need to so that even if one device is breached, it does not mean all your connected devices can be accessed.