The world’s most formidable cybersecurity based on superior research
that’s easy to use.
A unique balance of
prevention, detection and response.
ESET Inspect
XDR-enabling component
Investigate data, events and alarms generated by ESET’s XDR-enabling solution, ESET Inspect.
Threat Hunting
Whenever a malicious executable, process or device is located, admins have access to contextual actions that they can implement immediately to remedy the issue.
Incident Response
View and block modules based on over 30 different indicators of compromise, including hash, registry modifications, file modifications and network connections.
IOC Search
See root cause analysis, and full process tree, for any potentially malicious chain of events, allowing you to make informed decisions.
Forensics
The “maliciousness” of an activity depends on the context. With proper device groupings, admins can identify if specific activities should be performed by users on specific machines. Further context is provided thanks to ESET’s integration of the MITRE ATT&CK framework.
Enriched Context
ESET Inspect includes a rules-based detection engine for indicators of attack. Rules that are designed to identify suspicious malicious behavior trigger detections according to defined severities.
Detection Rules
Security Operations
Improve collaboration, reduce risk.
Actively track & fix vulnerabilities in operating systems and applications across all endpoints.
Vulnerability & Patch management
Guards against malicious system attacks on endpoints by controlling file, email and internet communication and applying appropriate remediation.
Endpoint Detection
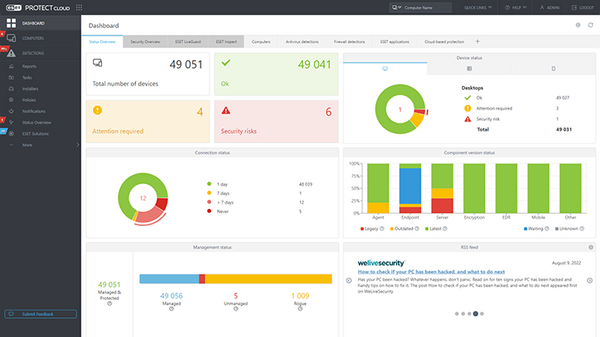
ESET PROTECT is a robust platform interface that allows users to automate a variety of actions, including resolution of sophisticated incidents.
Automated Response
Proactive cloud-based defense against zero-day and never-before-seen threat types.
ESET LiveGuard Detections
Advanced protection for Microsoft 365 email, collaboration and storage applications.
Cloud Application Protection
Fully validated encryption ensures your organization’s data is protected and helps you comply with laws and regulations.
Encryption
Seamless multi-factor authentication ensures access to your organization’s data is protected in compliance with laws and regulations.
Multi-Factor Authentication
Security Management
Protect your network, secure your data.
Allows admins to block or restrict read- or write-access to specified devices such as USB drives, bluetooth accessories or external hard drives.
Device Control
A ready-to-use solution, integrated within our platform interface, that covers Android and Apple devices.
Mobile Device Management
Regulate access to websites with inappropriate or harmful content, or pages that may have a negative impact on productivity.
Web Control
Control all network traffic to and from the system by allowing or denying individual network connections based on specified filtering rules.
Firewall Management
Retrieve hardware and software inventory details from connected devices, such as details about a device's RAM, storage, processor, etc.
HW & SW Inventory
Detect and control unknown or managed devices that are present on your network, and thereby mitigate potential security threats to your organization from unauthorized connections.
Rogue Device Management
IT Operations
Improve work flows, reduce costs.
- UEFI Scanner Checks and enforces the security of the pre-boot environment to detect and report malicious components in the firmware.
- LiveGrid® Our cloud reputation system, which utilizes data from ESET users worldwide and enables us to react immediately to the latest threats.
- Advanced Machine Learning We've long pioneered machine learning to detect and block threats, resulting in the best detection rates and the lowest possible number of false positives.
- LiveGuard Sandbox Executes suspicious samples in an isolated cloud test environment and evaluates their behavior using threat intelligence feeds, static and dynamic analysis, and reputation data.
- DNA Detections Based on deep analysis, we construct ESET DNA Detections which are used to assess potentially suspect code.
- Network Attack Protection Analyzes the content of network traffic and protects from network attacks. Any traffic which is considered harmful is blocked.
- Script Scanner & AMSI Script-based attack protection against JavaScript in web browsers and scripts in Powershell.
- Secure Browser Provides an additional layer of protection designed to protect sensitive data while browsing online (for example, financial data during online transactions).
ESET LiveSense
Multilayered technologies
- Monitors and evaluates all executed applications based on their behavior and reputation to detect and block processes that resemble the behavior of ransomware. Ransomware Shield
- Monitors typically exploitable applications (browsers, document readers, email clients, Flash, Java, and more) and focuses on exploitation techniques. Exploit Blocker
- Works in combination with Exploit Blocker to strengthen protection against malware that seeks to evade detection via the use of obfuscation and/or encryption. Advanced Memory Scanner
- Spots malware that has infected other software and is actively running. Monitors all the processes on a system at a low level and observes their behavior. Deep Behavioral Inspection
- Detects and blocks automated attacks that try to use password-guessing techniques to gain access to your network. Brute-Force Attack Protection
- Discovers malware through analyzing its network communication protocols. Defeats malware which tries to avoid detection and connect devices to botnet networks. Botnet Protection
- When inspecting a file or URL, before any scanning takes place, our products check the local cache for known malicious or whitelisted benign objects. Reputation and Cache
- ESET Threat Intelligence Threat Intelligence from ESET's world-renowned experts delivers in-depth feeds and APT reports. Get a unique perspective on the threat landscape and improve your cybersecurity posture.
- ESET Managed Detection and Response ESET’s MDR combines ESET technology and digital security expertise to effectively and proactively detect and respond to any threat.
- ESET Premium Support provides smooth deployment of ESET business products, ensures they operate flawlessly, and provides quick incident resolution. ESET Premium Support
- The ESET Deployment and Upgrade service assures correct installation and set-up of ESET products and secures seamless upgrades between major versions of ESET products. ESET Deployment and Upgrade
- ESET HealthCheck service examines your ESET business products policies, settings and configurations, identifies areas for improvement and suggests action points. ESET HealthCheck