Throughout 2019, the Emotet trojan gained increasing notoriety for spreading malicious emails, while also being blamed for helping to deliver ransomware like Ryuk.
In more recent campaigns, Emotet operators crafted very ingenuous phishing emails with an invitation to contribute to the menu of an upcoming Christmas party. In another invitation, Emotet jumped on people’s aspiration to support Greta Thunberg, Time Person of the Year 2019, by calling on readers to join in a demonstration against inaction on climate change.
Interestingly, Emotet also appears to have some steam to blow off with ESET. The Emotet writers, on occasion, drop comments into their code seemingly either venting their frustration at ESET or perhaps even a kind of temporary elation:
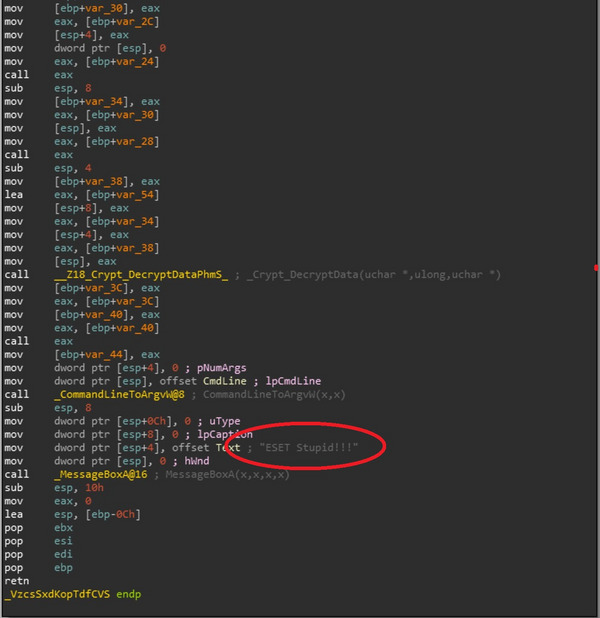
(image above) ESET’s detection technologies have been consistently blocking Emotet and all its variants, which could certainly elicit this kind of rude remark.
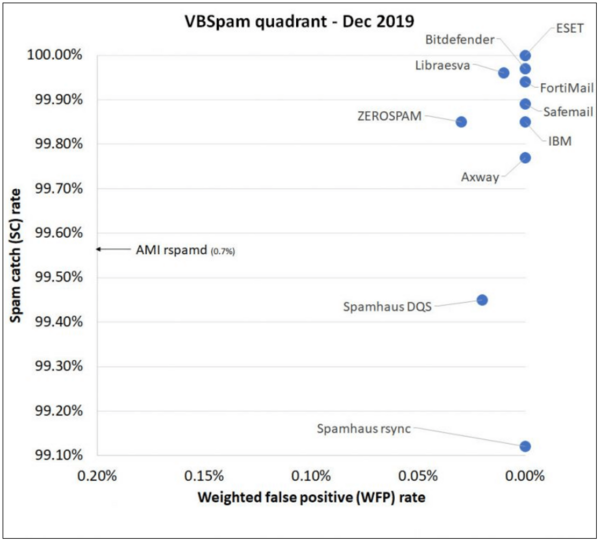
For businesses, the crafty social engineering tactics employed by Emotet could cause concern about the cyberawareness of your employees and conversely the robustness of your security systems. According to recent research from Virus Bulletin, Emotet can still bypass a number of email security products on the market. “Emails containing Emotet-infected malicious attachments continued to be the most difficult to block,” said the report from Virus Bulletin.
(image below) Fortunately for business users of ESET Mail Security for Microsoft Exchange Server, VBSpam testing shows that ESET has the highest spam, phishing and malware detection rates with the lowest false positive rate among competitors:
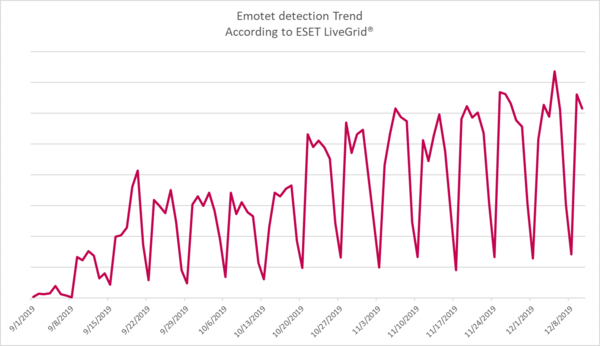
(image below) These are especially important metrics and necessary for businesses to assess their protection in the face of ongoing campaigns by Emotet. ESET LiveGrid® detections of Emotet from September to December 2019 showed a rising trend:
Layered protection in action
This telemetry data is a good indicator of the level of protection that devices protected by ESET enjoy against Emotet by detecting and blocking it before any possible compromise.
It should be kept in mind that simply receiving an email and downloading an attached Word document – one of Emotet’s methods to gain access to your device – does not necessarily mean your computer is compromised. The default security setting when opening email attachments is to use a “Protected View” with macros disabled, rendering the attachment innocuous.
But, to gain a better understanding of how ESET detects and blocks Emotet, let’s take a deeper dive.
The detection of a malicious attachment can be done even when it is unopened (depending on the level of its obfuscation) through a variety of detection techniques, including DNA Detections or by querying the ESET LiveGrid® Reputation System for its reputation.
ESET LiveGrid® Feedback System collects suspicious samples submitted by millions of ESET-protected endpoints from around the world for machine learning analysis in the cloud. The collected knowledge from any detections is then shared via the ESET LiveGrid® Reputation System to keep users protected from threats found in other parts of the world.
In the case of Emotet, if a user should open a malicious attachment and mistakenly enable macros, a set of PowerShell commands runs that attempt to contact compromised domains in order to download another malicious component. Of course, this is doomed to fail if the domain has already been marked as malicious by ESET, since the web access protection would stop the download attempt immediately.
Even if the domain was not blacklisted, the PowerShell commands themselves can also be identified as malicious by a security layer called ESET Host-based intrusion prevention system (HIPS).
(image below) HIPS is a detection layer built into many ESET products that monitors system activity and uses a pre-defined set of rules to recognize suspicious behavior. When suspicious activity – such as Emotet trying to start PowerShell commands from a Word document – is identified, HIPS can prevent it from running.
It can also trigger other layers, such as Advanced Memory Scanner (AMS) that monitor and detect malicious programs in memory, employing various techniques – such as the in-product sandbox and further DNA Detections.
This allows ESET products to identify the Emotet agent downloaded with the PowerShell commands as well as detect or block the payloads usually downloaded by this malware family.
Businesses have the advantage of being able to bypass entirely the need for employees’ machines ever to deal with Emotet-laden emails by beefing up network defenses with ESET Dynamic Threat Defense, which can test for malicious files in a cloud sandbox within minutes and thus prevent the initial entry of malware into a network.
These are only some of the security layers that ESET’s advanced solutions include and that are making the work of cybercriminals behind campaigns like Emotet more difficult. Have no doubt that Emotet made a return in 2019; businesses should look to raise their security maturity in the face of a rising trend into 2020.
You can obtain the latest Emotet malware IoCs, including compromised domains and C&C server addresses, by subscribing to ESET Threat Intelligence (ETI) services, which collects data from over 110 million sensors worldwide.