Protection des points terminaux
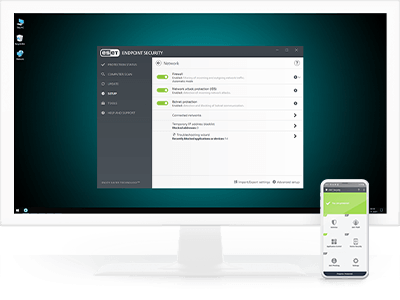
ESET Endpoint Security
Exploite une approche multicouche qui utilise plusieurs technologies en équilibre dynamique pour équilibrer constamment les performances, la détection et les faux positifs, ce qui permet aux organisations:
- Protection contre les logiciels de rançon
- Bloquer les attaques ciblées
- Prévenir les violations de données
- Arrêter les attaques sans fichier
- Détecter les menaces persistantes avancées
- Protection mobile et MDM
Explorer les fonctionnalités
Géré à partir d'une console unifiée
Tous les terminaux ESET, y compris les terminaux et les mobiles, peuvent être gérés à partir de notre console de gestion unifiée basée sur le cloud, ESET PROTECT.
Stop aux attaques sans fichier
Les plates-formes de protection des terminaux ESET ont des mesures d'atténuation en place pour détecter les applications malformées ou détournées afin de se protéger contre les attaques sans fichier. Des scanners dédiés ont également été créés pour vérifier constamment la mémoire à la recherche de tout élément suspect.
Bloquer les attaques ciblées
Les solutions de protection des points de terminaison d'ESET utilisent les informations de renseignement sur les menaces basées sur leur présence mondiale pour donner la priorité et bloquer efficacement les menaces les plus récentes avant leur livraison partout ailleurs dans le monde. En outre, nos solutions disposent d'une mise à jour basée sur le cloud pour répondre rapidement en cas de détection manquée sans avoir à attendre une mise à jour régulière.
Sauvegarder le navigateur web
Conçu pour protéger les actifs d'une organisation grâce à une couche de protection spéciale qui se concentre sur le navigateur, principal outil utilisé pour accéder aux données critiques à l'intérieur du périmètre de l'intranet et dans le nuage. Secure Browser offre une protection renforcée de la mémoire pour le processus de navigation, associée à une protection du clavier, et permet aux administrateurs d'ajouter des URL à protéger.
Protection contre les attaques de réseau
ESET Network Attack Protection améliore la détection des vulnérabilités connues au niveau du réseau.
Protection contre les botnets
ESET Botnet Protection détecte les communications malveillantes utilisées par les botnets, et en même temps, identifie les processus en infraction. Toute communication malveillante détectée est bloquée et signalée à l'utilisateur.
Apprentissage automatique
Tous les produits ESET Endpoint utilisent actuellement l'apprentissage automatique en conjonction avec toutes nos autres couches de défense et l'ont fait depuis 1997. Plus précisément, l'apprentissage automatique est utilisé sous la forme de sorties consolidées et de réseaux neuronaux. Pour une inspection approfondie du réseau, les administrateurs peuvent activer le mode spécial d'apprentissage automatique agressif qui fonctionne même sans connexion Internet.
Bac à sable intégré au produit
La Sandbox d'ESET permet d'identifier le comportement réel caché sous la surface des logiciels malveillants.
Bouclier contre les ransomwares
Une couche supplémentaire protégeant les utilisateurs contre les ransomwares. Notre technologie surveille et évalue toutes les applications exécutées en fonction de leur comportement et de leur réputation. Elle est conçue pour détecter et bloquer les processus qui ressemblent au comportement des ransomwares.
Ransomware Remediation
Elle permet un retour en arrière complet grâce à une restauration transparente et automatisée des fichiers à partir de sauvegardes sécurisées, minimisant ainsi l'impact sur l'entreprise en cas d'attaque par ransomware. Cette fonction exclusive complète la protection Ransomware Shield en utilisant des technologies de détection et de remédiation avancées qui surpassent le Volume Shadow Copy Service utilisé par d'autres solutions. Renforcez votre cyber-résilience et ne payez plus jamais de rançon.
Note : Inclus dans ESET PROTECT Advanced et les niveaux d'abonnement supérieurs.
Détection comportementale - HIPS
Le système de prévention des intrusions basé sur l'hôte (HIPS) d'ESET surveille l'activité du système et utilise un ensemble prédéfini de règles pour reconnaître et arrêter les comportements suspects du système.
Scanner UEFI
ESET est le premier fournisseur de sécurité des points d'extrémité à ajouter une couche dédiée dans sa solution qui protège l'interface micrologicielle extensible unifiée (UEFI). ESET UEFI Scanner vérifie et renforce la sécurité de l'environnement pré-boot et est conçu pour surveiller l'intégrité du firmware. Si une modification est détectée, il en informe l'utilisateur.
Scanner de mémoire avancé
ESET Advanced Memory Scanner surveille le comportement d'un processus malveillant et l'analyse une fois qu'il s'est débloqué en mémoire. Les logiciels malveillants sans fichier fonctionnent sans avoir besoin de composants persistants dans le système de file qui peuvent être détectés de manière conventionnelle. Seul le scan de la mémoire permet de découvrir et de stopper avec succès de telles attaques malveillantes.
Exploit Blocker
ESET Exploit Blocker surveille les applications typiquement exploitables (navigateurs, lecteurs de documents, clients de messagerie, Flash, Java et plus), et au lieu de viser des identifiants CVE particuliers, il se concentre sur les techniques d'exploitation. Lorsqu'il est déclenché, la menace est immédiatement bloquée sur la machine.
System requirements
Systèmes d’exploitation pris en charge
Pour les ordinateurs
- Windows
- macOS
- Linux
Pour les téléphones intelligents et les tablettes
- Android
- iOS et iPadOS (fonctionnalité de gestion des appareils mobiles uniquement)
Remarque : Les caractéristiques et les fonctionnalités exactes peuvent varier selon le système d’exploitation et la version utilisée.