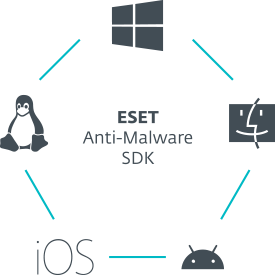
ESET Anti-Malware SDK
Available for both Windows and Linux platforms, ESET Anti-Malware SDK provides multilayered, cross-platform protection for a wide range of applications and integration scenarios. Provides:

Multiple subscription
options

Cross-platform
protection

Scalability

Comprehensive
SDK Kit
Cross-platform threat detection
While the SDK supports Windows and Linux, the scanning engine also blocks mobile malware (Android, iOS) and threats targeting macOS, providing for a fully fledged cross-platform protection.
Add anti-malware capabilities
Whether intended for your organisations’ internal use or for your customers, the SDK easily integrates ESET's scanning engine to fend off all types of threats, including ransomware and zero-day malware.
Complete control
You have full control over the implementation process and which functionality you decide to use. The solution offers a wide range of options, supported with extensive documentation and ESET engineers ready to assist you in case you need help.
Use cases
PROBLEM
How to add value to products and services your organisation provides?
Your organisation is competing in a tough market and needs to enhance its products, services and solutions.
SOLUTION
- Build products with excellent protection within.
Offer products with excellent-quality in-built protection. To gain a head start on your rivals, enhance your products, services and solutions with ESET anti-malware. Depending on the type of product or service your organisation provides, choose the ESET Anti-Malware SDK functionality that suits best and offers most value to your customers.

protected by ESET since 2017
more than 9,000 endpoints
protected by ESET since 2016
more than 4,000 mailboxes
protected by ESET since 2016
more than 14,000 endpoints
ISP security partner since 2008
2 million customer base
The ESET difference
DNA detections
Detection types range from very specific hashes to ESET DNA Detections, which are complex definitions of malicious behaviour and malware characteristics.
While the malicious code can be easily modified or obfuscated by attackers, the behaviour of objects cannot be changed so easily and ESET DNA Detections are designed to take advantage of this principle.
In-product sandbox
Today’s malware is often heavily obfuscated and tries to evade detection as much as possible. To see through this and identify the real behaviour hidden underneath the surface, we use in-product sandboxing.
With the help of this technology, ESET solutions emulate different components of computer hardware and software to execute a suspicious sample in an isolated virtualised environment.
Scans files and blocks of data
Analyses hundreds of different file formats (executables, installers, scripts, archives, documents and bytecodes, as well as blocks of data) in order to accurately detect embedded malicious components.
URL and IP address scanning
ESET Anti-Malware SDK also provides URL and IP address scanning to identify and block phishing sites and addresses containing dangerous payload.
Explore our customised solutions
Please leave us your contact details so we can design a personalised offer to fit your requirements.
No commitment.
Stay on top of cybersecurity news
Brought to you by awarded and recognised security researchers from ESET's 13 global R&D centers.