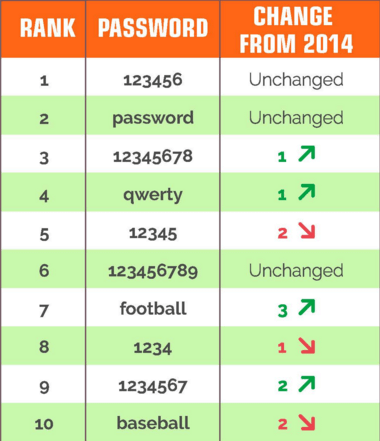
SplashData compiled their annual list of passwords made public during 2015 and ranked them in order of popularity. The list is not for the faint of heart, it makes some pretty scary reading.
Reader discretion is advised: the quality of the following passwords is harrowing. The following list shows the most ‘popular’ passwords of 2015, in order from most common to least.
The list was put together by SplashData, read their blog on the subject here.
- 123456
- password
- 12345678
- qwerty
- 12345
- 123456789
- football
- 1234
- 1234567
- baseball
- welcome
- 1234567890
- abc123
- 111111
- 1qaz2wsx
- dragon
- master
- monkey
- letmein
- login
- princess
- qwertyuiop
- solo
- password
- starwars
Hopefully none of your passwords appear on this list. If one, or more, does then change it ASAP! Mark James, ESET IT security specialist, explains why using a password as poor as these is a critical security flaw.
Why are these passwords so risky?
“Passwords will always be the single biggest failure point of any network or login,” Mark explains.
“It makes no difference how good your internal procedures are or how tight your rules and policies are configured if you’re using weak or easy passwords you are already on the easy target list.
“We often hear about data breaches and ask the usual question: was the data encrypted? But it makes no difference if the user is already authenticated due to you using and possibly losing inadequate login credentials.
“Simple password cracking procedures will take data that’s been hacked and leaked, match it against a known word and bingo they now have your password.
“Take those details and try every known online financial login and it’s quite possible you’re going to get a match.
“The bad guys have access to the same lists we do and when passwords appear in these lists they will be used for brute force matching immediately.
“Time is important when you’re trying to guess someone’s password, so they want to get it done and move on to the next one as quickly as possible.
“Bear in mind if you’re using any of these passwords it won’t take a hacker minutes to guess your password, not even seconds, it will take them less time to find your password than it did for you to enter it.”
Do you use a password manager or algorithm to create your passwords?
Join the ESET UK LinkedIn Group and stay up to date with the blog. If you’re interested in seeing where ESET has been featured in the news then check out our ‘In the news’ section.