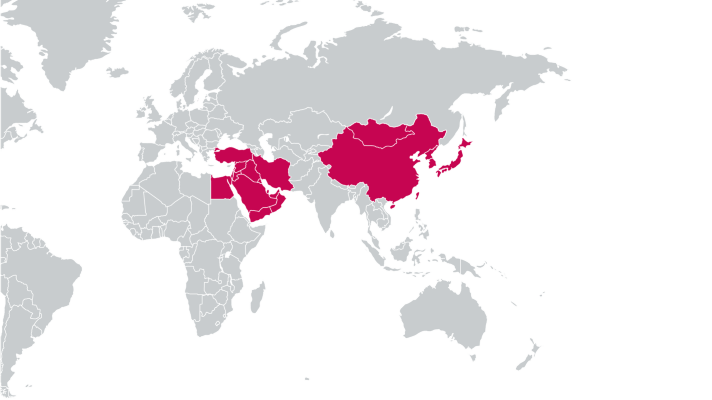
BRATISLAVA, MONTREAL – Since mid-2020, ESET Research has been analysing multiple campaigns, later attributed to the Gelsemium cyberespionage group, and has tracked down the earliest version of their main malware, Gelsevirine, to 2014. During the investigation, ESET researchers found a new version of Gelsevirine, a backdoor that is both complex and modular. Victims of its campaigns are located in East Asia as well as the Middle East and include governments, religious organisations, electronics manufacturers and universities. At present, the group has managed to remain mostly under the radar. This research was exclusively previewed at the annual ESET World conference this week.
Gelsemium is very targeted – with only a few victims, according to ESET telemetry – and considering its capabilities, this points to the conclusion that the group is involved in cyberespionage. The group has a vast number of adaptable components. “Gelsemium’s whole chain might appear simple at first sight, but the exhaustive number of configurations, implanted at each stage, can modify on-the-fly settings for the final payload, making it harder to understand,” explains ESET researcher Thomas Dupuy, co-author of the Gelsemium research analysis.
Gelsemium uses three components and a plug-in system to give the operators a range of possibilities to gather information: the dropper Gelsemine, the loader Gelsenicine, and the main plugin Gelsevirine.
ESET researchers believe that Gelsemium is behind the supply-chain attack against BigNox that was previously reported as Operation NightScout. This was a supply-chain attack, reported by ESET, that compromised the update mechanism of NoxPlayer, an Android emulator for PCs and Macs, and part of BigNox’s product range, with over 150 million users worldwide. The investigation uncovered some overlap between this supply-chain attack and the Gelsemium group. Victims originally compromised by that supply-chain attack were later being compromised by Gelsemine. Among the different variants examined, “variant two” from the article shows similarities with Gelsemium malware.
For more technical details about Gelsemium, read the blogpost “Gelsemium: when threat actors go gardening” on WeLiveSecurity. Make sure to follow ESET Research on Twitter for the latest news from ESET Research.
The geographical distribution of Gelsemium’s targets
About ESET
For more than 30 years, ESET® has been developing industry-leading IT security software and services to protect businesses, critical infrastructure and consumers worldwide from increasingly sophisticated digital threats. From endpoint and mobile security to endpoint detection and response, as well as encryption and multi-factor authentication, ESET’s high-performing, easy-to-use solutions unobtrusively protect and monitor 24/7, updating defences in real time to keep users safe and businesses running without interruption. Evolving threats require an evolving IT security company that enables the safe use of technology. This is backed by ESET’s R&D centres worldwide, working in support of our shared future. For more information, visit our website or follow us on LinkedIn, Facebook, and Twitter.