What is Spam?
Annoying emails, IMs, texts, voicemails and other digitally distributed messages that you’ve received but never would have asked for? Those can all be described by a single word – spam.
Annoying emails, IMs, texts, voicemails and other digitally distributed messages that you’ve received but never would have asked for? Those can all be described by a single word – spam.
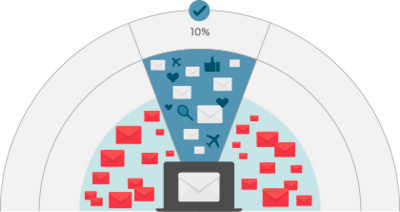
Spam is any form of unrequested communication sent in bulk. Depending on the content of the message, there are two main types – Unsolicited Bulk Emails (UBE) and Unsolicited Commercial emails (UCE).
If the email or message is unsolicited and deceptive, it is probably spam. One of the most common ways to spread unsolicited content is through botnets – large networks of robots or infected “zombie” devices. Chain letters and hoaxes are also considered to be spam, although these differ in that they are usually passed on by people with good intentions.
Any fan of the British comedy television show Monty Python probably already knows where the term comes from. In the show's 1970 ‘Spam’ sketch, two guests are ordering a meal in a greasy-spoon café and notice that nearly every dish on the menu contains SPAM® – a type of canned meat. Even though one of them doesn’t want SPAM in her meal, it soon becomes clear the ingredient is almost impossible to avoid – much like the unsolicited email messages.

If the email, message, or any other form of bulk communication is unsolicited and deceptive, then it probably is spam.
Trojan Horses are similar to the Trojan Horse known from ancient Greco-Roman tales. These Trojan virus hide their true function, often disguising themselves as legitimate software, in order to gain unauthorised access to a device. After reaching the targeted machine, they often employ various techniques to be executed by the user or by other software on the affected system.
Zombies are computers connected to the internet that have been compromised by a hacker, computer virus or trojan horse program. These are then used to perform malicious tasks under remote direction. Botnets of zombie computers are often used to spread e-mail spam and launch denial-of-service attacks (DOS attacks).
Phishing is an email scam in which the criminal impersonates a trustworthy entity to obtain sensitive data from the user.
Scams are fraudulent methods used to obtain money or personal details such as a credit card number or national insurance number. Scammers prey on others with deception through the buying and selling of illegitimate goods and services, fake charities, dating websites and threats/extortion.
Email spam can waste your time and become incredibly annoying. Thankfully, there are a few methods for limiting email spam from clogging up your inbox. One of the best ways to avoid junk email is to use trustworthy anti spam software, this will automatically move spam emails into your junk folder.
You can also reduce the number of spam emails you receive by clicking unsubscribe at the bottom of any messages you no longer wish to subscribe to. Another option is to report any spam emails as junk in your inbox so they are immediately moved over. You can also flag any phishing scams to help stop these intrusive emails.
If you must share your email address publicly, edit its format to make it harder for spammers to find. For example, writing it in a different way or sharing it as an image rather than a link.
Last but not least, use a reliable anti-spam solution.
The first spam email campaign was observed in 1978, landing messages in the inboxes of nearly 400 (or 15% of all) users connected to the internet’s predecessor, Advanced Research Projects Agency Network (ARPANET). However, after receiving a great deal of negative feedback, this form of marketing was abandoned.
However as the internet grew to global proportions, so did spam. Unfortunately spam didn’t just spread unsolicited ads, but also phishing links and other fraudulent content, as well as dangerous malware families, making it a serious security.
This prompted Cybersecurity vendors and software developers to create anti spam solutions, capable of filtering this kind of communication. Legislators also came up with anti spam laws that made sending spam illegal and prosecutable.
In 2008, McColo, a California-based hosting provider was shut down due to “unsolicited commercial email (UCE)” messages. It is estimated that McColo’s servers were accountable for three-quarters of all spam messages sent worldwide at that time.
Powerful and easy-to-manage protection that blocks scams, encrypts sensitive data, and secures folders and online transactions. Includes integrated VPN for enhanced privacy. Secures Windows, macOS, Android and iOS devices.