What if I told you there was a law on the books in the nation's most populous state set to affect thousands of businesses across the country, with stiff financial penalties and an effective date only months away—and almost half of business leaders have never even heard of it?
It may seem implausible, but that’s the reality of the California Consumer Privacy Act (CCPA), California's sweeping privacy legislation set to take effect Jan. 1, 2020. Yes, in five months.
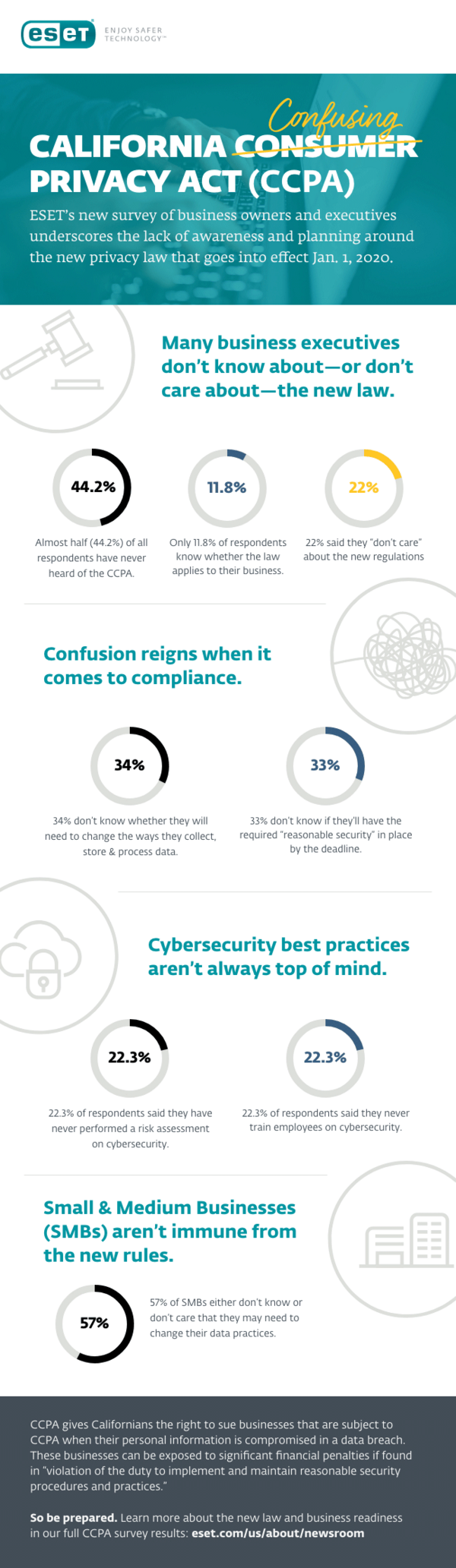
A new survey we conducted demonstrates that confusion reigns in the business community.
Almost half of the business leaders surveyed (44.2%) have never heard of the law. I wonder if this has something to do with the name—an executive in South Carolina might, at first glance, consider a law that states “California” in its title may well be for California only. But think again—the law applies to all businesses that interact with California residents, regardless of where the business is located.
Privacy legislation can seem complex, which may be why only 11.8% of business leaders said they know whether they need to comply. In reality, though, the criteria on whether you need to comply are relatively simple. Your business only needs to do business with California residents and satisfy one of the following:
- Have annual gross revenues above $25 million
- Handle data of 50k+ consumers, households or devices annually
- Derive 50% or more of annual revenue from selling personal information
Regardless of where your business is located in the world, if you match one of these criteria, you will need to comply.
Our survey showed, however, that about a third (34%) don’t know if they’ll need to change their data handling processes. The true percentage may be higher given the percentage of business leaders who have not even heard of CCPA.
Crucially, the implications of the law for security are even less well understood.
The new legislation says a penalty for breaches can arise from a “violation of the duty to implement and maintain reasonable security procedures and practices.” Data breach victims can sue for damages from $100-$750 per incident or actual damages, whichever is greater.
Despite the financial risk, our survey found that 33% don’t know if they’ll have “reasonable security” in place as of January 1, when the legislation comes into effect.
Although the “reasonable” standard is not specifically spelled out in the law, ESET will be releasing guidance for companies to begin assessing their security profile, identifying gaps and creating a reasonable security roadmap and implementing it.
What is clear is that businesses need to focus on implementing defensive mechanisms, processes and procedures to ensure they are considered to be adhering to reasonable security requirements to protect the personal information belonging to California residents.
There will be no excuse for non-compliance. If you have not already done so, then start a project or working group to ascertain whether you need to comply—and if you do, create a plan to achieve it.