Latest ESET white paper puts Internet Information Services web server threats under the microscope. Three of the discovered families — IIStealer, IISpy and IISerpent — are highlighted to show how IIS malware is being used for cybercrime, cyberespionage and SEO fraud.
BRATISLAVA, MONTREAL — August 6, 2021 — ESET researchers have discovered a set of 10 previously undocumented malware families, implemented as malicious extensions for Internet Information Services (IIS) web server software. Targeting both government mailboxes and e-commerce credit card transactions, as well as aiding in malware distribution, this diverse class of threats operates by eavesdropping on and tampering with the server’s communications. At least five IIS backdoors have been spreading through server exploitation of Microsoft Exchange email servers in 2021, according to ESET telemetry and the results of additional internet-wide scans that ESET researchers performed to detect the presence of these backdoors.
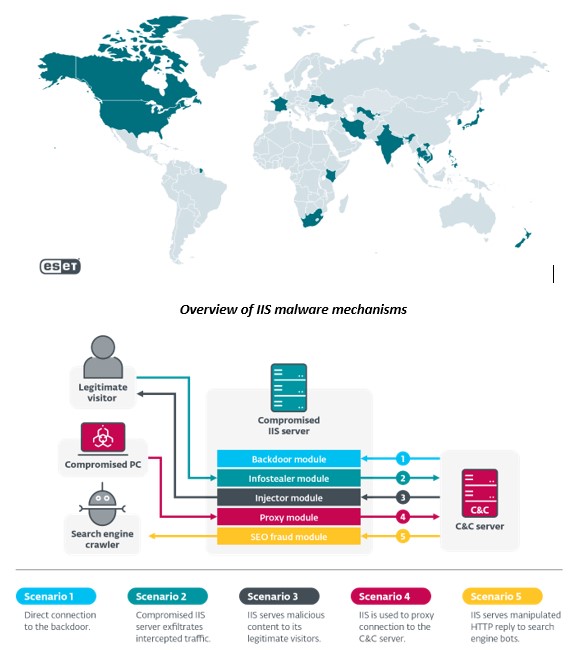
Among the victims are governments in Southeast Asia and dozens of companies belonging to various industries located mostly in Canada, Vietnam and India, but also in the US, New Zealand, South Korea and other countries.
Today, ESET Research is publishing the white paper “Anatomy of native IIS malware” and launching a series of blogposts on the most notable of the newly discovered threats: IIStealer, IISpy and IISerpent. These will be published on WeLiveSecurity starting today and following through to August 11, 2021. The findings of ESET’s IIS malware research were first presented at Black Hat USA 2021 and will also be shared with the community at the Virus Bulletin 2021 conference on October 8, 2021.
IIS malware is a diverse class of threats used for cybercrime, cyberespionage and SEO fraud — but in all cases, its main purpose is to intercept HTTP requests incoming to the compromised IIS server and affect how the server responds to (some of) these requests. “Internet Information Services web servers have been targeted by various malicious actors, for cybercrime and cyberespionage alike. The software’s modular architecture, designed to provide extensibility for web developers, can be a useful tool for attackers,” says ESET researcher Zuzana Hromcová, author of the paper.
ESET has identified five main modes in which IIS malware operates:
- IIS backdoors allow their operators to remotely control the compromised computer with IIS installed.
- IIS infostealers allow their operators to intercept regular traffic between the compromised server and its legitimate visitors and steal information such as login credentials and payment information.
- IIS injectors modify HTTP responses sent to legitimate visitors to serve malicious content.
- IIS proxies turn the compromised server into an unwitting part of the command and control infrastructure for another malware family.
- SEO fraud IIS malware modifies the content served to search engines to manipulate SERP algorithms and boost the ranking for other websites of interest to the attackers.
“It is still quite rare for security software to run on IIS servers, which makes it easy for attackers to operate unnoticed for long periods of time. This should be disturbing for all serious web portals that want to protect their visitors’ data, including authentication and payment information. Organizations that use Outlook on the web should also pay attention, as it depends on IIS and could be an interesting target for espionage,” explains Hromcová.
ESET Research offers several recommendations that can help mitigate against IIS malware attacks. These include using unique, strong passwords and multifactor authentication for the administration of IIS servers; keeping the operating system up to date; using a web application firewall and endpoint security solution for the server; and regularly checking the IIS server configuration to verify that all installed extensions are legitimate.
Along with the white paper, ESET will publish shorter blogposts derived from the paper from August 6 through August 11, 2021:
- Anatomy of native IIS malware (August 6, 17:00 CEST) — an extensive white paper published along with a summary blog post.
- IIStealer: A server-side threat to e-commerce transactions (August 6, 17:00 CEST) — a blog post that looks at a malicious IIS extension (trojan) that intercepts server transactions to steal credit card information.
- IISpy: A complex server-side backdoor with anti-forensic features (August 9, 11:30 CEST) — a blog post about a malicious IIS extension (backdoor) capable of securing long-term espionage on compromised servers.
- IISerpent: Malware-driven SEO fraud as a service (August 11, 11:30 CEST) — a blog post that describes a malicious extension (server-side trojan) used to manipulate page rankings for third-party websites.
For more technical details about these IIS threats, read the introductory blog post “Anatomy of native IIS malware” and the white paper on WeLiveSecurity. From August 6 to August 11 you can read the follow-up blogposts about IIStealer, IISpy and IISerpent[A1] . Make sure to follow ESET Research on Twitter for the latest news from ESET Research.
Victims of native IIS backdoors spread via the Microsoft Exchange Server ProxyLogon vulnerability chain
About ESET
For more than 30 years, ESET® has been developing industry-leading IT security software and services to protect businesses, critical infrastructure and consumers worldwide from increasingly sophisticated digital threats. With solutions ranging from endpoint and mobile security to encryption, multi-factor authentication and endpoint detection and response, ESET’s high-performing, easy-to-use products unobtrusively protect and monitor 24/7, updating defenses in real time to keep users safe and businesses running without interruption. Evolving threats require an intelligent IT security company that enables the safe use of technology. This aim is backed by ESET’s R&D centers worldwide, working in support of our shared future. For more information, visit www.eset.com or follow us on LinkedIn, Facebook and Twitter.