ULTIMATE MAIL SECURITY FOR BUSINESS
ESET PROTECT Mail Plus
Multilayered email protection with zero-day threat defense.
Included modules
Included modules
Protect your users and their email, the most exploited threat vector, with multilayered antispam, anti-phishing and host server protection technology.
Protection against ransomware and new, never-before-seen threats types that uses adaptive scanning, machine learning, cloud sandboxing and in-depth behavioral analysis.
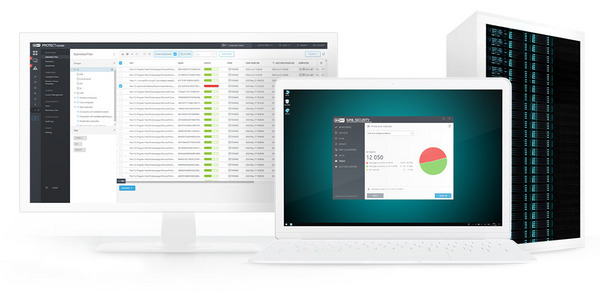
Single-pane-of-glass remote management for visibility to threats, users and quarantined items.
Comprehensive rule system allows administrators to define email filtering conditions and actions to take with filtered emails. This means more time spared to focus on other critical business tasks.
Advanced Threat
Defense Proactive cloud-based prevention against ransomware or never-before-seen threat types with autonomous remediation capabilities.
Learn more
Mail Server Security An additional layer of security, protecting Exchange email servers from threats entering the network on top of the standard endpoint and file server protection.
Features advanced anti-phishing, anti-malware, and anti-spam combined with cloud-powered proactive threat defense. Provides you with robust quarantine management and rule definition/filtering system.
Prevents ransomware and other email-borne attacks without compromising email's speed.
Learn more
Explore and learn from our library of demos
No sign-up or installation required – just click and watch
Actions such as create an exclusion, submit files for further analysis or initiate a scan are available within a single click.
Users are sent emails when messages have been quarantined and can handle it themselves. Administrators can decide to delete or release messages from a central quarantine.
Use predefined notification or create your own. The notification system features a full “what you see is what you get” editor.
Trustworthy Endpoint Security That Simply Works
RGRaja G., Senior Project Manager
"I particularly like how easy it is to deploy across Windows, Mac, and servers using ESET PROTECT. It’s a clean console and you can easily view your environment. I like the patch management, device control and sandbox analysis because it really allows me to calibrate the security policies."
One of the best client email protection
JBJon B., System Admin
"It is a robust centralized security management platform ideal for business needing scalable endpoint protection with strong threat detection, cross-platform support (Windows, macOS, Linux and Android) and efficient automation."
Reliable Solution for Strengthening Enterprise Security
OFOwen F., Information Security Officer
"ESET PROTECT gives me centralized visibility across the entire organization. It lets me see endpoint health, vulnerabilities, and active incidents from one place. The reporting features also help me present clear security insights to leadership without needing extra tools."
Based on customer reviews, through G2 Crowd surveys that asked ESET business customers to rate their experiences using ESET PROTECT solutions.

Protected by ESET since 2017
More than 9,000 endpoints
Protected by ESET since 2019
1,200 devices & 2,700 mailboxes
Protected by ESET since 2016
More than 32,000 endpoints
ISP security partner since 2008
2 milion customer base
Supported mail servers
Note: Exact features and functionality may vary depending on the server version used.
Remote management platform is available as cloud-based or on-premises deployment. No need to buy or maintain additional hardware, reducing the total cost of ownership.
Transfer your subscription to another server
You can transfer a valid ESET subscription from the original server to a completely new one.
Phishing attacks and fake websites trying to steal login credentials are on the rise. See how ESET can help.
How ESET leading-edge technology goes far beyond the capabilities of basic antivirus?
Find out what industry analysts are saying about ESET, and how we perform in independent tests.
4
0
RECOMMENDED
Endpoint, cloud and data security preventing ransomware Explore more
Cyber security risk management and XDR. Explore more
All-in-one protection with XDR to prevent breaches. Explore more
All-in-one protection with premium 24/7 MDR service. Explore more
Mobile devices
protection for free
Mobile devices
protection for free
Mobile devices
protection for free
Mobile devices
protection for free
Price available on request
Leave us your contact details to receive an offer tailored for your company's needs.
Price available on request
Leave us your contact details to receive an offer tailored for your company's needs.
Price available on request
Leave us your contact details to receive an offer tailored for your company's needs.
Console Unified cybersecurity platform interface providing superior network visibility and control. Available as cloud or on-prem deployment.
Modern Endpoint Protection Advanced multilayered protection for computers and smartphones powered by unique ESET LiveSense technology.
Next-Generation Antivirus Next-gen antivirus protection for business that helps you stay ahead of known and emerging threats with our AI-native, prevention-first approach.
Device Control Enables restriction of unauthorized devices, such as USB flash drives or CDs, to prevent access to sensitive data, mitigating the risk of data breaches and insider threats.
Anti-Phishing Safeguards sensitive company data from phishing, spear phishing and other types of social engineering attacks.
Ransomware Remediation Provides comprehensive rollback through seamless, automated file restoration from secure backups. Minimize the business impact of a ransomware attack and never pay a ransom again.
Server Security Real-time protection for your company’s data passing through all general servers.
Mobile Threat Defense Robust security for all Android and iOS mobile devices within the organization. Equip your mobile fleet with Antimalware, Anti-Theft and MDM capabilities.
Full Disk Encryption Robust encryption solution for system disks, partitions or entire devices to achieve legal compliance.
Advanced Threat Defense Proactive cloud-based prevention against ransomware or never-before-seen threat types with autonomous remediation capabilities.
Cloud Workload Protection Reinforce your cloud virtual machines (VMs) with AI-powered, multilayered protection to prevent breaches and minimize downtime.
Cloud App Protection Advanced protection for Microsoft 365 and Google Workspace apps, with additional proactive threat defense.
Available as on demand upgrade providing additional protection layer. Click here and contact a sales person to receive an offering tailored to your individual needs. No commitment.
Available as on demand upgrade providing additional protection layer. Click here and contact a sales person to receive an offering tailored to your individual needs. No commitment.
Extended Detection and Response Additional platform capability to proactively detect threats, effectively identify anomalous behavior in the network and realize timely remediation, preventing breaches and business disruption.
ESET Inspect, the XDR-enabling cloud-based tool, provides outstanding threat and system visibility, allowing risk managers and security professionals to perform fast and in-depth root cause analysis and immediately respond to incidents.
Mail Server Security An additional layer of security, protecting Exchange email servers from threats entering the network on top of the standard endpoint and file server protection.
Features advanced anti-phishing, anti-malware, and anti-spam combined with cloud-powered proactive threat defense. Provides you with robust quarantine management and rule definition/filtering system.
Prevents ransomware and other email-borne attacks without compromising email's speed.
Available as on demand upgrade providing additional protection layer. Click here and contact a sales person to receive an offering tailored to your individual needs. No commitment.
Available as on demand upgrade providing additional protection layer. Click here and contact a sales person to receive an offering tailored to your individual needs. No commitment.
Vulnerability & Patch Management Actively track & fix vulnerabilities in operating systems and applications across all endpoints.
This add-on can be purchased with, or on top of this ESET PROTECT tier. Click here and contact a salesperson to receive an offering tailored to your individual needs. No commitment.
This add-on can be purchased with, or on top of this ESET PROTECT tier. Click here and contact a salesperson to receive an offering tailored to your individual needs. No commitment.
Multi-Factor Authentication Single-tap, mobile-based multi-factor authentication that protects organizations from weak passwords and unauthorized access.
Available as on demand upgrade providing additional protection layer. Click here and contact a sales person to receive an offering tailored to your individual needs. No commitment.
Available as on demand upgrade providing additional protection layer. Click here and contact a sales person to receive an offering tailored to your individual needs. No commitment.
ESET AI Advisor ESET's proprietary generative AI cybersecurity assistant helps with interactive risk identification, analysis, and response
Available as on demand upgrade providing additional protection layer. Click here and contact a sales person to receive an offering tailored to your individual needs. No commitment.
Available as on demand upgrade providing additional protection layer. Click here and contact a sales person to receive an offering tailored to your individual needs. No commitment.
MDR Ultimate Service End-to-end digital security with proactive threat hunting.
Available as on demand upgrade providing additional protection layer. Click here and contact a sales person to receive an offering tailored to your individual needs. No commitment.
Available as on demand upgrade providing additional protection layer. Click here and contact a sales person to receive an offering tailored to your individual needs. No commitment.
Premium Support Ultimate Flawless deployment, operation and incident resolution. Leave it all to us.
Available as on demand upgrade providing additional protection layer. Click here and contact a sales person to receive an offering tailored to your individual needs. No commitment.
Available as on demand upgrade providing additional protection layer. Click here and contact a sales person to receive an offering tailored to your individual needs. No commitment.
Available as on demand upgrade providing additional protection layer. Click here and contact a sales person to receive an offering tailored to your individual needs. No commitment.
Cybersecurity Awareness Training Prevention-first education to ensure employees are the foundation of an organization’s digital security.
Available as on demand upgrade providing additional protection layer. Click here and contact a sales person to receive an offering tailored to your individual needs. No commitment.
Available as on demand upgrade providing additional protection layer. Click here and contact a sales person to receive an offering tailored to your individual needs. No commitment.
Available as on demand upgrade providing additional protection layer. Click here and contact a sales person to receive an offering tailored to your individual needs. No commitment.
Available as on demand upgrade providing additional protection layer. Click here and contact a sales person to receive an offering tailored to your individual needs. No commitment.
Threat Intelligence Get in-depth, up-to-date global knowledge about specific threats and attack sources.
Available as on demand upgrade providing additional protection layer. Click here and contact a sales person to receive an offering tailored to your individual needs. No commitment.
Available as on demand upgrade providing additional protection layer. Click here and contact a sales person to receive an offering tailored to your individual needs. No commitment.
Available as on demand upgrade providing additional protection layer. Click here and contact a sales person to receive an offering tailored to your individual needs. No commitment.
Available as on demand upgrade providing additional protection layer. Click here and contact a sales person to receive an offering tailored to your individual needs. No commitment.
Not sure what solution is best for your business?
Renew, upgrade or add devices to your existing ESET subscription.
Enter ESET PROTECT Hub to manage your purchased subscriptions.
Install your purchased protection on additional devices.
All ESET products include free technical support in your language.