ESET PROTECT MDR/XDR
Provides continuous monitoring, detection, and response across your entire environment, identifying suspicious activity and responding in real time.
Strengthen Security Across People, Devices, and Data
Continuous verification, least-privilege access, and an assume-breach mindset are the pillars of a zero trust security approach. ESET PROTECT brings this strategy to life with unified protection, strong identity controls, and 24/7 managed detection and response to close gaps and strengthen resilience.
Hybrid work, cloud services, and remote collaboration have made modern IT environments more distributed and complex.
Users, devices, and data now operate far beyond a single network, making traditional security boundaries increasingly ineffective.
Attackers are no longer focused solely on networks.
They exploit compromised identities, unmanaged devices, and blind spots in visibility to move laterally and remain undetected, bypassing legacy perimeter-based defenses.
Zero Trust takes a data-driven approach to security. Every access request is continuously verified, regardless of location, user, or device.
This reduces exposure and enables adaptive protection across the entire environment, guided by clear Zero Trust principles.
Treat all networks as untrusted, whether on-premises, at home, or in the cloud.
Grant only the access needed for only as long as it’s needed.
Always be ready to detect, contain, and respond quickly to security breaches to minimize their impact.
A successful zero trust architecture relies on the right combination of tools and policies, integrating strong identity controls, continuous monitoring, and clear access rules to reduce risk, protect data, and enable secure business operations.
Provides continuous monitoring, detection, and response across your entire environment, identifying suspicious activity and responding in real time.
Offers deep visibility, behavior analysis, and continuous verification of endpoints.
Delivers cloud-based, real-time analysis of new and unknown threats.
Strengthens proactive verification by identifying and blocking attacker infrastructure and evolving threats.
Provides strong multifactor authentication (MFA) to verify users and protect against credential theft.
Ensures only authorized users can access sensitive data on devices.
Enables centralized, role-based access management and consistent policy enforcement across endpoints, servers, and mobile devices.
24/7 managed detection and response with expert analysis, proactive threat hunting, and guided remediation.
Multilayered endpoint defense to contain and stop active threats.
Automatically identifies and remediates exploitable weaknesses.
Protects collaboration platforms from phishing, malware, and business email compromise.
ESET’s multilayered, AI-powered cloud protection covers hybrid, multi-OS environments, reducing attack surfaces across endpoints, servers, mail systems, mobile devices, and cloud apps. Hardened browsers and specialized controls block remote desktop protocol (RDP) attacks before they begin.
Enforce identity trust with multifactor authentication (MFA) that prevents account takeover and unauthorized access. Pair with full disk encryption to lock down sensitive data on laptops and workstations, protecting users and admins alike.
Automated vulnerability and patch management keeps systems current and safeguarded from known exploits. ESET Cloud Office Security protects against business email compromise and phishing.
Centralized policies applied from a unified console ensure consistent, role-based access control across endpoints, servers, and mobile devices.
Minimize detection and response times to as little as 6 minutes with ESET MDR, our 24/7 managed detection and response service. Backed by ESET XDR, you gain full visibility into threats, behaviors, and anomalies across your IT environment.
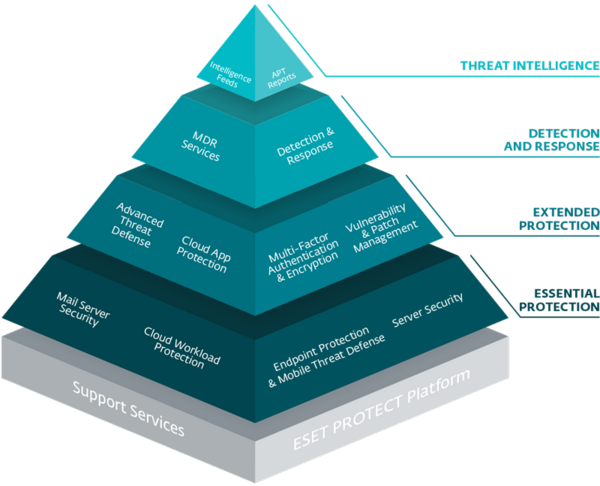
The model allows you to identify where your IT security is at right now and the level of protection that your business really needs.
Antivirus-Level
No Monitoring
Lax Policy
Unmanaged Endpoints
Small Office / HO
Endpoint Protection
Phishing / Spam Protection
Firewall
Device / Web Policy
Managed Endpoints
Small Office / SMB
Data Encryption
Multi-Factor Authentication
Cloud Sandbox
Adaptive Policy
Managed Endpoints
Small Office to SMB
Incident Detection
Threat Monitoring
Isolation (IoC)
Evolutionary Policy
+ Forensics
SMB to Enterprise
Threat Intelligence APT Investigation Report
Preventive Policy
+ SIEM / SOC
Enterprise / KRITIS
Start with proactive, cloud-based endpoint protection featuring advanced threat defense to stop targeted and never-before-seen attacks. Secure identities and data with encryption and MFA.
Add ESET XDR for advanced detection, behavioral analysis, and accelerated investigations to limit lateral movement.
Choose ESET MDR for continuous monitoring, expert triage, and guided response. Our analysts tune detections, enforce policy, and strengthen defenses in real time.
Use ESET Threat Intelligence (ETI) to anticipate attacker infrastructure, proactively update defenses, and fine-tune zero trust policies.

Zero trust is a security model that assumes no user, device, or connection is trusted by default. Every request is continuously authenticated, authorized, and verified before access is granted.
Zero trust architecture (ZTA) is a framework defined by NIST SP 800-207. It focuses on identity, device health, continuous monitoring, access controls, and real-time decision making instead of traditional network perimeters.
According to the CISA Zero Trust Maturity Model, the five pillars are:
The foundational principles that guide zero trust design are:
• Continuous Verification –Validate user identity, device health, and contextual factors throughout every session and transaction—never rely on a single initial authentication.
• Least-Privilege Access –Provide only the access required for the task, and review permissions regularly.
• Assume Breach –Incidents are inevitable. Build vigilance through layered controls, processes, and monitoring.
ZTNA provides secure, identity-based access to internal applications without exposing them to the public internet. Access is granted based on user identity, device posture, and contextual risk, not network location.
Implementation typically follows these steps:
Zero trust can be challenging because it requires mapping data flows, redefining access controls, verifying device posture, and continuously monitoring activity. Legacy environments, distributed teams, and limited visibility increase complexity. Platforms like ESET simplify this with integrated MFA, endpoint protection, XDR, and MDR.
Yes. Zero trust aligns with major regulatory frameworks requiring identity protection, access control, encryption, continuous monitoring, and incident response. It also strengthens eligibility for cyber insurance, which is now critical in high-risk industries like financial services, healthcare, and technology.
Zero trust is a security strategy, not a single product. It succeeds when technology and strategy work together by leveraging tools like MFA, encryption, EDR/XDR, mobile device management, and policy engines to enforce continuous verification and least-privilege access.
Done right, zero trust can improve user experience by providing the right access at the right time, with contextual verification and minimal friction.
Zero trust requires a new way of thinking about security, focusing on protecting data and ensuring that only the right people and devices have access. Setting up additional security checks and monitoring users, systems, and data can take time and effort initially. Most organizations, however, begin producing value within weeks by hardening identity and device posture, then expand coverage and automation over subsequent quarters. With the right tools and automation, security teams gain more control, reduce risks more effectively, and make the environment easier to manage over time.
Zero trust combines three guiding principles—continuous verification, least-privilege access, and assume breach—with comprehensive coverage across key areas of your environment:
Together, these principles and areas create a resilient, adaptive security framework that reduces risk, strengthens visibility, and ensures consistent protection across your organization.